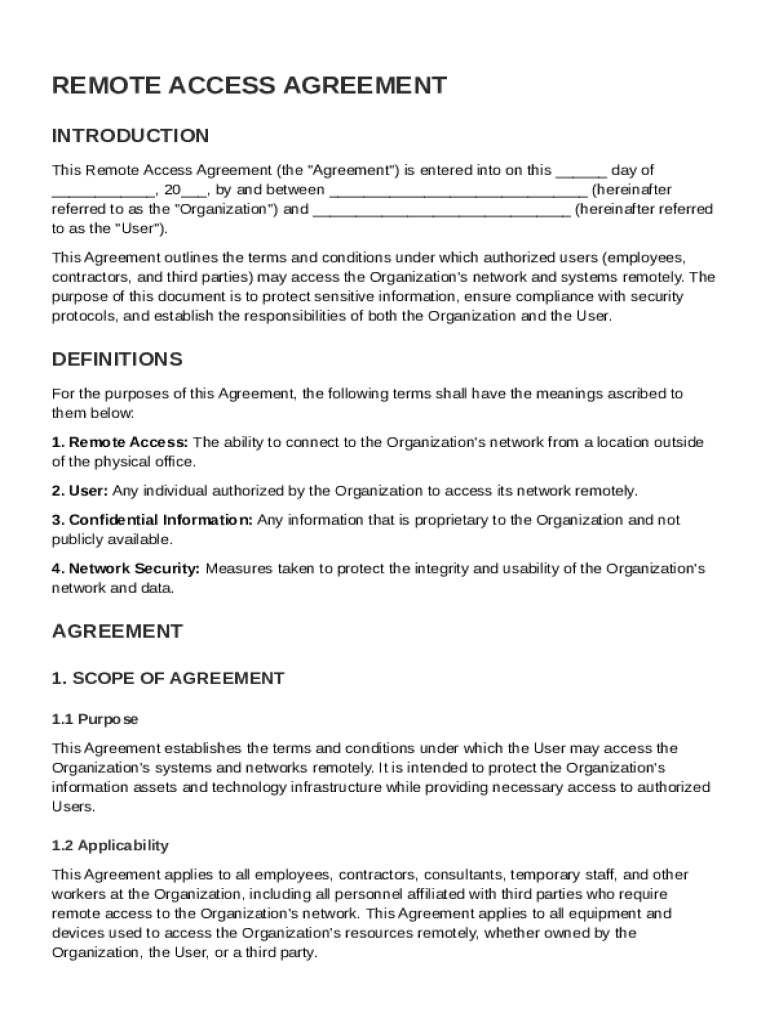
Definition and Meaning
The Remote Access Agreement Template is an essential document that outlines the terms and conditions for authorized access to an organization's network from remote locations. This agreement serves to delineate responsibilities and expectations for both the organization and users. It comprehensively defines key terms and establishes protocols for ensuring network security, confidentiality, and compliance. By adhering to this agreement, organizations can control access to their sensitive information and maintain the integrity of their systems while allowing necessary remote connectivity.
How to Use the Remote Access Agreement Template
Using the Remote Access Agreement Template requires careful consideration of various factors to tailor it to organizational needs. Begin by reviewing the default language and sections in the template, ensuring it aligns with your company's policies and requirements. Customize sections such as user roles, access level definitions, and specific security measures. Managers should collaborate with IT and legal teams to adapt the agreement accurately. Once customized, distribute it to relevant parties, ensuring all users comprehensively understand and agree to the outlined conditions before being granted access.
Key Elements of the Remote Access Agreement Template
The template consists of several critical components that establish a framework for secure remote access. These elements include:
- Authorization Procedures: Clear steps outlining how users gain approval to access the network remotely.
- Security Measures: Protocols for maintaining data security, such as password policies and encryption requirements.
- Monitoring and Auditing: Procedures for monitoring user activity to detect unauthorized access or violations.
- Termination Conditions: Criteria under which remote access may be revoked or suspended.
- Liability and Indemnification: Clauses protecting the organization from losses due to unauthorized access.
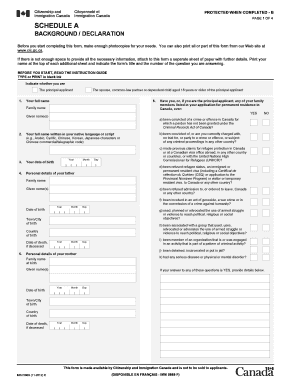
Steps to Complete the Remote Access Agreement Template
Completing the Remote Access Agreement Template involves several steps:
- Gather Input: Collect necessary information from IT, HR, and legal departments to ensure comprehensive coverage.
- Customize Content: Adapt the template to fit specific organizational requirements and security policies.
- Review Legal Compliance: Ensure the document complies with relevant data protection laws and industry standards.
- Finalize and Distribute: Obtain approvals from relevant stakeholders before distributing the agreement to users.
Who Typically Uses the Remote Access Agreement Template
Organizations that permit employees and third-party contractors to access their networks remotely typically use this template. IT departments and HR personnel frequently handle the coordination and enforcement of this agreement. It serves businesses of various sizes and industries, particularly those with a mobile or remote workforce, such as tech firms, consultancies, and customer service centers.

Legal Use of the Remote Access Agreement Template
Ensuring the legal integrity of the Remote Access Agreement Template is crucial. The document should comply with applicable U.S. federal and state regulations concerning data protection and cybersecurity. Organizations must ensure the agreement respects privacy legislation such as the General Data Protection Regulation (GDPR) if they operate internationally alongside U.S. laws like the Computer Fraud and Abuse Act (CFAA). Consulting legal counsel to confirm compliance is advisable.
State-Specific Rules for the Remote Access Agreement Template
Although the agreement primarily follows federal guidelines, some states may impose additional requirements or adjustments. For instance, states like California, with stringent data privacy laws, may necessitate additional clauses related to the California Consumer Privacy Act (CCPA). Ensure to verify specific state regulations to maintain compliance with local statutes and amend the agreement accordingly.
Important Terms Related to Remote Access Agreement Template
Understanding key terms within the agreement can aid clarity and comprehension:
- Authentication: Verification processes that confirm user identities before granting access.
- Data Encryption: Techniques employed to secure data transmission and storage.
- Network Security Protocols: Standards that protect data and network infrastructures from unauthorized access.
- User Permissions: Defined levels of access allocated to different types of users based on their roles and responsibilities.