Definition & Meaning
The Privacy Impact Assessment (PIA) for the VA IT System is a thorough examination and evaluation process utilized by the Veterans Administration (VA) to manage privacy risks associated with its Information Technology systems. It is a formal document that outlines the system's purpose, functions, and how it collects, handles, and protects personal data. Beyond merely identifying risks, the PIA also includes mitigation strategies to ensure compliance with federal regulations and secure sensitive information like veterans' personal details. This assessment is crucial for enhancing transparency and accountability, contributing to trust between the VA and the individuals it serves.
Key Elements of the Privacy Impact Assessment for the VA IT System
The PIA comprises several critical components designed to evaluate and manage the privacy implications of the VA's IT systems:
-
Purpose and Usage: It clarifies the system's objectives and how it aligns with the broader goals of financial management and compliance with federal regulations.
-
Information Collection Practices: Details on what data is collected, the sources of this data, and the intended use of the information.
-
Legal Framework: Outlines the legal authorities governing data collection and usage, ensuring that the system operates within legal boundaries.
-
Risk Assessment and Mitigation: Identifies potential privacy risks and outlines strategies to mitigate these risks, safeguarding personal data.
-
User Access Controls: Details security measures, including access controls to limit data access to authorized personnel only.
Steps to Complete the Privacy Impact Assessment for the VA IT System
Completing a PIA involves a systematic approach to ensure all potential risks are assessed and mitigated:
-
Identify the System Scope: Define what systems and data processes will be covered by the assessment.
-
Data Flow Mapping: Create diagrams to visualize data flow, including data inputs, storage, access, and exit points.
-
Risk Analysis: Assess potential risks involved in data handling and processing, focusing on factors like unauthorized access or data breaches.
-
Develop Mitigation Strategies: Propose solutions to address identified risks, focusing on enhancing data security and privacy.
-
Documentation: Compile findings into a comprehensive PIA report, including analysis, risk management strategies, and system details.
-
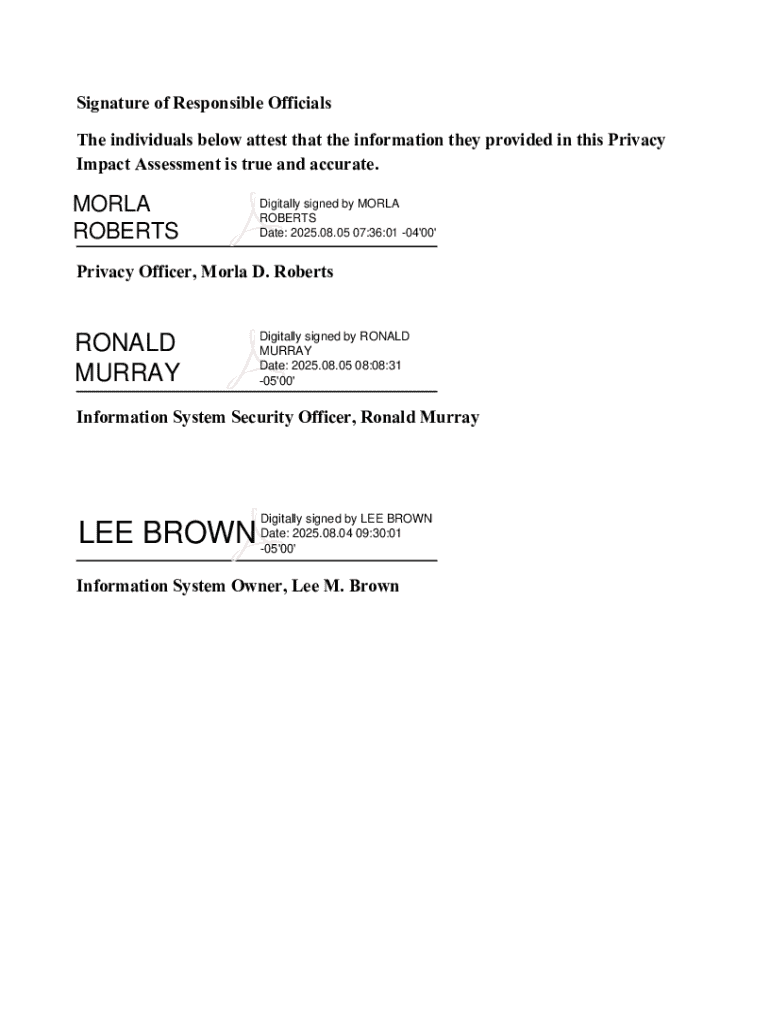
Review and Approval: Submit the assessment for review by relevant departmental staff and obtain formal approval.
How to Use the Privacy Impact Assessment for the VA IT System
Utilizing a PIA involves several key steps:
-
Evaluate System Changes: Use the PIA to assess any new risks introduced by changes or upgrades to the IT system.
-
Monitor Compliance: Regularly review PIAs to ensure ongoing compliance with privacy regulations and adapt to potential changes in legal requirements.
-
Educate Stakeholders: Share PIA findings with relevant parties, including system users and privacy officers, to promote awareness and understanding of privacy responsibilities.
-
Implement Controls: Use the assessment's findings to design and implement robust access controls, ensuring only authorized personnel can access sensitive information.
Legal Use of the Privacy Impact Assessment for the VA IT System
The PIA serves as a legal document supporting privacy compliance and risk management within the VA:
-
Regulatory Compliance: Ensures adherence to federal privacy regulations, such as the Privacy Act and the Federal Information Security Management Act (FISMA).
-
Accountability and Transparency: Acts as proof of due diligence in protecting sensitive information and responding to privacy concerns.
-
Internal and External Audits: Provides evidence during audits or investigations, confirming that the VA is managing privacy risks responsibly.
Who Typically Uses the Privacy Impact Assessment for the VA IT System
The PIA is used by various stakeholders within the VA:
-
Privacy Officers: Responsible for overseeing the protection of personal information and ensuring compliance with privacy laws.
-
IT Management Teams: Use the PIA to guide the design and implementation of secure IT systems.
-
Risk Management Professionals: Utilize the assessment to identify and mitigate data privacy risks.
-
Auditors and Regulators: Reference PIAs during audits to ensure the VA is meeting its privacy obligations.


Required Documents
Completing the PIA requires gathering key documents to inform the assessment:
-
System Design Documentation: Details the architecture and technical specifications of the IT system.
-
Data Inventory: A comprehensive list of data types collected by the system, including classifications and sources.
-
Legal Compliance Requirements: A catalog of relevant privacy laws and regulations that govern the system.
-
Previous PIAs and Risk Assessments: For context and reference on the system's historical compliance and risk posture.
Examples of Using the Privacy Impact Assessment for the VA IT System
Case studies underscore the practical application and benefits of PIAs:
-
System Upgrades at the VA: When the VA implemented enhancements to its financial management systems, PIAs helped identify and mitigate privacy risks associated with the new data processes.
-
Interdepartmental Data Sharing: For initiatives involving data exchanges between VA departments, PIAs ensured that privacy protocols were maintained across different networks and systems.
-
Audit Preparations: In preparation for federal audits, PIAs provided documented proof of the VA's adherence to privacy standards and its proactive risk management practices.