Definition & Meaning
The Privacy Impact Assessment (PIA) for the Women's Information and Services Engine (WISE) serves as a comprehensive evaluation to identify and mitigate risks associated with the handling of personally identifiable information (PII). It ensures that privacy considerations are integrated into the lifecycle of the IT system under the Veterans Health Administration. This assessment is crucial to guarantee that the processing of women's information in the WISE adheres to privacy laws and best practices.
Steps to Complete the PIA
-
Initiate the Assessment:
- Identify all stakeholders and systems involved.
- Gather relevant documentation for understanding data flows and processes.
-
Data Collection Analysis:
- Document what PII is collected, its purpose, and the means of collection.
- Assess how information is stored, used, and shared within WISE.
-
Risk Identification:
- Identify potential privacy risks and vulnerabilities that may impact data subjects.
- Evaluate the likelihood and impact of these risks.
-
Mitigation Strategies:
- Develop strategies to minimize identified risks, such as data encryption and access controls.
- Implement user training programs to bolster privacy protection.
-
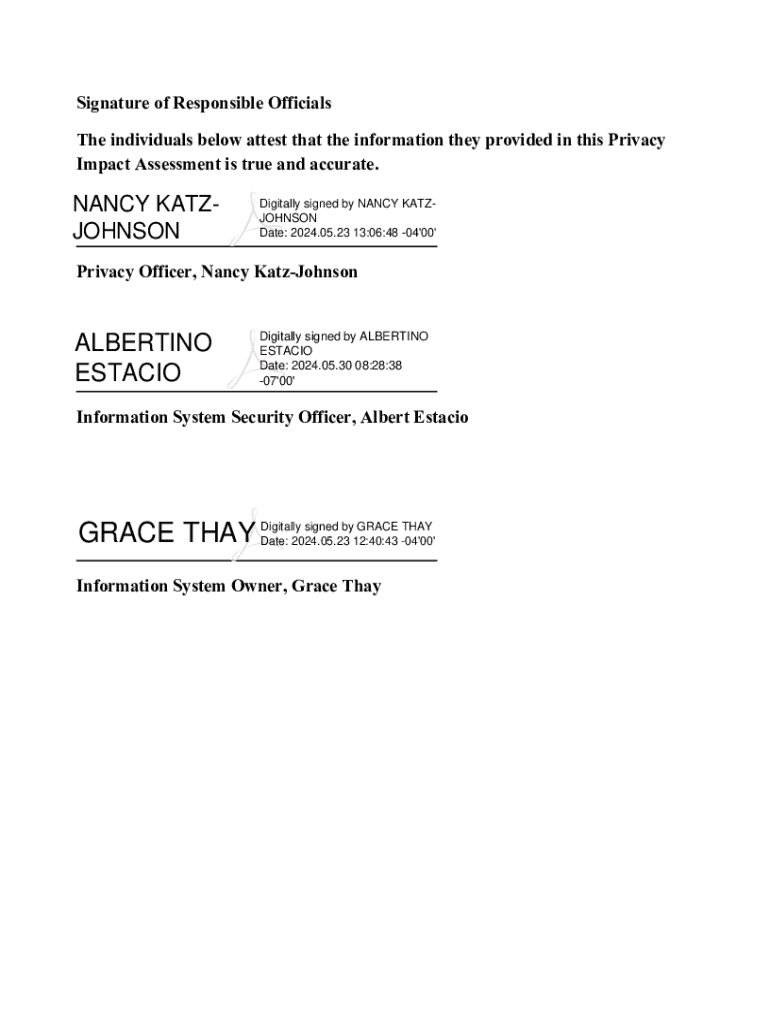
Review and Approval:
- Submit the completed PIA for review by the privacy office for compliance validation.
- Make revisions based on feedback, if necessary.
How to Use the PIA for WISE
-
For System Evaluation:
- Use the assessment to thoroughly evaluate how WISE collects and processes data.
- Implement the recommendations to enhance the system's privacy safeguards.
-
Training Tool:
- Use the PIA as part of privacy awareness and training sessions for those handling data in WISE.
- Ensure staff understands their roles in maintaining privacy.
Key Elements of the PIA
- Purpose and Scope:
- Clearly outline the objectives and boundaries of the system under assessment.
- Data Flow Diagrams:
- Visual representations of how data moves within the system.
- Privacy Risks and Mitigations:
- Detailed analysis of potential risks and proposed solutions.
Legal Use of the PIA
Compliance with federal privacy laws is mandatory, and the PIA helps ensure alignment with key regulations like the Privacy Act and HIPAA. Its legal use involves:
- Ensuring Transparency:
- Inform data subjects about how their information is handled.
- Ensuring Accountability:
- Track the system's privacy practices through documented evidence.
Who Typically Uses the PIA
- Privacy Officers:
- Oversee and manage privacy risks associated with WISE.
- System Administrators:
- Implement technical measures to protect PII.
- Legal Teams:
- Ensure all processes comply with relevant privacy laws and regulations.

Important Terms Related to PIA
- Personally Identifiable Information (PII):
- Any data that can be used to identify an individual.
- Data Encryption:
- Techniques used to safeguard data from unauthorized access.
- Privacy Act Compliance:
- Adherence to federal guidelines that govern the use of PII.
Examples of Using the PIA for WISE
- Scenario 1: System Update:
- Use the PIA to assess new features for potential privacy concerns.
- Scenario 2: Data Breach Response:
- Refer to the PIA to understand data flows and identify potential breaches.
- Scenario 3: Policy Development:
- Inform new privacy policies using insights from the PIA.
State-Specific Rules for the PIA
Although the PIA is federally guided, variations may exist in how states implement privacy protections based on state laws. Users should be aware of:
- State-Specific Data Protection Laws:
- Understand how state regulations like the CCPA in California intersect with federal guidelines.
- State Enforcement:
- Compliance checks might differ based on local privacy enforcement mechanisms.
With these blocks, this content provides a detailed and comprehensive overview of the Privacy Impact Assessment for the Women's Information and Services Engine (WISE), offering substantial information for users interested in understanding and applying the assessment.