Definition & Meaning
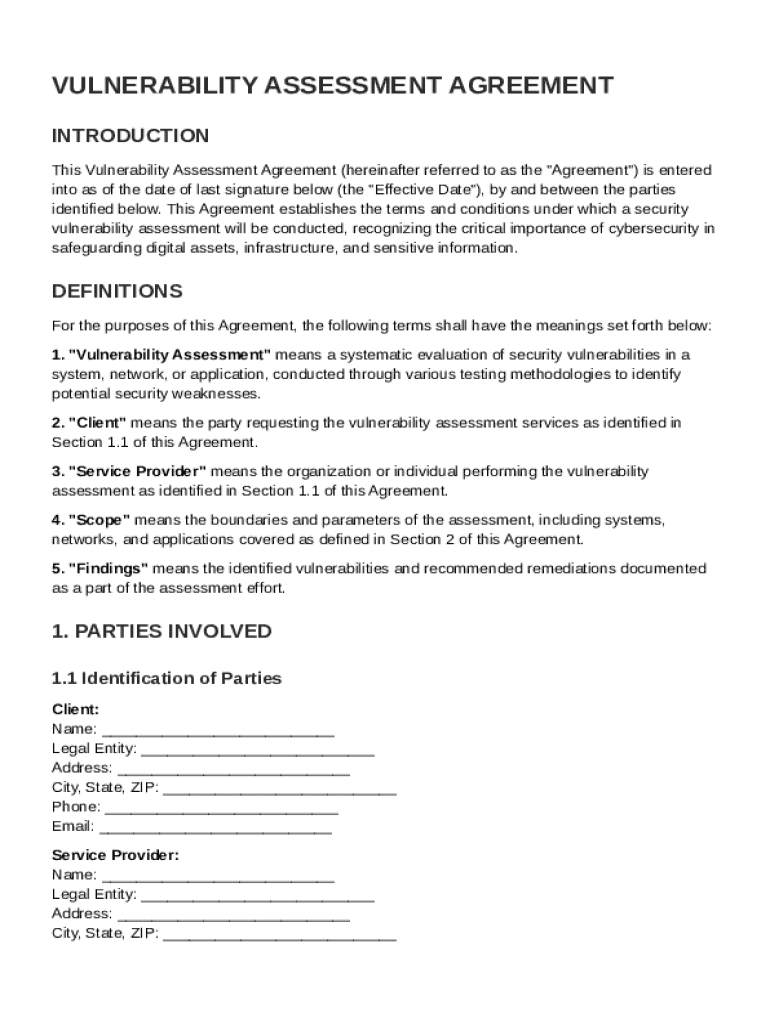
A Vulnerability Assessment Agreement Template is a legal document that outlines the terms and conditions governing a security vulnerability assessment. This agreement is typically entered between a Client and a Service Provider in order to detail the scope, responsibilities, and expectations of both parties involved in assessing and addressing potential security vulnerabilities in digital systems. The agreement is crucial for establishing a clear understanding of each party’s obligations to ensure the protection of digital assets.
Key Elements
- Scope of Work: Defines the specific activities and methodologies that will be deployed during the vulnerability assessment.
- Responsibilities: Details the duties and roles of both the Client and the Service Provider, ensuring both parties are aligned in their efforts.
- Confidentiality Obligations: Ensures that sensitive data and findings from the assessment are kept confidential and securely handled.
- Liability Limitations: Specifies the extent to which each party is liable for any incidents arising from the assessment process.
Key Elements of the Vulnerability Assessment Agreement Template
This section provides an in-depth look at the key elements that must be included in a comprehensive Vulnerability Assessment Agreement.
Scope of Work
The Scope of Work is a critical part of the template that defines what the vulnerability assessment will entail. This section should provide a detailed description of the testing methodologies, tools, and timelines. By precisely outlining these aspects, both parties can align their expectations, reducing the risk of misunderstandings or omissions.
Confidentiality and Reporting
The confidentiality obligation ensures that all sensitive information identified during the assessment remains protected. This section typically includes:
- Agreements on nondisclosure of findings.
- Protocols for data handling and storage.
Reporting Requirements
This element defines how the findings will be documented and shared. Typically, the agreement includes:
- Format and frequency of reports.
- Parties responsible for receiving and reviewing reports.
- Timeline for delivery of initial and final reports.
Steps to Complete the Vulnerability Assessment Agreement Template
Completing a Vulnerability Assessment Agreement Template involves several critical steps that need to be followed for accuracy and compliance.
Initial Consultation
- Identify Stakeholders: Gather information about the organizations involved.
- Define Objectives: Establish the primary goals of the vulnerability assessment.
Drafting the Agreement
- Populate Template Fields: Use the template to fill in details specific to the parties and the assessment.
- Review Legal Clauses: Ensure that the terms comply with relevant legal standards and are aligned with the parties' requirements.
Finalization and Signature
- Review and Adjust: Both parties should review the draft agreement and suggest any necessary changes.
- Sign the Agreement: Obtain signatures from representatives of both parties for legal validation.
Who Typically Uses the Vulnerability Assessment Agreement Template
The Vulnerability Assessment Agreement Template is used by a variety of entities, predominantly in the digital and technology sectors.


Common Users
- IT Security Firms: Engage with clients to provide thorough security assessments of their systems.
- Large Corporations: Require periodic security checks to protect sensitive corporate data.
- Government Agencies: Conduct assessments to safeguard critical infrastructure.
- Consultancies: Offer specialized advisory services and need formal agreements with clients.
Legal Use of the Vulnerability Assessment Agreement Template
Understanding the legal context of using a Vulnerability Assessment Agreement Template is critical to ensuring compliance and avoiding potential disputes.
Legal Requirements
- ESIGN Act Compliance: Ensure electronic signatures within the agreement are legally recognized.
- Data Protection Laws: Ensure the agreement aligns with existing data protection regulations, such as the GDPR or CCPA, depending on jurisdiction.
Best Practices
- Incorporate Legal Review: Have a legal expert review the final agreement to ensure that all necessary legal protections are in place.
Examples of Using the Vulnerability Assessment Agreement Template
Real-world implementations of the Vulnerability Assessment Agreement can provide valuable insights into its practical application.
Case Studies
- Financial Institutions: Utilize the template to engage external cybersecurity experts to uncover potential breaches in banking infrastructure.
- Healthcare Providers: Use the agreement to secure patient data by identifying system vulnerabilities and implementing tailored security measures.
State-Specific Rules for the Vulnerability Assessment Agreement Template
State-specific rules can influence the structure and enforceability of a Vulnerability Assessment Agreement.
Variability by State
- Regulatory Differences: Some states have specific cybersecurity regulations that impact how vulnerability assessments must be conducted and documented.
- Legal Terminology: Understand how state laws may affect the agreement's enforceability and the use of certain legal terms.
Examples
- California: The California Consumer Privacy Act (CCPA) imposes strict confidentiality obligations for handling personal data uncovered during assessments.
Software Compatibility
The ability to use and manipulate the Vulnerability Assessment Agreement Template across different software platforms can enhance its utility and accessibility.
Compatible Platforms
- DocHub: Allows direct editing and signing of the agreement.
- Google Workspace: Offers integration with Google Drive and Gmail for seamless document handling.
- Adobe Acrobat: Provides PDF functionalities for further document manipulation.