Definition and Meaning of a Key Agreement Form Template
A key agreement form template is a structured document used to formalize the process of issuing and managing keys, particularly in institutional or corporate settings. It typically outlines the responsibilities and obligations of parties involved, such as the issuer (e.g., a university or company) and the recipient (e.g., a contractor or employee). Its primary function is to ensure clear communication and compliance with key management policies, safeguarding the organization's assets.
In many cases, a key agreement form will specify that the keys remain the property of the issuing entity and stipulate conditions under which they are to be returned, usually after a specified term or upon completion of a service or project. Terms for liability and penalties for late returns or loss may also be included, reinforcing the importance of accountability in key management practices.
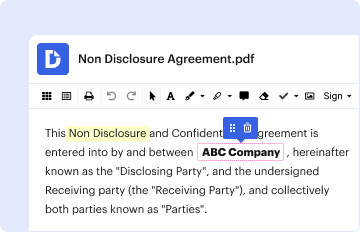
Steps to Complete the Key Agreement Form Template
Completing a key agreement form template involves several coordinated steps ensuring both parties understand their responsibilities. Detailed instructions help mitigate errors and foster compliance.
-
Review the Document: Thoroughly read through the entire agreement to understand its terms and conditions. Pay attention to clauses related to key usage, return policies, and liability.
-
Fill in Recipient Information: Accurately enter the recipient's details, such as name, contact information, and position or relationship with the issuing entity.
-
Detail Key Information: Specify details about the keys being issued. This may include the key number, location it accesses, and any special access restrictions.
-
Acknowledge Conditions: Both parties should carefully review the conditions related to key handling, including return deadlines and penalties for non-compliance.
-
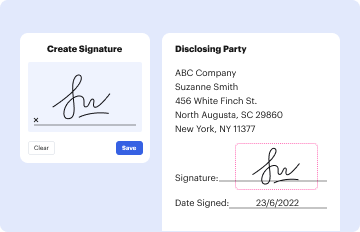
Sign the Agreement: Ensure both the recipient and an authorized representative of the issuing entity sign the agreement. Electronic signatures may be used if compliant with ESIGN standards.
-
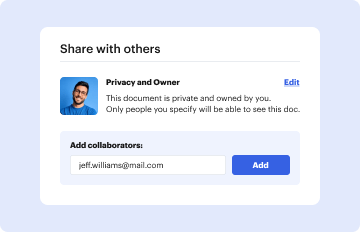
Distribute Copies: Once completed, ensure both parties receive a copy of the signed agreement for their records. Confirm that any additional procedures, such as intake into a digital system, are finalized.
Who Typically Uses the Key Agreement Form Template
Key agreement forms are commonly utilized by organizations where access control is crucial to operations. Examples include:
- Universities and Schools: Ensuring restricted areas such as labs and administrative offices are securely accessed by authorized personnel only.
- Corporations and Businesses: Managing access to high-security areas and resources to prevent unauthorized entry and ensure compliance with internal security policies.
- Government Institutions: Maintaining access control in government offices where sensitive information and resources are protected.
- Facilities Management Teams: Coordinating access for contractors and maintenance personnel to ensure they can perform necessary work without compromising security.

Important Terms Related to Key Agreement Form Template
Understanding specific terminology related to key agreements is essential for clarity and legal compliance.
- Issuer: The party granting access through key issuance, often the owner or responsible custodian of a property or facility.
- Recipient: The individual or entity receiving keys, responsible for their use and return.
- Liability: The responsibility, often of the recipient, for any loss or unauthorized use of the keys.
- Return Policy: The terms specifying when and how keys must be returned to the issuer.
- Compliance: Adherence to the conditions outlined in the agreement, which may include timely return of keys and maintaining confidentiality regarding facilities accessed.
Legal Use of the Key Agreement Form Template
Key agreement forms serve as legal documentation to uphold security protocols and protect organizational assets. They are used to:
- Establish Accountability: Clearly delineate the responsibilities of the key holder, reducing the likelihood of unauthorized access or misuse.
- Provide Recourse: Outline the consequences of non-compliance, providing legal grounds for action in cases where terms are breached.
- Ensure Transparency: Document the rights and obligations of both parties, minimizing disputes over policy clarity.
- Support Liability Claims: Serve as evidence in legal situations to determine liability for loss or damage due to unauthorized access.
Key Elements of the Key Agreement Form Template
A well-constructed key agreement form typically includes several critical components:
- Recipient and Issuer Information: Identifying details of both parties, establishing their roles and responsibilities.
- Description of the Keys: Specific information on the keys being issued, including identifiers and access level details.
- Terms and Conditions: Detailed stipulations governing key use, maintenance, and return process.
- Signatures: Both parties must sign the document to indicate mutual agreement and acceptance of terms.
- Acknowledgments: Sections affirming that both parties understand their commitments regarding security and confidentiality.
Examples of Using the Key Agreement Form Template
Real-world scenarios where a key agreement form template proves essential include:
- University Maintenance: A contractor is issued keys to dormitory buildings to perform necessary maintenance over the summer break. The agreement mandates key return upon completion and outlines penalties for delayed returns.
- Corporate Security: A new facilities manager receives keys to various secure zones within a tech company’s headquarters. The key agreement emphasizes protocols for securing keys and penalizes any loss or non-reported theft.
- Government Projects: A contractor working on a government infrastructure project receives multiple keys to restricted access points. The agreement enforces strict return policies and highlights the legal implications of any compliance lapses.
These examples illustrate the vital role key agreements play in managing access across sectors, ensuring security, and fostering responsible key management.
Penalties for Non-Compliance
Non-compliance with key agreement terms can result in significant penalties. These may include:
- Financial Penalties: Charges or fines associated with loss or late return of keys, intended to cover replacement costs and administrative handling.
- Access Revocation: Temporary or permanent denial of access privileges for failure to adhere to agreement terms.
- Legal Action: Pursuit of legal remedies against the recipient for unreturned keys, which could involve civil claims or other formal proceedings.
- Disciplinary Measures: In organizational settings, non-compliant employees may face disciplinary action, affecting their employment status or position.
Understanding these penalties underscores the importance of adherence to the key agreement stipulations.