Definition and Meaning
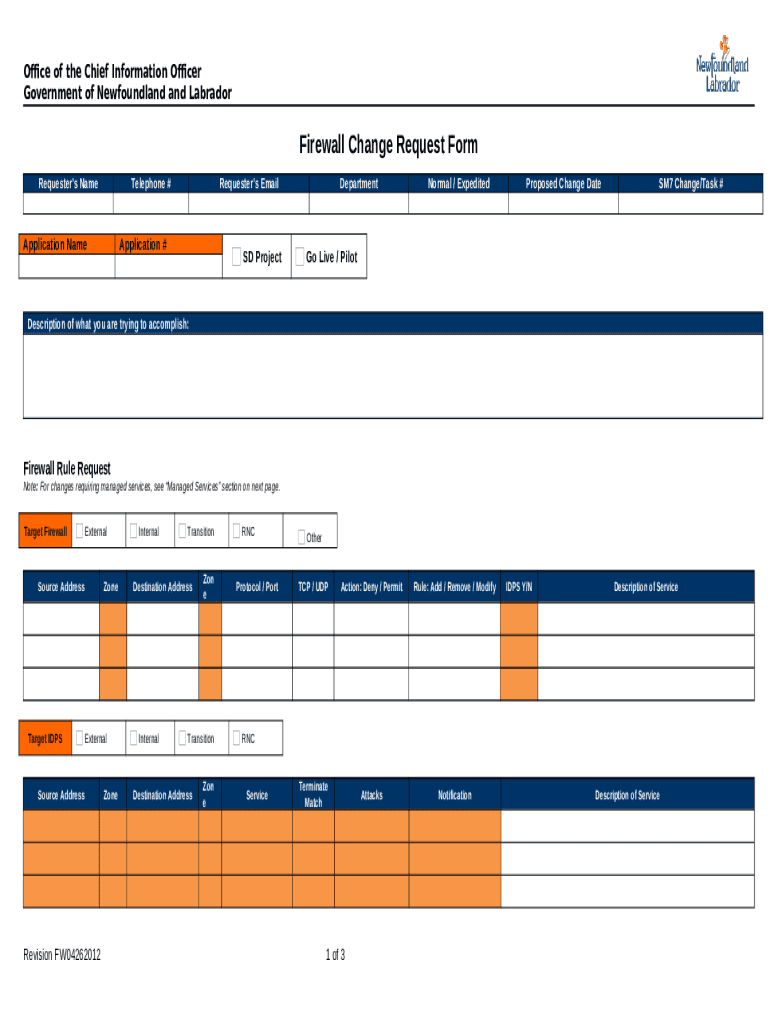
The Firewall Change Request Form Doc is a structured document used to request modifications to firewall configurations. This form is crucial for entities that manage network security, ensuring that any changes to the firewall are documented, reviewed, and approved in a systematic manner. By using this form, organizations manage network traffic effectively, maintaining the balance between robust security measures and operational efficiency. It typically requires users to provide detailed information about the requested changes and the justification for these changes to facilitate informed decision-making.
How to Use the Firewall Change Request Form Doc
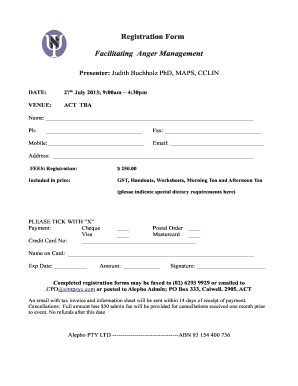
Using the Firewall Change Request Form Doc involves a step-by-step process that begins with gathering necessary information and ends with submitting the form for approval. First, the requester needs to complete all applicable sections, providing details such as the changes proposed, justification, affected systems, and any potential impact. After completing the form, it may require a series of reviews by different parties, such as IT security personnel or departmental managers.
- Identify the necessary changes.
- Complete the form, filling in all required sections.
- Attach any supporting documentation or data.
- Submit the form through the designated channel for review.
- Follow up for any feedback or further clarification required by the reviewers.
Steps to Complete the Firewall Change Request Form Doc
Completing the Firewall Change Request Form Doc requires the user to carefully follow each section to ensure comprehensive coverage of the request. This typically includes:
- Requester Information: Fill in personal details such as name, department, and contact information.
- Technical Details: Specify the nature of the firewall change, detailing IP addresses, ports, and protocols involved.
- Business Justification: Provide a detailed explanation of why the change is necessary, including business impact assessment.
- Approval Signatures: Obtain necessary signatures from approvers within the organization before submission.
- Submission: Send the completed form to the appropriate department for review and final approval.
Key Elements of the Firewall Change Request Form Doc
A well-structured Firewall Change Request Form Doc contains various key elements to facilitate clear communication and efficient processing:
- Requester Information: Names and roles of individuals requesting the change.
- Desired Changes: Description of the specific firewall rules to be modified.
- Business Justification: Rationale for the request and expected benefits.
- Impact Analysis: Potential effects on system performance or security.
- Review and Approval Sections: Spaces for necessary sign-offs from IT and management.
Who Typically Uses the Firewall Change Request Form Doc
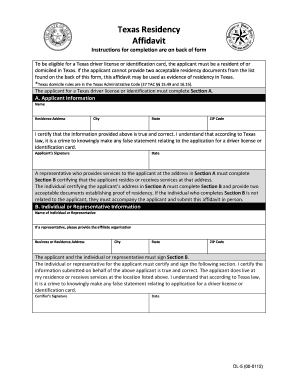
This form is commonly used by IT professionals, network administrators, and security managers tasked with managing and securing a company's network infrastructure. Organizations with formal change management processes in place, particularly in sectors such as finance, healthcare, and government, often rely on such forms to ensure that changes do not compromise network integrity or data security. Additionally, the form is vital for compliance purposes, helping businesses adhere to regulatory standards.

Legal Use of the Firewall Change Request Form Doc
Legally, the Firewall Change Request Form Doc serves as an official record of changes made to network security protocols. It provides a documented trail that can be critical during audits or legal inquiries, ensuring that all changes are traceable and approved by authorized personnel. The form complies with industry regulations and standards like HIPAA for healthcare or PCI DSS for financial transactions, safeguarding sensitive data against unauthorized access.
Examples of Using the Firewall Change Request Form Doc
The form might be used in scenarios such as:
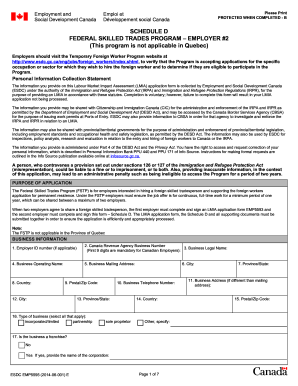
- Network Expansion: When a company expands its network infrastructure and requires new firewall rules to accommodate additional servers or offices.
- Security Policy Update: Updating firewall settings in response to new cyber threats or changes in organizational security policies.
- Compliance Requirements: Adjusting firewall configurations to meet updated legal or regulatory requirements.
Digital vs. Paper Version
The Firewall Change Request Form Doc can exist as both a digital and a paper document, each with its own advantages. The digital version often integrates with document management systems, offering benefits like easy sharing, version control, and electronic signatures. Meanwhile, the paper version may be preferred in environments with strict document retention policies or limited access to digital resources. Digital forms also facilitate more straightforward access for auditing and can enhance efficiency in organizations emphasizing paperless processes.