Definition and Meaning of Advanced Computing Research Institute Theory - Cornell University
The "Advanced Computing Research Institute Theory - Cornell University" refers to the foundational theoretical concepts developed and researched by the Advanced Computing Research Institute at Cornell University. This body of work typically involves sophisticated mathematical and computational methods intended to address complex computing challenges. Scholars and researchers at this institute focus on developing new theories and algorithms that advance the field of computer science, particularly in areas like machine learning, quantum computing, and data processing.
Practical Applications of the Theory
The theories developed at the Advanced Computing Research Institute have far-reaching applications. In practical settings, these theories are applied to solve computational problems in various industries, such as finance for risk assessment models, healthcare for analyzing medical data, and technology for optimizing algorithms in big data analytics. Research insights can also influence the creation of new software tools and frameworks used by developers worldwide.
Examples of Application
- Finance: Algorithms improving risk assessment and fraud detection models.
- Healthcare: Analyzing large datasets for patient diagnosis and treatment plans.
- Technology Development: Enhancing data storage solutions and cloud computing efficiencies.
How to Access the Theory
To access the theories and research findings from the Advanced Computing Research Institute, individuals can explore academic papers published by the institute's researchers. These publications are often available in renowned computer science journals or through Cornell University’s digital repository. Additionally, the institute may host seminars and workshops, which are invaluable for networking and gaining firsthand insights from leading researchers.
Steps to Access
- Visit Cornell University’s Digital Repository: Search for specific topics or papers related to the Advanced Computing Research Institute.
- Subscribe to Academic Journals: Stay updated with the most recent publications in journals where Cornell researchers frequently publish.
- Attend Workshops: Participate in seminars hosted by the institute for direct engagement with the academic community.
Steps to Utilize the Theory
Implementing the theory effectively involves understanding and contextualizing it to fit specific computational challenges. Professionals utilize these theories by first engaging with the foundational materials and then collaborating with experts who specialize in practical applications.
Implementation Process
- Comprehensive Study: Start by reviewing foundational texts and research papers to grasp core concepts.
- Collaborative Sessions: Work with teams or industry experts familiar with implementing such theories.
- Pilot Testing: Apply the theories in small-scale projects before full-scale implementation.
Importance of the Advanced Computing Research Institute Theory
This research institute's contributions hold significant value due to its pioneering work in addressing some of modern computing’s most pressing challenges. The theories generated not only enrich academic circles but also every facet of computational advancement, fostering innovation across multiple sectors.
Key Benefits
- Innovation Catalyst: Drives the development of cutting-edge technologies.
- Interdisciplinary Reach: Influences a broad spectrum of fields beyond computer science.
- Educational Resource: Acts as a profound resource for academic instruction and student learning.
Typical Users of the Advanced Computing Research Institute Theory
The users of this theory are diverse, ranging from academic researchers and educators to industry professionals and technologists. Specifically, data scientists, software developers, and systems analysts might find these theories particularly beneficial for crafting efficient and scalable solutions.
User Profiles
- Academic Researchers: Enhance knowledge and innovate further in the field of computing.
- Industry Professionals: Develop products and services with newly informed technological approaches.
- Educators: Integrate the latest theories into curricula to prepare the next generation of computer scientists.
Legal Considerations When Using the Theory
When applying these theories, it’s crucial to understand the legal implications, especially if they are used for commercial purposes. Intellectual property laws related to academic research must be respected, ensuring proper attribution and compliance with relevant legal standards.
Legal Compliance Steps
- Review Intellectual Property Rights: Confirm the usage rights for any advanced computing theories.
- Acknowledge Authorship: Properly cite and attribute any academic sources or frameworks utilized.
- Commercial Use Licensing: Investigate any licensing requirements if the theory forms part of a product or service.
Key Elements of the Theory
The core elements involve mathematical models, algorithm development, and computational efficiency. These foundational aspects support the robust frameworks that can be applied to solve real-world problems.
Core Components
- Mathematical Models: Used to represent and solve complex computational problems.
- Algorithm Development: Creation of step-by-step processes for computation.
- Efficiency Optimization: Enhancing performance and reducing resource consumption across various computing tasks.
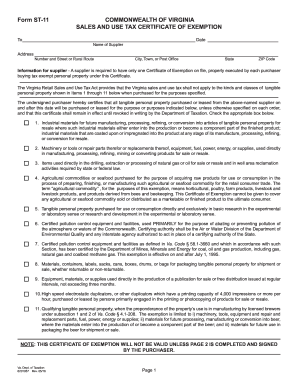
State-Specific Guidelines for Application
While the theories themselves are universal, implementing them may require adherence to state regulations, especially concerning data privacy and ethical AI use in the United States. Familiarity with state laws ensures responsible and legally compliant application of these advanced computational theories.
Examples of State Considerations
- Data Privacy: Align with state-specific data protection laws.
- Ethical AI Practices: Ensure AI applications adhere to local ethical standards.
- Regulatory Approvals: Secure necessary permissions where applicable, especially in sectors like healthcare or finance.