Understanding the Bomb Threat Checklist
The Bomb Threat Checklist is an essential tool for organizations to effectively manage and respond to bomb threats. It provides a structured way to gather critical information during a threatening call to ensure that responders can act swiftly and efficiently.
Purpose of the Bomb Threat Checklist
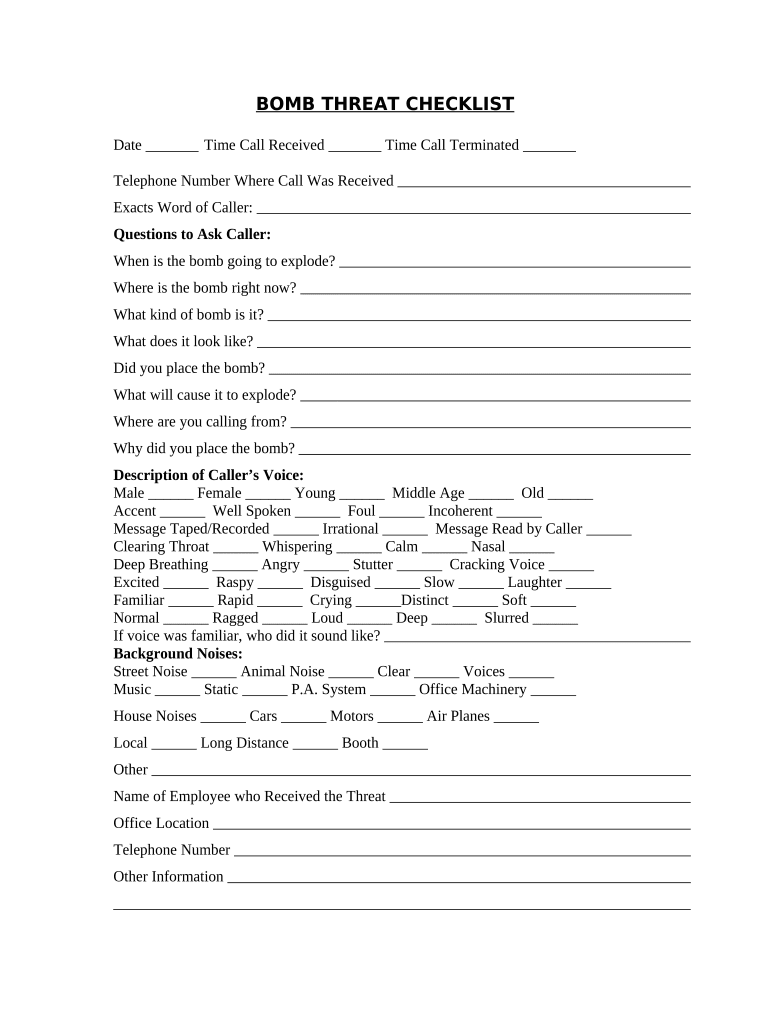
The primary objective of the Bomb Threat Checklist is to guide individuals in documenting vital details during a bomb threat situation. Accurate and detailed information collection is crucial for law enforcement and emergency services to assess and respond appropriately to the threat. This checklist addresses several key areas:
- Recording Call Specifics: Capture critical details such as the time of the call, the number from which the call originated, and specific content of the threat itself.
- Identifying Caller Traits: Note distinctive characteristics of the caller’s voice, such as tone, emotion, and any muffled sounds. This information can aid in identifying the caller later.
- Background Assessment: Document any noteworthy sounds heard in the background, which may provide clues about the caller’s location or circumstances.
Key Questions to Ask During a Bomb Threat Call
Having a set list of questions can help the person receiving the threat gather relevant information. Key questions to include in your checklist are:
- Location and Timing: Ask where the bomb is located and the time it will detonate.
- Description: Request a description of the bomb, such as its size and type.
- Motivation: Inquire about the reasons for the threat, which can provide insight into any potential motives.
- Caller Identification: Ask the caller for their name or alias, if possible.
Gathering this data can be invaluable for emergency services and can help determine the seriousness of the threat.
Documentation and Reporting Procedures
Once information is collected during a bomb threat, the checklist guides how to document and report this data. Essential elements include:
- Immediate Reporting: Ensure the information is relayed to the appropriate authorities as soon as possible. This typically includes local law enforcement and building security.
- Record Keeping: Maintain detailed records of the call, including the checklist itself and any follow-up actions taken. Consider creating an incident report that includes time stamps and actions performed.
- Post-Incident Review: After the situation has resolved, conduct a review of the incident. Assess what worked well and identify areas for improvement in your response protocols.
Importance of Training Employees on the Checklist
Training employees on how to use the Bomb Threat Checklist is critical. Organizations should consider the following:
- Regular Drills: Conducting bomb threat drills helps familiarize employees with the checklist and reinforces their ability to respond effectively under pressure.
- Role Assignment: Designate specific roles for staff members during a bomb threat situation, including who will answer the call and who will contact authorities.
- Knowledge Refreshers: Regular training sessions help keep the information fresh in employees' minds and adapt to any updates in procedures.
Legal Considerations
Organizations should also be aware of the legal implications related to bomb threats. This includes:
- Reporting Requirements: Be aware of local laws regarding mandatory reporting of bomb threats to authorities.
- Liability Issues: Understand potential liabilities connected to mishandling bomb threats, including the responsibilities toward employees and public safety.
- Privacy Concerns: Ensure that any collected information complies with privacy laws and does not infringe on individuals’ rights.
Conclusion: The Role of the Bomb Threat Checklist
The Bomb Threat Checklist serves not only as a reactive tool but also as a proactive measure for safety planning. By ensuring that all personnel are trained in its use, organizations can create a safer environment and enhance their preparedness for unforeseen emergencies.