Understanding the ZF Microsystem-Based Embedded System Application
ZF Microsystem-based embedded system applications are specialized technological solutions that utilize ZF Microsystems technology for various industrial and consumer applications. These systems are often implemented in projects requiring robust and secure authentication processes, such as fingerprint verification systems, which have become increasingly vital in ensuring data security and user authentication.
Key Components and Technologies
- Cyrix Media GX Processor: A crucial part of this system, the Cyrix Media GX processor powers the embedded applications, offering computational capabilities necessary for processing biometric data.
- ZF Microsystem Board: This hardware is integral to the system, facilitating the interconnection of components and supporting various I/O functions critical for embedded applications.
Security and Authentication Technologies
Embedded system applications often emphasize strong security measures, employing biometric methods like fingerprint verification. This approach is central to ensuring secure and reliable user identification and access control across diverse environments.
How to Use the ZF Microsystem-Based Embedded System Application
Using this application involves a series of steps tailored to the specific needs of the project at hand, whether it's for personal security or more complex industrial applications.
Setup and Configuration
- Installing the Hardware: Begin by securely setting up the ZF Microsystem board within the application environment, ensuring all connections are stable and meet the necessary power and data transfer requirements.
- Software Installation: Load the appropriate software that interfaces with the ZF Microsystems technology, typically necessitating specific drivers and applications that support the processor and embedded system board.
Operational Use
- Biometric Enrollment: Users must enroll their biometric data, such as fingerprints, into the system. This involves a secure and accurate capture of user data, which the system uses to verify identities efficiently.
- Access and Execution: Following enrollment, the system can be used to either grant or restrict access based on the biometric verification, ensuring both security and reliability in operational environments.
Steps to Complete the ZF Microsystem-Based Embedded System Application
Completing this application entails a series of methodical steps tailored to ensure the system's optimal setup and functionality.
- Integration of Components: Assemble the hardware components, including the processor and microsystem board, ensuring compatibility and functionality.
- System Configuration: Configure the system parameters to align with the intended use, which may include setting security levels, defining user roles, and enabling specific functions.
- Testing and Evaluation: Thoroughly test the system to ensure all aspects function correctly. This step is crucial in identifying and rectifying any potential issues related to data entry accuracy or processing speed.
Importance of the ZF Microsystem-Based Embedded System Application
The significance of this application lies in its capability to deliver secure, reliable, and efficient microprocessor-based solutions for embedding tasks. The high level of security offered by fingerprint verification is invaluable for sensitive data environments, adding an extra layer of protection against unauthorized access.
Benefits and Use Cases
- Security Enhancement: Provides high-assurance user authentication.
- Integration Flexibility: Supports a wide range of applications from consumer devices to industrial systems.
- Innovative Solutions: Facilitates the adoption of cutting-edge security technologies in various domains.
Relevant Terms and Contexts
- Biometrics: A critical term when discussing authentication technologies, it refers to metrics related to human characteristics used for identification.
- Minutiae Extraction: Part of fingerprint verification, involving identifying specific features in fingerprint patterns to recognize individuals accurately.
Legal and Compliance Considerations
Using ZF Microsystem-based applications involves understanding the legal and compliance frameworks that govern biometric and data security technologies. The setup ensures that data handling and processing comply with regulations to protect user privacy and data integrity.
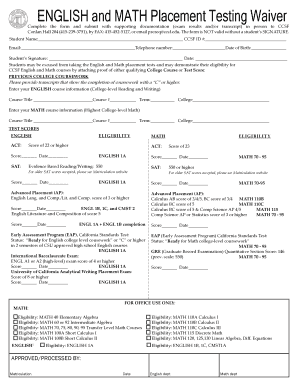
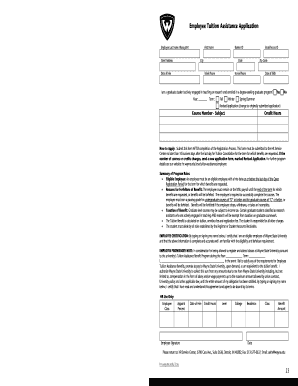
Application and Approval Process
The application process for implementing these systems may involve various approval stages, particularly in regulated industries. Engagement with technical experts and adherence to industry standards are required to successfully deploy and operate these systems.
Approval Time and Procedures
- Pre-Implementation Assessments: Conduct thorough evaluations to ensure compliance with technical and legal standards.
- Regulatory Submissions: Post-evaluation, submit necessary documentation to governing bodies for approval, ensuring all protocols meet industry requirements.
Given these detailed insights, users and potential adopters of the ZF Microsystem-based embedded system applications can better understand their significance, application, and the necessary steps to integrate them into their technological and operational frameworks.