Definition and Meaning
The phrase "Restriction b - ncbi nlm nih" references specific data or document handling protocols related to the National Center for Biotechnology Information (NCBI), under the National Library of Medicine (NLM), part of the National Institutes of Health (NIH). It pertains to classification or usage guidelines for accessing certain types of scientific data or information managed by these institutions. Understanding these terms helps users navigate and comply with specific access and usage requirements when engaging with NCBI resources.
How to Use the Restriction b - ncbi nlm nih
To utilize data or publications under the "Restriction b" protocols, individuals should first ensure they understand all associated access guidelines. This often involves:
- Reviewing any use agreements or terms of service provided by NCBI.
- Ensuring compliance with data access ethics, particularly if dealing with sensitive or proprietary information.
- Employing designated channels or repositories for access, which may require authentication or special permissions.
Steps to Complete the Restriction Compliance Process
- Identify Required Access: Ascertain what specific data or documents require use under the "Restriction b."
- Review Guidelines: Thoroughly read any NCBI, NLM, or NIH documentation related to access restrictions.
- Authenticate Access: Use appropriate login credentials or institutional access rights, if necessary.
- Document Use: Maintain records of data usage to ensure compliance with any follow-up inquiries or audits.
Who Typically Uses the Restriction b - ncbi nlm nih
Common users of these protocols include:
- Academic Researchers: Particularly those involved in genetic, biological, or clinical studies needing access to restricted scientific data.
- Healthcare Professionals: Accessing data for research or operational purposes.
- Government and Policy Makers: Utilizing information for public health initiatives, policy development, or regulation purposes.


Key Elements of the Restriction b - ncbi nlm nih
- Access Protocols: The necessity to follow specific steps for gaining access to data.
- Compliance: Adhering strictly to usage guidelines, which may vary based on the nature of data.
- Ethical Considerations: Ensuring research ethics is followed, particularly concerning sensitive data.
Legal Use of the Restriction b - ncbi nlm nih
Utilizing data under "Restriction b" involves understanding and following legal stipulations such as:
- Data Protection Laws: Including privacy laws that may affect how data is handled and shared.
- Publication and Usage Rights: Ensuring correct attribution and avoiding unauthorized dissemination of material.
Software Compatibility
When accessing data or documents under these restrictions, compatibility with standard software and tools may be essential, such as:
- Data Analysis Tools: Software like R or Python for handling large datasets.
- Document Management Platforms: Such as DocHub for organizing and managing document workflows.
Examples of Using the Restriction b - ncbi nlm nih
Practical usage examples may include:
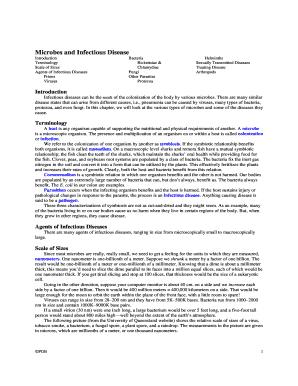
- Biological Studies: Using restriction protocols in studying specific gene expressions or effects.
- Public Health Research: Accessing proprietary data for epidemic research or control strategy development.
Application Process and Approval Time
Accessing data or documents under this restriction typically requires an application process:
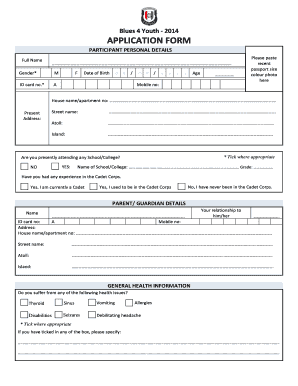
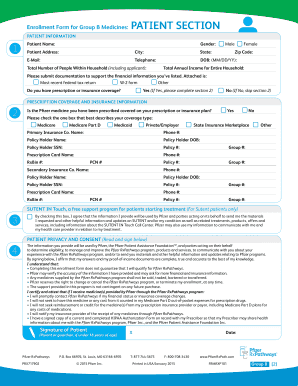
- Application Steps: Filling out forms or applications via NCBI portals.
- Approval Duration: Timeframes may vary based on data sensitivity and user credentials, typically ranging from a few days to weeks.
Required Documents for Access
Gain necessary access by preparing:
- Identity Verification: Institutional or personal identification documents.
- Access Justification: Explanation of intended data use, possibly including detailed research proposals.
Eligibility Criteria
Eligibility for accessing data under these protocols often depends on:
- Institutional Affiliation: Often reserved for recognized academic or research institutions.
- Purpose of Use: Must align with approved scientific or educational purposes.

Penalties for Non-Compliance
Failure to adhere to protocols may result in:
- Loss of Access: Temporary or permanent restriction from NCBI resources.
- Legal Ramifications: Including possible sanctions or fines for unauthorized use or dissemination of sensitive information.