Definition and Meaning of a Security Log Book PDF
A security log book in PDF format serves as a digital tool designed to record and maintain detailed accounts of security-related activities and incidents. The PDF format ensures that data is accessible, consistently formatted, and easily shared across digital platforms. Utilized by security professionals, this document acts as a chronological record of events, assisting in monitoring and protecting premises, assets, or sensitive information. Security logs can include entries about patrol rounds, visitor registrations, alarm checks, or any incident that requires documentation, enhancing both transparency and accountability in security operations.
How to Use the Security Log Book PDF
-
Recording Entries:
- Begin by opening the file using a PDF editor such as DocHub. This allows for seamless editing and signing.
- Log entry details including time, date, event type, and personnel involved. Ensure entries are concise yet comprehensive to provide a clear record.
-
Sign-Off Requirements:
- Some entries may require verification by a supervisor or designated officer for authenticity.
- Use electronic signature capabilities to sign off on entries, confirming the actions or incidents recorded.
-
Review and Analysis:
- Regularly review entries to assess patterns or potential security risks.
- Utilize search functions within the PDF to quickly locate specific entries.
How to Obtain the Security Log Book PDF
A security log book PDF can often be obtained through the following methods:
-
Download from Security Software Providers: Many security systems or software offer templates that can be downloaded directly from their website or application.
-
Custom Templates: Create a custom security log book using a PDF editor like DocHub. This allows tailoring of fields to match specific security needs, such as including sections for specific checks or incidents.
Steps to Complete the Security Log Book PDF
-
Open the PDF:
- Use an accessible PDF editor to open the file, ensuring that you can fill out and make changes as needed.
-
Entering Information:
- Start by filling in foundational details such as the organization’s name, date, and personnel involved.
- Use predefined fields to log time-stamped entries of security rounds or incidents, detailing the nature of each event.
-
Finalizing Entries:
- Once all entries are made, review them for accuracy and completeness.
- Use the signing tool to authenticate the document if required.
Key Elements of the Security Log Book PDF
-
Date and Time of Entry: Each log entry begins with a precise timestamp to maintain a systematic record.
-
Description of Incident or Task: Provide detailed descriptions of security incidents or tasks performed, using pre-set categories where applicable.
-
Personnel Information: Include names and roles of individuals involved or witnessing the entry, enhancing accountability.
-
Incident Outcome or Action Taken: Summarize the outcome of the event or corrective actions taken following the incident.
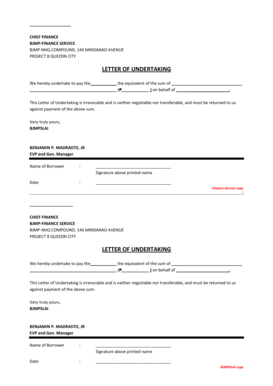
Legal Use of the Security Log Book PDF
The security log book PDF serves multiple legal purposes, including:
-
Evidence in Legal Proceedings: In case of disputes or incidents, the log acts as legally admissible evidence documented in accordance with organizational procedures.
-
Compliance and Regulations: Maintain compliance with industry standards and regulations requiring documentation of security practices and events.
-
Audit Trails: Provide thorough records for audits, demonstrating adherence to security protocols and investigation procedures.
Who Typically Uses the Security Log Book PDF
-
Security Personnel: Guards and officers use the log book to document their patrols and any irregularities they encounter.
-
Facility Managers: Responsible for analyzing log book data to improve security measures and address potential vulnerabilities.
-
Event Coordinators: For events or gatherings, log books help track the flow of guests and any security incidents.


Examples and Scenarios of Using the Security Log Book PDF
-
Retail Outlets: Track shoplifting incidents, employee entries, or unusual customer behavior.
-
Construction Sites: Record entry and exit times for workers and visitors, ensuring the site remains safe and secure.
-
Corporate Offices: Document after-hours entries by cleaning crews or maintenance staff, reinforcing security protocols.
Software Compatibility and Integration
The security log book PDF can be integrated with various digital environments:
-
DocHub: Seamlessly edit and manage the document on both desktop and mobile devices, using Google Drive and other cloud services.
-
Other Applications: Utilize with applications like TurboTax, QuickBooks for financial aspect tracking, or Excel for data analysis.
Security log books are not just tools but comprehensive systems ensuring security teams operate efficiently and responsively. Their integration into an organization's broader security framework enhances effectiveness, providing a valuable record for monitoring and analysis.