Understanding "702 Android Malware" and Its Implications
Definition and Structure of Android Malware
Android malware refers to malicious software specifically targeting devices running the Android operating system. It is designed to exploit vulnerabilities within Android's architecture, which includes a unique filesystem layout and specific security protocols. Android malware often targets both the system and user applications by leveraging Android's permissions and app management framework. Understanding the structure of Android malware is crucial in recognizing how it spreads and affects devices. Typically, this malware targets insecure permissions and exploits features such as app signing and system services.
Steps for Analyzing 702 Android Malware
- Initial Detection: The first step in analyzing Android malware like the "702 Android Malware" involves identifying unusual behavior on the device, such as rapid battery drain, slow performance, or unexpected data usage.
- Isolation: Isolate the suspected device from networks to prevent further spread.
- Reverse Engineering: Use reverse engineering techniques to examine the code and identify the malware's origin. This may involve using tools like Android Debug Bridge (ADB) and analyzing the system's startup processes.
- Permissions Audit: Review and analyze the app permissions to identify any unnecessary access that might indicate malicious intent.
- System Services Check: Examine the system services that the malware might be exploiting.
Legal Use and Ethical Considerations
Understanding the legal framework surrounding Android malware is crucial, as exploring or using malware without consent is illegal and unethical. Law enforcement and cybersecurity professionals may analyze malware like "702 Android Malware" under specific legal guidelines to improve security frameworks and protect user data. In the U.S., the Computer Fraud and Abuse Act provides a legal basis for addressing unauthorized access or use of computers and networks, including those affected by malware. Legal use cases are limited to authorized research, security enhancements, and educational purposes with strict adherence to privacy laws.
Key Elements and Components of the Malware
- Malicious Code: The core element of Android malware, which carries out unauthorized tasks on a device.
- Exploit Mechanism: Techniques used to bypass system security.
- Command and Control (C&C) Network: A server infrastructure the malware uses to receive commands from its creator.
- Data Exfiltration: The process of extracting data from the device without user consent.
- Persistence Mechanism: Strategies to ensure the malware remains on the device after reboots.
Who Typically Uses the 702 Android Malware?
The 702 Android Malware is typically utilized by malicious actors aiming to:
- Gain unauthorized access to personal data
- Manipulate device functions for fraudulent purposes
- Conduct espionage operations
- Develop further sophisticated attacks targeting vulnerabilities in systems, especially those in outdated Samsung devices, as highlighted in previous case studies


Examples of Malware in Action
- Data Theft: Instances where users notice encrypted data being sent out intermittently.
- Detailed Case Study: A situation where applications replicate themselves across devices via shared networks.
- Unauthorized Access: Cases where users experience loss of control over key applications on their phones.
Protecting Against Android Malware
To safeguard against Android malware such as the "702 Android Malware," consider these tips:
- Install reputable cybersecurity applications that can detect malware attacks in real-time.
- Regularly update your Android system and applications to patch known vulnerabilities.
- Be cautious when granting app permissions and ensure they are necessary for the app's function.
- Avoid downloading apps from untrusted sources or those offering too-good-to-be-true services, which can often be gateways for malware.
Software Compatibility and Systems
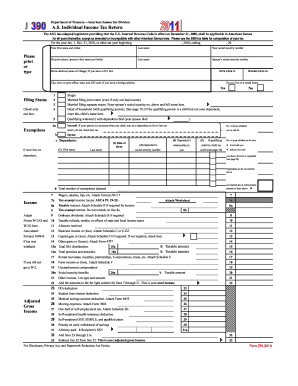
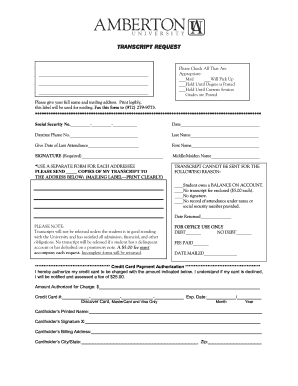
For analyzing and mitigating threats like the "702 Android Malware," integrating with advanced security systems compatible with platforms such as TurboTax or QuickBooks may offer streamlined solutions for businesses and individual users. These platforms often provide specific security settings to handle potential threats, which can be pivotal in managing sensitive data.
These sections provide comprehensive coverage of what needs to be known about the "702 Android Malware," focusing on detection, analysis, legal considerations, key components, user profiles, real-world examples, and protection strategies.