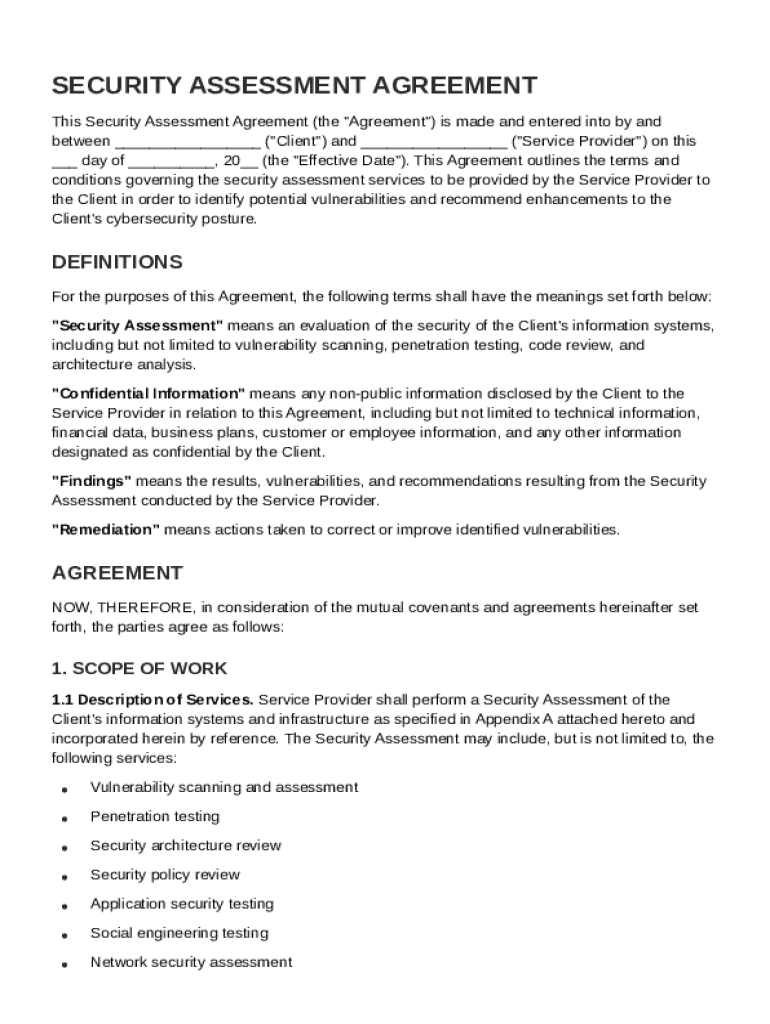
Definition & Meaning
A Security Assessment Agreement Template is a formal document that outlines the collaboration between a client and a service provider to analyze the client’s information systems for potential security vulnerabilities. The agreement specifies the parameters of the assessment, ensuring both parties understand their roles and responsibilities. Key terms often include ‘Security Assessment,’ ‘Confidential Information,’ and ‘Remediation.’ By utilizing this template, both parties agree to a structured process aimed at identifying cybersecurity weaknesses and suggesting improvements.
Detailed Explanation
- Security Assessment: This term generally refers to the process of evaluating the effectiveness of organizational security controls. The assessment aims to discover vulnerabilities that could be exploited by malicious actors.
- Confidential Information: Any sensitive data exchanged between the client and service provider during the assessment. The agreement usually defines what constitutes confidential information and stipulates how it should be protected.
- Remediation: The strategies and steps that will be taken to address any identified vulnerabilities. This section may outline specific actions the service provider recommends to enhance the client's security posture.
Key Elements of the Security Assessment Agreement Template
The Security Assessment Agreement Template includes crucial parts that ensure comprehensive coverage for conducting a security assessment. Understanding these elements helps in correctly filling and utilizing the template for maximum effectiveness and compliance.
Fundamental Components
- Scope of Work: This section describes what the security assessment will cover, which areas will be assessed, and any limitations to the evaluation. It ensures clarity on what tasks will be performed, avoiding future disputes.
- Responsibilities: Clearly defined responsibilities of both the client and service provider to ensure seamless execution of the assessment. It may include obligations for providing necessary access, resources, or information.
- Confidentiality Obligations: Specifies the requirements for maintaining secrecy of sensitive data. Both parties agree not to disclose any confidential information gathered during the assessment to unauthorized entities.
- Fees and Payment Terms: Details the financial aspects of the agreement, including the cost of services, payment schedules, and accepted methods of payment. It may also specify late payment fees or penalties.
- Termination Conditions: Outlines the processes and conditions under which the agreement can be terminated, ensuring both parties have the clarity on how they can legally end the engagement.
How to Use the Security Assessment Agreement Template
Correctly utilizing the Security Assessment Agreement Template involves understanding its components and following specific procedures to ensure all necessary information is captured.
Step-by-Step Instructions
- Review the Template: Begin by examining the complete document to understand its structure and requirements.
- Customize the Template: Modify sections to reflect the specific needs of both parties. Ensure the scope of work and responsibilities are accurate and relevant.
- Fill In Required Details: Enter necessary details such as the name of both parties, timeline, and specific agreements regarding confidentiality and fees.
- Legal Review: It is recommended for both parties to have the agreement reviewed by a legal professional to ensure compliance with applicable laws.
- Sign and Execute: After ensuring all sections are complete and accurate, both parties can execute the agreement through legally binding signatures.
- Store Properly: Maintain secure storage of the signed document, adhering to confidentiality obligations.
Legal Use of the Security Assessment Agreement Template
The Security Assessment Agreement Template adheres to legal standards required for such engagements, ensuring the practice aligns with U.S. laws and industry standards.
Legal Considerations
- Governing Law: The agreement usually specifies which jurisdiction's laws will govern the terms. This is particularly crucial in resolving any legal disputes.
- Liability Limitations: This area details the extent to which each party is liable in the case of a breach or failure in the assessment process.
- Intellectual Property: Addresses ownership of any data, analysis, or reports generated from the security assessment activities.
Who Typically Uses the Security Assessment Agreement Template
Various professionals and organizations benefit from utilizing a Security Assessment Agreement Template, particularly those operating within sectors susceptible to cybersecurity threats.
Users
- IT and Security Consultants: Frequently use this template when engaging with clients to perform security evaluations.
- Legal and Compliance Teams: Employ the template to ensure all procedural and legal obligations are met in contracts involving sensitive data handling.
- Businesses: Especially those handling sensitive or proprietary information, use this template to formalize engagements with external security auditors.
Examples of Using the Security Assessment Agreement Template
Real-world scenarios illustrate the practical application and benefits of the Security Assessment Agreement Template in safeguarding information systems.
Case Studies
- Financial Institutions: A bank entering into an agreement with a cybersecurity firm to regularly assess its online banking system for vulnerabilities.
- Healthcare Providers: Hospitals ensure confidential patient information is protected by working with security consultants to assess their IT systems.
- E-commerce Platforms: Online retailers use these agreements to engage security professionals in evaluating their transaction systems.
Important Terms Related to Security Assessment Agreement Template
Understanding related terminology enhances the comprehension and correct utilization of the Security Assessment Agreement Template.
Glossary
- Penetration Testing: Simulating cyber attacks on a system to discover and address vulnerabilities.
- Security Audit: A systematic evaluation of an organization's security measures and protocols.
- Data Breach: An incident involving unauthorized access to confidential information, often causing significant risks to business and reputation.
State-Specific Rules for the Security Assessment Agreement Template
While the Security Assessment Agreement Template generally follows a standard structure, specific state laws may influence certain aspects.
Key State Variations
- California: Known for its rigorous data protection regulations, agreements may need to address extra confidentiality provisions under frameworks like the CCPA.
- New York: Financial institutions may have additional requirements under the NYDFS Cybersecurity Regulation, impacting the content and obligations of the agreement.
- Texas: Larger businesses may be subject to specific state cybersecurity laws, requiring tailored agreements to stay compliant.