Definition & Meaning
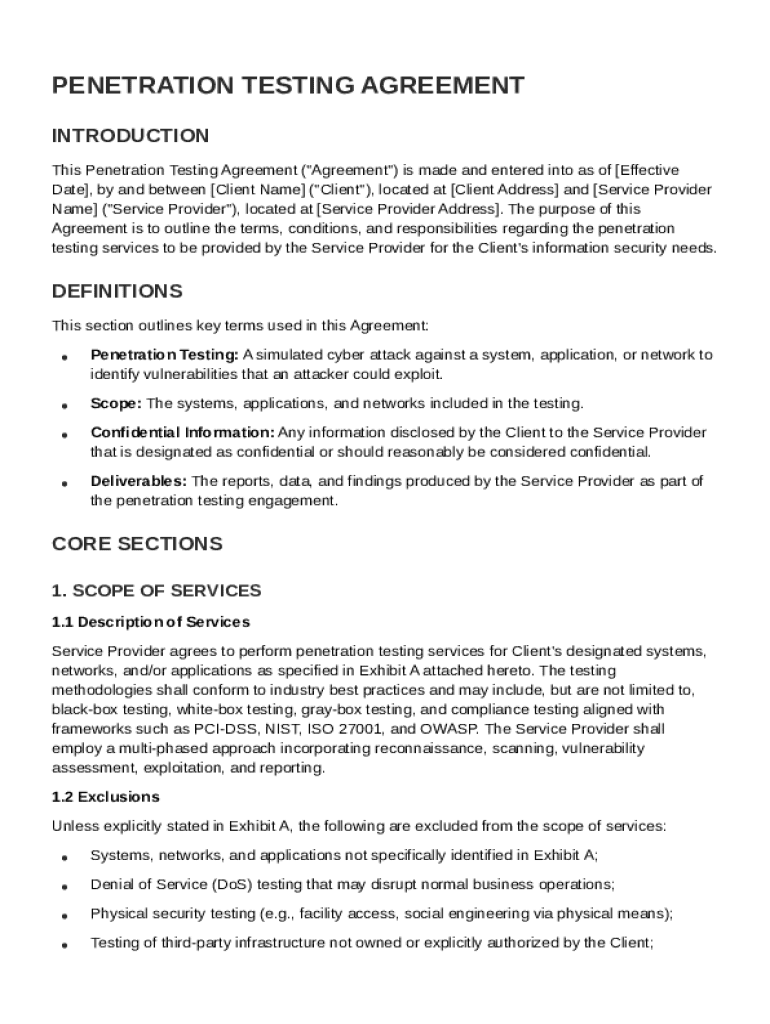
The "Penetration Testing Agreement Template" is a structured legal document used to outline the terms and conditions between a service provider and a client engaging in penetration testing services. This template serves a crucial role in defining the scope, objective, and confidentiality agreements associated with penetration testing. Such testing aims to uncover vulnerabilities within a client's systems, applications, or networks. The agreement ensures both parties understand their responsibilities, as well as the methodologies and deliverables involved.
- Purpose: To protect both parties involved and clarify the testing boundaries.
- Scope: Covers what systems and applications are included in the testing.
- Deliverables: Lists what the client should expect, like detailed vulnerability reports and remediation strategies.
Key Elements of the Penetration Testing Agreement Template
The template is built around several critical components that form the backbone of the agreement. Each element plays a significant role in ensuring that the penetration testing process is effective and legally sound.
- Scope of Services: Defines which systems and applications will be tested and any particular exclusions.
- Responsibilities: Outlines the duties of both the client and the service provider, ensuring clarity and accountability.
- Confidentiality: Establishes the protocols for handling sensitive information discovered during testing.
- Reporting Methodologies: Describes how findings will be documented and communicated to the client.
- Payment Terms: Specifies the compensation structure for the services provided.
- Liability and Indemnity: Details any limitations on the service provider's liability and indemnity provisions.
- Termination Conditions: Provides scenarios under which the contract can be terminated by either party.
Legal Use of the Penetration Testing Agreement Template
Within the United States, the Penetration Testing Agreement template is used as a legal instrument to solidify the contractual relationship between the service provider and the client. Legal compliance is integral to its framework to avoid any future disputes.
- Governing Law: The agreement specifies the jurisdiction which will govern any legal issues that may arise.
- Compliance: Typically requires adherence to industry standards and best practices for ethical hacking and security testing.
- Enforcement: The agreement ensures that any breaches can be litigated under the specified state laws.
Steps to Complete the Penetration Testing Agreement Template
Completing the template requires meticulous attention to detail, as accuracy impacts both the efficacy and legality of the agreement. Here are the steps usually involved:
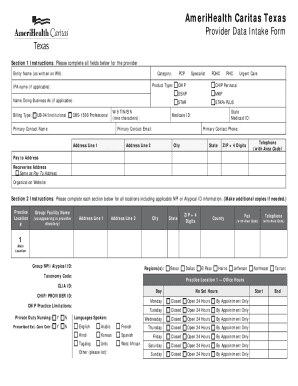
- Identify the Parties: Include the full legal names and contact information for both the service provider and client.
- Define Objectives: Clearly specify the objectives of the penetration testing process.
- Delimit the Testing Environment: State exactly which systems, networks, and applications are subject to testing.
- Specify Timeframes: Agree upon and document the testing and reporting timelines.
- Outline Confidentiality Measures: Include clauses that ensure all discovered vulnerabilities are kept confidential.
- Determine Compensation: Clearly state the payment terms, including due dates and invoicing procedures.
- Agree on Liability Limits: Set out the limitations on the service provider’s liability to safeguard both parties.
Important Terms Related to Penetration Testing Agreement Template
Understanding critical terminology assures that both parties are fully informed and prepared for potential scenarios during the testing:
- Vulnerability: Possible points of weakness in the client's system.
- Remediation: Strategies to rectify identified vulnerabilities.
- Ethical Hacking: Controlled procedures for legally testing a system’s defenses.
- Test Environment: The specific systems and data isolated for testing.
- Data Breach: Incident where sensitive data is accessed or stolen.
Examples of Using the Penetration Testing Agreement Template
In practice, organizations leverage this template to secure their digital assets through tailored penetration testing. Here are some scenarios:
- Financial Institutions: Used to assess the security of online banking platforms.
- Healthcare Providers: Employed to protect patient data from cyber threats.
- E-commerce Companies: Ensures checkout processes are secure from intrusions.
Who Typically Uses the Penetration Testing Agreement Template
The template is predominantly utilized by a diverse group engaged in digital security:
- IT Security Firms: As service providers offering specialized testing services.
- Corporate IT Departments: To guarantee in-house compliance with security standards.
- Legal Teams: To draft protective clauses related to data privacy and liability.


Software Compatibility
Drafting, editing, and reviewing the Penetration Testing Agreement can be conveniently managed via various software solutions:
- DocHub: Offers intuitive tools for document collaboration and signing in both PDF and DOC formats.
- Microsoft Word: Commonly used for drafting and editing the initial agreements.
- Google Docs: Facilitates real-time collaboration among teams during drafting.
Being aware of these specifics ensures comprehensive and legally secure agreements that are actionable and protective.