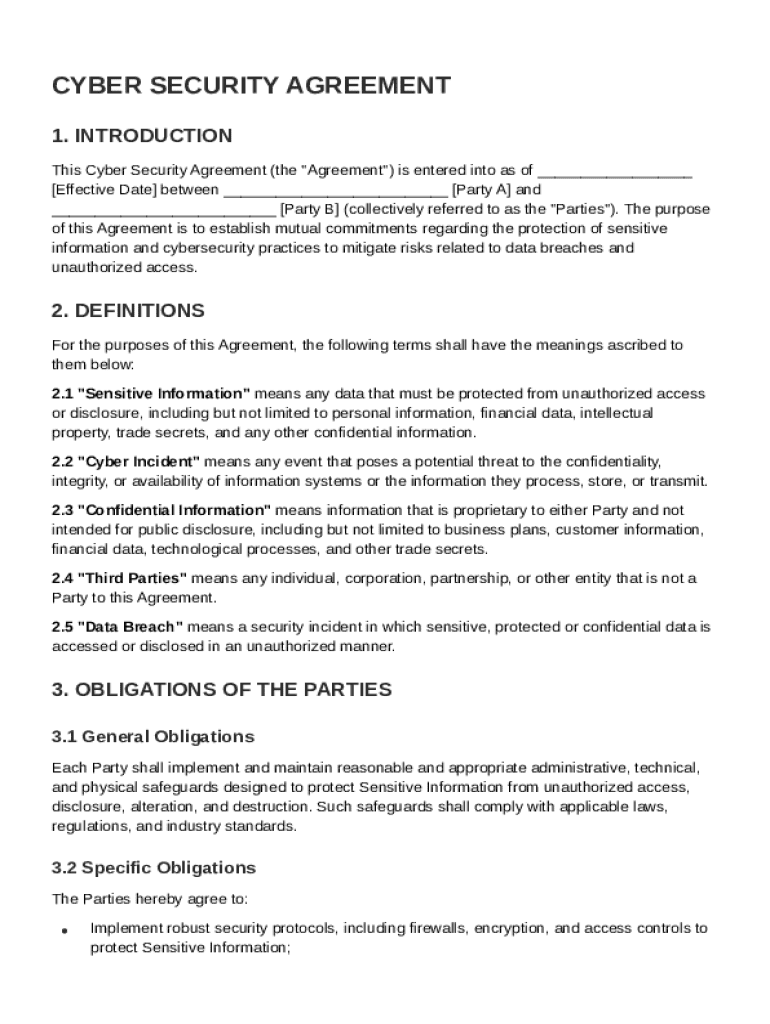
Definition and Meaning
A Cyber Security Agreement Template is a specialized document designed to outline the mutual responsibilities and commitments between two parties in protecting sensitive information. It functions as a framework to establish cybersecurity practices aiming to safeguard data, prevent unauthorized access, and manage risks associated with data breaches. The agreement typically defines key terms such as "Sensitive Information" and "Data Breach," ensuring both parties understand their obligations. By setting clear guidelines, the template aids in implementing consistent security protocols, conducing audits, and conducting employee training, forming a robust foundation for data protection.
Key Components of a Cyber Security Agreement
- Definition of Sensitive Information: Specifies what constitutes sensitive data within the context of the agreement.
- Data Breach Protocols: Details procedures to follow in the event of a security breach, including notification requirements.
- Security Obligations: Outlines the responsibilities of parties in implementing and maintaining cybersecurity measures.
- Legal Compliance: Ensures adherence to applicable data protection laws and regulations.
How to Use the Cyber Security Agreement Template
Using a Cyber Security Agreement Template involves several steps to tailor it to the specific needs of the involved parties. The process begins with identifying the sensitive data to be protected, followed by customizing the agreement to reflect the responsibilities of each party. It's crucial to ensure the document encompasses all necessary security measures, legal obligations, and procedures that align with the organization's goals.
Steps for Customization
- Assess Security Needs: Identify the specific cybersecurity requirements for your organization or partnership.
- Draft Obligations: Clearly outline the security roles and responsibilities for each party involved.
- Review Legal Requirements: Ensure compliance with laws such as the Data Protection Act or other relevant regulations.
- Consult Legal Experts: Have the document reviewed by a legal professional to ensure enforceability and legal accuracy.
Steps to Complete the Cyber Security Agreement Template
Completing the Cyber Security Agreement Template requires a structured approach to ensure all necessary elements are accurately addressed. This process entails a thorough review of the agreement's provisions, careful customization according to relevant legal principles, and collaborative input from both parties to ensure mutual agreement.
Detailed Completion Process
- Initial Preparation: Gather all relevant information regarding both parties and the data to be protected.
- Customizing the Template: Adapt the template's sections to match the specific obligations and protection mechanisms of your organization.
- Legal Review: Ensure the template aligns with applicable cybersecurity laws and sector-specific regulations.
- Final Approval and Signing: Both parties should review and agree upon all terms before signing the document to make it legally binding.
Key Elements of the Cyber Security Agreement Template
The Cyber Security Agreement Template encompasses several fundamental elements critical for comprehensive data protection. These components ensure both parties understand their roles and responsibilities in maintaining cybersecurity and facilitate a structured approach to managing potential threats.
Fundamental Elements
- Obligations and Responsibilities: Clear delineation of roles in safeguarding data.
- Incident Response Plan: Detailed actions and accountability in case of a data breach.
- Confidentiality Provisions: Clauses to protect the integrity and confidential nature of the data exchanged.
- Termination Clauses: Conditions under which the agreement may end, including breach of security protocols.
Legal Use of the Cyber Security Agreement Template
The legal framework provided by a Cyber Security Agreement Template serves to formalize the commitment to cybersecurity by establishing enforceable terms and conditions. It ensures that both parties adhere to defined protocols to mitigate data breaches and comply with legal standards.
Ensuring Legal Compliance
- Regulatory Alignment: Ensures the agreement aligns with federal and state cybersecurity regulations.
- Indemnification Clauses: Provides protection against legal claims resulting from unauthorized access or compliance failures.
- Audit Rights: Grants rights to conduct periodic audits to verify compliance with the agreement's security protocols.
Important Terms Related to the Cyber Security Agreement
Understanding the terminology used within a Cyber Security Agreement is essential for both parties to meet their obligations effectively. Key terms define the scope of responsibilities and the protocols to be followed in different scenarios.
Notable Terms
- Sensitive Information: Any data deemed confidential and requiring protection.
- Data Breach: Unauthorized access to sensitive information necessitating immediate action.
- Encryption: The process of encoding information to prevent unauthorized access.
- Authentication Protocols: Established methods to verify the identity of users accessing confidential data.
Who Typically Uses the Cyber Security Agreement Template
The Cyber Security Agreement Template is utilized across various sectors to ensure data protection and compliance with cybersecurity legislation. It is particularly beneficial for businesses handling large volumes of sensitive data.


Common Users
- Tech Companies: To safeguard intellectual property and data against cyber threats.
- Healthcare Organizations: For compliance with HIPAA privacy rules regarding patient information.
- Financial Institutions: To secure transactional data and maintain trust with customers.
State-Specific Rules for the Cyber Security Agreement Template
Cybersecurity policies can vary significantly by state, impacting the legal obligations and enforcement of Cyber Security Agreements. Understanding these differences is crucial for customizing agreements to include state-specific requirements.
State Variations
- California: Strict guidelines under CCPA for consumer data protection.
- New York: Comprehensive security requirements under the NYDFS Cybersecurity Regulation.
- Texas: Specific provisions under the Texas Business and Commerce Code regarding data breach notifications.