Definition & Meaning
The ACH Security Framework Self-Assessment Worksheet 1 is a tool that helps organizations evaluate their adherence to the security standards necessary for safeguarding Automated Clearing House (ACH) data. The worksheet provides a structured approach to assessing the organization's policies and procedures concerning IT security, data handling, destruction of protected information, and employee training. These measures align with the NACHA Operating Rules, which establish minimum obligations for protecting ACH data throughout its lifecycle.
How to Use the ACH Security Framework Self-Assessment Worksheet 1
Organizations can use the ACH Security Framework Self-Assessment Worksheet 1 to systematically assess their compliance with security standards. The worksheet is typically divided into sections that correspond to various aspects of ACH data protection:
-
Review Current Security Policies: Begin by outlining existing security policies that pertain to ACH data. Evaluate their effectiveness against current standards.
-
Data Handling Procedures: Assess how ACH data is collected, stored, and transmitted. Ensure these processes minimize the risk of unauthorized access.
-
Employee Training Programs: Examine the extent and frequency of staff training on data security protocols and updates to the NACHA Operating Rules.
-
Security Incident Response: Evaluate procedures in place for responding to unauthorized data access or breaches and assess the adequacy of the response.
Organizations should provide detailed answers to each section and note any areas that require improvement. It's essential to involve relevant stakeholders from IT, compliance, and operations in this assessment to gather comprehensive insights.
Steps to Complete the ACH Security Framework Self-Assessment Worksheet 1
Completing the ACH Security Framework Self-Assessment Worksheet 1 involves several key steps:
-
Gather Necessary Documentation: Collect all relevant documents related to your organization's ACH data security policies and procedures.
-
Conduct a Policy Review: Analyze existing policies for alignment with the NACHA Operating Rules.
-
Assess Procedures and Controls: Evaluate the controls in place for protecting ACH data, including encryption protocols and access restrictions.
-
Identify Training Needs: Determine if staff members are sufficiently trained and make plans for additional training if gaps are found.
-
Fill Out the Worksheet: Complete each section of the worksheet thoroughly, documenting both compliance and areas needing improvement.
-
Create an Action Plan: Develop a plan to address identified weaknesses, complete with timelines and responsible parties.
Completing this worksheet not only supports compliance but also enhances ACH data security within the organization.
Key Elements of the ACH Security Framework Self-Assessment Worksheet 1
The ACH Security Framework Self-Assessment Worksheet 1 includes several vital components designed to evaluate different aspects of data security:
- Security Policy Assessment: Verification of documented security policies for ACH data.
- Data Environment Review: Analysis of the IT infrastructure that handles ACH transactions.
- Risk Management Procedures: Documentation of approaches used to identify and mitigate risks.
- Training and Awareness Programs: Evaluation of programs that inform staff about data protection practices.
- Incident Response Protocols: Review of procedures for addressing data breaches or unauthorized access.
These elements collectively provide a comprehensive overview of an organization's ACH security posture, allowing for targeted improvements.
Who Typically Uses the ACH Security Framework Self-Assessment Worksheet 1
The worksheet is utilized primarily by financial institutions, third-party service providers, and any businesses involved in processing ACH transactions. Typically, the IT departments, compliance officers, and risk management professionals within these organizations are responsible for completing the assessment. By using this worksheet, organizations can ensure they are in line with industry standards and are protecting their customers' sensitive information effectively.
Legal Use of the ACH Security Framework Self-Assessment Worksheet 1
The use of the ACH Security Framework Self-Assessment Worksheet 1 is critical for maintaining compliance with U.S. laws and regulations governing electronic payments. Organizations are legally obligated to protect ACH data to prevent fraud and data breaches. This assessment helps ensure adherence to the NACHA Operating Rules and other relevant regulations, providing a foundation for legal compliance and offering a defense against potential legal actions in case of data mishandling.
Important Terms Related to the ACH Security Framework Self-Assessment Worksheet 1
Understanding key terminology is crucial when working with the ACH Security Framework:
- NACHA Operating Rules: Guidelines that define the responsibilities of participants in the ACH network to ensure secure transactions.
- Protected Information: Specific customer data handled within ACH transactions that must be secured.
- Encryption Protocols: Technologies or methods used to protect data during transmission.
- Data Breach: Unauthorized access to confidential data with potential misuse.
- Risk Mitigation: Strategies designed to reduce adverse effects on ACH data security.
Familiarity with these terms aids in effectively completing the self-assessment and implementing robust security practices.
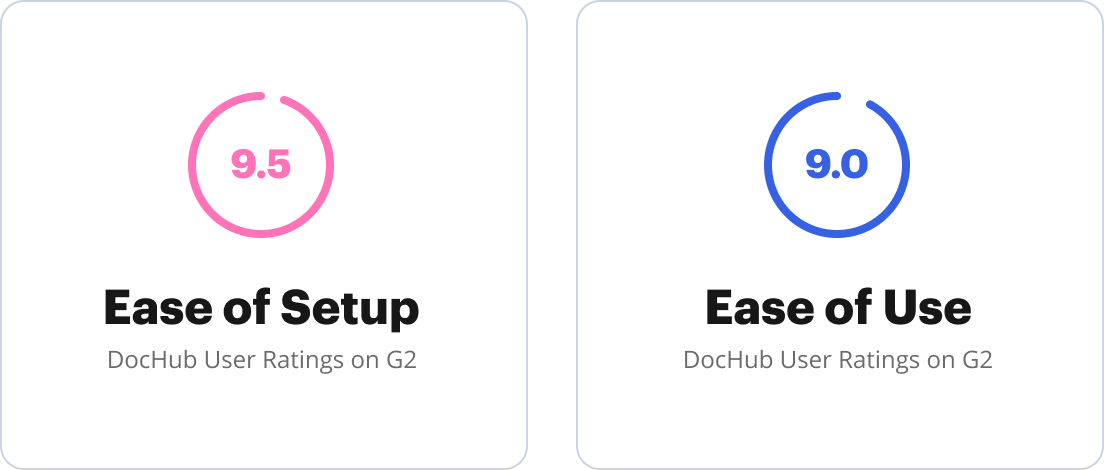
Software Compatibility
For organizations using software tools to aid in the completion and analysis of the ACH Security Framework Self-Assessment Worksheet 1, it's important to ensure compatibility with existing systems. Many institutions may use software like TurboTax or QuickBooks for financial data management, and it is essential that any tools used for ACH security assessment integrate seamlessly with these systems to facilitate easy data sharing and reporting. Integrating compatible software solutions allows for a more streamlined assessment process, reducing the risk of manual errors and enhancing overall data security management.