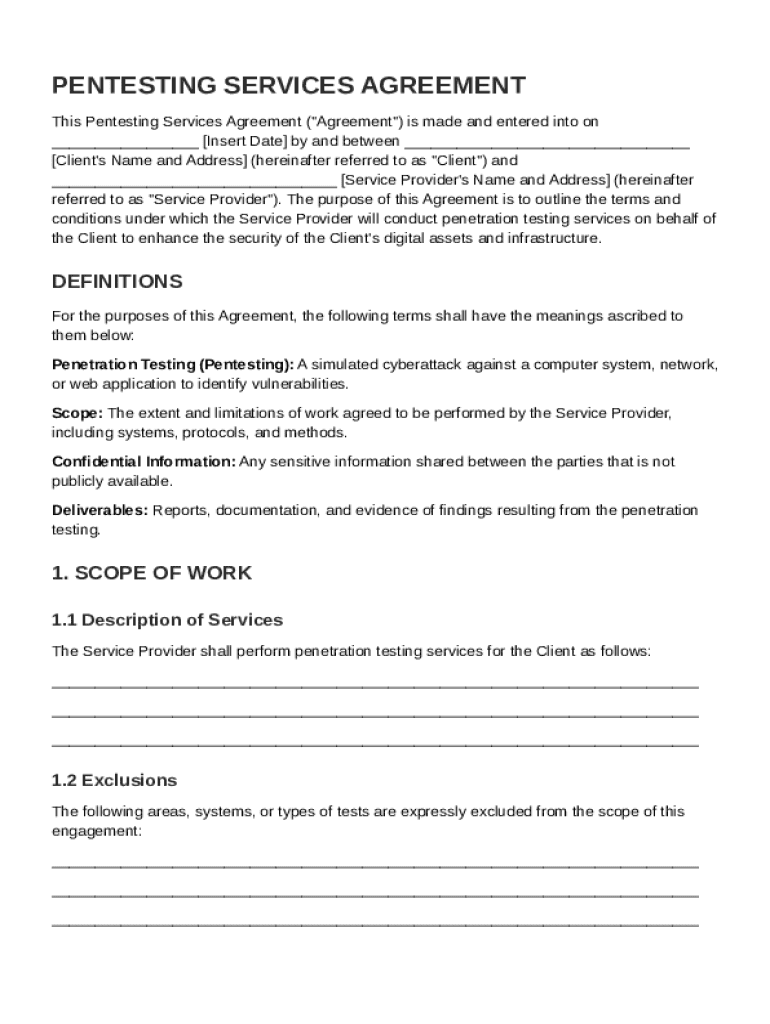
Definition & Meaning
A Pentest Contract Template serves as a formal agreement outlining the terms and conditions for conducting penetration testing on a client's digital infrastructure. This contract is crucial for defining the scope of the work, the responsibilities of both the service provider and the client, and the expected outcomes. The primary goal of the agreement is to enhance the security posture of the client's network, systems, or applications by identifying vulnerabilities through authorized simulated cyberattacks. A well-structured Pentest Contract Template includes sections on confidentiality, reporting, liability limitations, and compliance with relevant security standards.
How to Use the Pentest Contract Template
Using the Pentest Contract Template requires a clear understanding of the project requirements and the client's security objectives. Start by customizing the template to reflect specific details about the scope of testing, such as the network segments or applications to be tested. It's important to specify the testing methodologies and tools that will be employed, ensuring they align with the client's risk management strategies. Once customized, both parties should review the contract to ensure clarity on all terms. Any necessary amendments should be agreed upon before both sides sign the document to formalize the agreement.
Steps for Customization
- Identify Testing Scope: Clearly define the assets to be tested, including any specific areas of concern.
- Set Testing Schedule: Agree on a timeframe for the testing to ensure minimal disruption to business operations.
- Outline Deliverables: Detail what reports will be provided post-testing, including the format and timing.
- Include Confidentiality Clauses: Ensure that sensitive information about vulnerabilities is protected.
Key Elements of the Pentest Contract Template
The Pentest Contract Template encompasses several critical sections that establish the foundation for a successful penetration test. Firstly, the scope of work must be clearly articulated to limit the potential for disputes. Next, payment terms should be stated to establish when and how much the service provider will be compensated. Confidentiality clauses are essential to safeguard the client's sensitive data uncovered during the testing. Liability and indemnification terms protect both parties from potential legal issues that may arise from the testing. Finally, the contract should specify the governing law, which determines the legal jurisdiction applicable to the agreement.
Crucial Sections
- Scope of Work: Detailed description of testing areas.
- Payment Terms: Information on payment schedules and amounts.
- Confidentiality: Provisions to protect sensitive findings.
- Liability Limitations: Constraints on the responsibility of both parties.
Important Terms Related to Pentest Contract Template
When working with the Pentest Contract Template, understanding specific terms is vital for all parties involved. "Penetration Testing" refers to the authorized simulated cyberattack against a system to evaluate its security. "Vulnerabilities" are weaknesses in a system that could be exploited by threats. "Testing Methodology" outlines the systematic approach the pentester will use to conduct the tests. Additionally, "Remediation" refers to the process of fixing the identified vulnerabilities. Having these terms clearly defined within the contract prevents misunderstandings and ensures effective communication between the client and service provider.
Legal Use of the Pentest Contract Template
The legal enforceability of the Pentest Contract Template is pivotal in protecting both the client and the service provider. It ensures compliance with laws such as the Computer Fraud and Abuse Act (CFAA) in the United States, which criminalizes unauthorized access to computers. The contract should include a clause granting explicit authorization for the service provider to conduct tests within the defined scope, protecting them from legal repercussions. Moreover, the contract must address data protection laws such as the General Data Protection Regulation (GDPR) if applicable, to ensure both parties are adhering to privacy requirements.
Who Typically Uses the Pentest Contract Template
The Pentest Contract Template is utilized by cybersecurity firms, independent security consultants, and organizations seeking to assess their cybersecurity infrastructure. Typically, the template is employed when a company needs third-party validation of their security measures. IT departments, risk management teams, and legal advisors often collaborate to ensure the contract aligns with organizational security policies and legal standards. Whether the user is a small business owner or part of a larger corporation, the template provides a structured approach to engaging professional penetration testing services.
Examples of Using the Pentest Contract Template
Real-world applications of the Pentest Contract Template demonstrate its versatility across industries. A financial institution, for instance, might use the template to engage pentesting services to comply with regulatory requirements such as the Payment Card Industry Data Security Standard (PCI DSS). A healthcare provider could use it to ensure the security of patient records, aligning with legal obligations under the Health Insurance Portability and Accountability Act (HIPAA). Another example involves a tech startup employing the template as a proactive measure to safeguard its software-as-a-service (SaaS) platforms, thus building customer trust and protecting its brand reputation.
Steps to Complete the Pentest Contract Template
Completing the Pentest Contract Template requires a systematic approach to ensure comprehensive coverage of all necessary sections. Begin by entering both parties' contact details and outlining the project's scope. Specify the testing methodologies and duration, then detail the payment terms, including the total cost and payment schedule. Add clauses regarding confidentiality, data protection, and liability limitations. Both parties should review the document thoroughly to confirm mutual understanding. Finally, the parties must sign the contract for it to become legally binding, ensuring each retains a copy for their records.
Completion Checklist
- Ensure all contact details are accurate.
- Verify the scope and methodologies align with client objectives.
- Confirm payment terms and schedule are agreeable.
- Check confidentiality and liability clauses for clarity.
- Both parties must sign and date the document.