Definition and Meaning of National Key Point Registration
National Key Point Registration refers to a process by which specific sites deemed vital to the country's national security are officially recognized and protected. These sites, often critical infrastructure like military bases, nuclear plants, or energy facilities, require stringent security measures to prevent potential threats. The registration process ensures these sites comply with national security regulations and standards, safeguarding against espionage, terrorism, and other threats. Understanding the criteria and managing compliance is crucial for organizations responsible for such key points.
Steps to Complete the National Key Point Registration
-
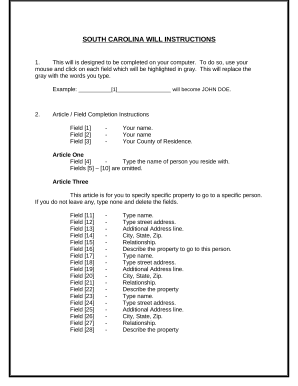
Preparation and Documentation: Gather the necessary documentation, including an application letter, certified copies of relevant certificates, identification documents, and payment of the applicable application fee. These ensure you meet initial eligibility requirements.
-
Application Submission: Complete the registration form with accurate information about the site, its significance, and security measures in place. Submit this alongside your prepared documentation to the designated government authority responsible for national security.
-
Review Process: Once submitted, the application undergoes a review process. The authority assesses the application's completeness, verifies supplied data, and evaluates the site's national security significance.
-
Site Inspection and Evaluation: In some cases, an onsite inspection may be conducted to evaluate the security measures and overall compliance with national guidelines.
-
Approval or Request for Additional Information: Based on the review and inspection, the authority either approves the registration, granting the site's national key point status, or requests additional information for clarity or documentation correction.
Required Documents for National Key Point Registration
Accurate completion of the national key point registration requires a comprehensive set of documents:
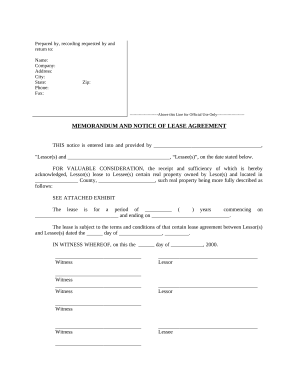
- Application Letter: A formal request detailing the need for registration and the significance of the site.
- Certificates and Approvals: Certified copies of any relevant certificates demonstrating compliance with national security protocols.
- Identification Documents: Certified copies of legal identification for the organization’s representatives involved in the registration.
- Application Fee Receipt: Proof of payment for the application fee, which varies depending on jurisdiction.
Ensuring all documents are correct and certified as needed can prevent delays or rejections in the registration process.
Legal Use of the National Key Point Registration
Registering a site as a national key point reflects legal compliance with national security laws. Such recognition ensures that:
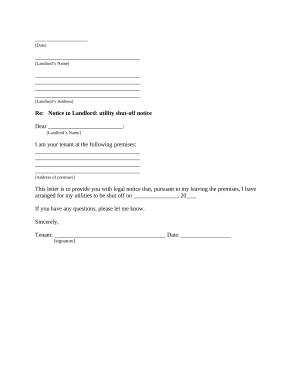
- Security Protocols: The site implements and maintains safety measures as mandated by national security legislation.
- Government Support: The site may receive government assistance and resources in maintaining security.
- Legal Protection: It provides legal protection, allowing for more decisive actions against potential threats or breaches.
These safeguards support the site's operational integrity and national safety contributions.
Importance of National Key Point Registration
Securing national key points through registration is crucial because:
- National Security: Protects sites vital to the nation’s operational stability and security.
- Prevents Terrorism: Mitigates risks of attack or sabotage on critical infrastructure.
- Regulatory Compliance: Ensures sites adhere to legal and security standards.
- Public Safety: Guarantees continued public access to essential services provided by these sites.
Registration indicates proactive measures in national security, reinforcing a site’s dedication to public and national safety.
Examples of National Key Point Registration Use
Several examples illustrate the role and importance of national key point registration:
- Military Installations: Protecting military bases ensures the security of defense operations and sensitive information.
- Energy Facilities: Nuclear or renewable energy plants require robust protection due to their role in national power supply.
- Telecommunication Hubs: Safeguarding communication centers prevents disruptions in essential communication networks.
These examples reveal how registration aligns with broader national security objectives by managing risks to critical infrastructure.
Application Process and Approval Time for National Key Point Registration
Initial Steps
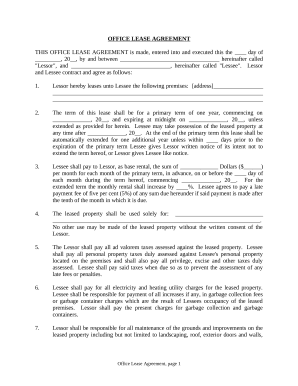
- Application Submission: Upon completing and compiling all required documentation, submit the application to the appropriate regulatory body.
- Review and Initial Feedback: Initial reviews provide feedback on submission completeness, highlighting missing elements.
Evaluation and Final Decision
- In-depth Review: A detailed evaluation of the site’s security setup and compliance mechanisms against national criteria.
- Processing Duration: While this varies by jurisdiction, typically expect processing to take several weeks to months, depending on complexity and application completeness.
Understanding these timelines helps manage expectations and plan site security enhancements accordingly.
Eligibility Criteria for National Key Point Registration
Certain criteria must be met to qualify a site as a national key point:
- Critical Infrastructure: Must serve a pivotal role in national security, economy, or public welfare.
- Security Risk Assessment: A thorough assessment indicating significant threat vulnerabilities in need of mitigation.
- Ownership and Management: Sites should have clearly defined management structures capable of implementing security measures.
Meeting these criteria is essential for a successful registration application, ensuring sites meet national security standards.