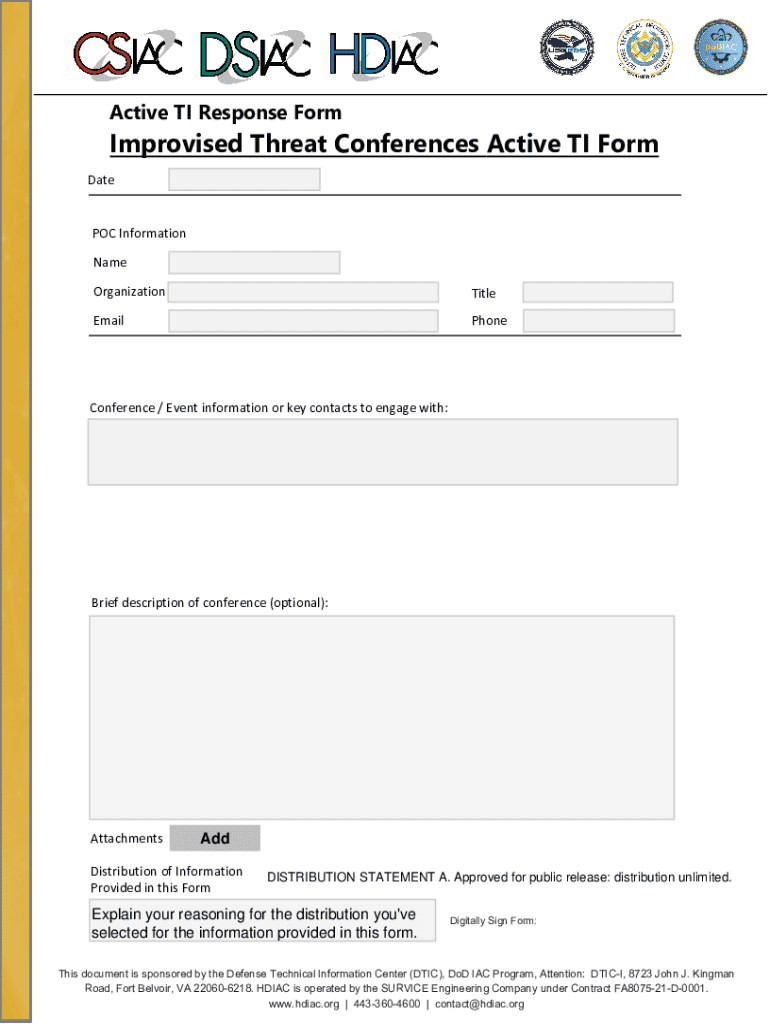
Definition & Meaning
The Active Ti Response Form is pivotal in the context of Improvised Threat Conferences, providing a structured method for gathering essential information. Sponsored by the Defense Technical Information Center and operated by SURVICE Engineering Company, this form is specifically designed to collect data related to conference details, point of contact information, and distribution statements. It is a critical document used to streamline information sharing and ensure organized record-keeping within defense-related discussions.
How to Use the Active Ti Response Form
To effectively utilize the Active Ti Response Form, one must follow a systematic approach. Start by gathering all necessary details related to the Improvised Threat Conference. This includes the date, location, and specifics such as the agenda or topics to be discussed. The form serves as a comprehensive tool that organizes this information neatly, ensuring clarity and consistency. Each section of the form is designed to prompt the user for precise data, minimizing errors and omissions.
Step-by-Step Instructions
- Collect Conference Details: Note the date, time, and venue of the conference.
- Identify Point of Contacts: Record names, titles, and contact information of key individuals.
- Describe the Conference: Provide a brief overview of the objectives and intended outcomes.
- Include Distribution Statements: Specify who receives the documents and any necessary classifications.
- Review and Sign: Ensure all information is accurately filled before the final submission.
Steps to Complete the Active Ti Response Form
Completing the Active Ti Response Form requires attention to detail and a systematic approach. The sections must be addressed in a logical sequence to ensure that no pertinent information is overlooked. Start with the top section where the date and conference metadata are entered, followed by the identification of relevant contacts engaged in the process. This is where the detail-oriented nature of the form shines, allowing comprehensive coverage of the details involved.
Detailed Instructions
- Prepare Required Information: Gather all relevant data about the conference.
- Fill Out Key Sections: Start with date and location, followed by the participant details.
- Complete Descriptive Sections: Add information on conference objectives and distribution needs.
- Validate Entries: Cross-check all details and correct any inaccuracies.
- Finalize: Sign off and distribute the completed form to necessary stakeholders.
Who Typically Uses the Active Ti Response Form
The typical users of the Active Ti Response Form are professionals involved in defense-related activities, specifically those organizing or attending Improvised Threat Conferences. This includes defense contractors, military officials, and logistics coordinators who need to ensure seamless information flow and record-keeping.

Key Elements of the Active Ti Response Form
The core components of the Active Ti Response Form include sections for:
- Date and Location: Capturing when and where the event takes place.
- Point of Contact Information: Essential for coordinating subsequent communications.
- Conference Details: Brief descriptions and objectives to provide context.
- Distribution Statements: Clarifying who is intended to receive the information and any security classifications.
Legal Use of the Active Ti Response Form
The Active Ti Response Form complies with legal standards and regulations pertaining to information sharing within the defense sector. It ensures that sensitive data is documented and transferred in accordance with established guidelines, protecting both the integrity and confidentiality of information.
Examples of Using the Active Ti Response Form
An example of the form in action includes its use in a hypothetical Improvised Threat Conference organized by a governmental defense agency. The form assists in collecting detailed contact information of attendees, as well as specifying the classification levels of shared documents. This illustrates the form’s utility in organizing complex information required for strategic discussions.
Key Takeaways
Using the Active Ti Response Form enhances the organization and compliance of data collection for conferences with security implications. It serves as a standardized method for documenting essential details, which are pivotal for effective communication and legal adherence within defense operations. The form’s precise structure ensures a thorough capture of information, minimizing data loss and facilitating streamlined conference preparations.