Definition & Meaning
The Privacy Impact Assessment (PIA) for the VistA VAEC-AWS system is a crucial document within the Veterans Health Administration framework. It is designed to manage and protect sensitive data, including medical and mental health records of veterans. The primary goal of the PIA is to ensure that the VistA VAEC-AWS system complies with privacy regulations by outlining the types of data collected, methods of collection, and security measures in place to safeguard this information. By conducting a PIA, the Veterans Health Administration proactively identifies privacy risks and implements strategies to mitigate these risks.
Key Elements of the Privacy Impact Assessment for VistA VAEC-AWS
The PIA for the VistA VAEC-AWS system comprises several key elements crucial for maintaining privacy and data security:
- Data Collection Methods: It details how the system collects Protected Health Information (PHI) and Personally Identifiable Information (PII) from veterans.
- Data Sharing Practices: The PIA describes how data is shared internally within the Veterans Health Administration and with external entities. It specifies legal authorities that govern data sharing and usage.
- Security Measures: The document outlines various security protocols to protect data, including encryption and authentication methods.
- Privacy Risk Assessment: It provides an analysis of potential privacy risks and the associated mitigation strategies to ensure compliance with relevant privacy laws.
- Legal Compliance: The PIA ensures that data handling practices align with federal regulations and standards.
How to Use the Privacy Impact Assessment for VistA VAEC-AWS
The PIA serves as a comprehensive guide for organizations and individuals involved in managing the VistA VAEC-AWS system. Users should:
- Review Data Handling Practices: Understand how the system collects, shares, and protects sensitive information.
- Implement Compliance Strategies: Use the PIA as a blueprint to ensure all data-related processes adhere to federal privacy regulations.
- Identify Risks: Analyze the PIA to identify existing privacy risks and assess the effectiveness of current mitigation strategies.
- Plan for Improvements: Regularly update the PIA to incorporate new security measures and data protection enhancements.
Steps to Complete the Privacy Impact Assessment for VistA VAEC-AWS
Completing a PIA for the VistA VAEC-AWS system involves several crucial steps:
- Identify Information Types: Document all types of data collected and processed by the system, focusing on PHI and PII.
- Analyze Data Flow: Map out how data moves within the system and between external partners to identify potential privacy vulnerabilities.
- Assess Security Protocols: Evaluate current security measures in place, such as encryption standards and access controls.
- Document Legal Authorities: Ensure that all data handling practices comply with applicable legal requirements.
- Conduct Risk Assessment: Identify and document privacy risks, and develop strategies for risk mitigation.
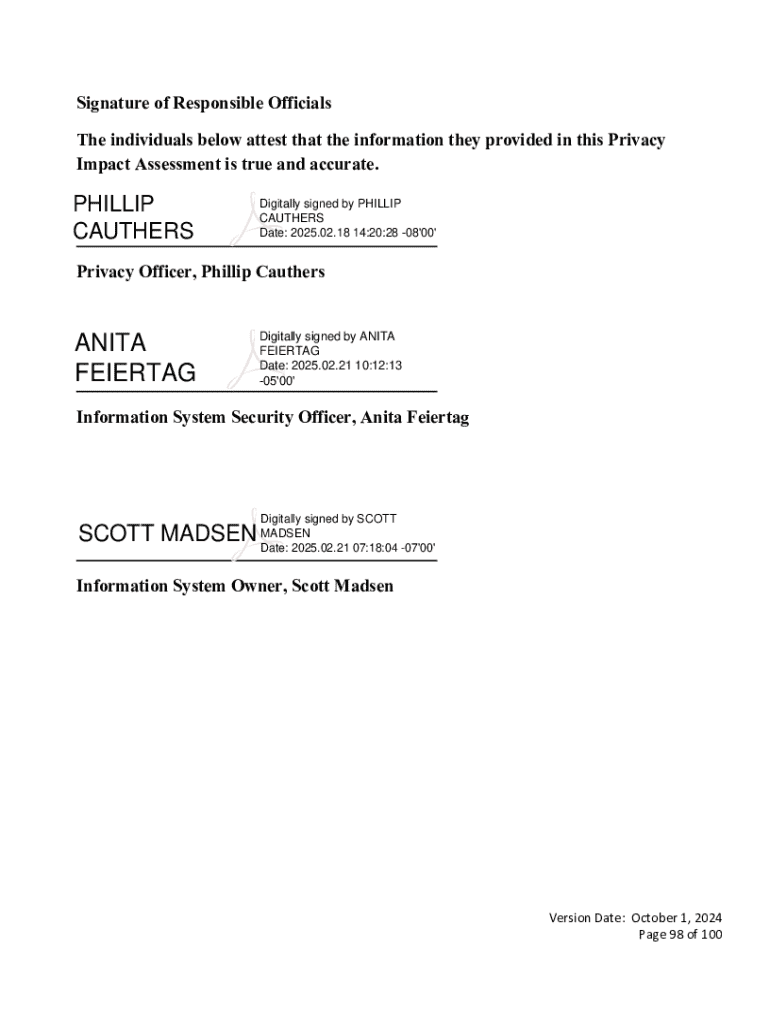
- Review and Approve: Submit the completed PIA for review and approval by relevant authorities within the Veterans Health Administration.
Legal Use of the Privacy Impact Assessment for VistA VAEC-AWS
The legal use of the PIA involves ensuring compliance with federal privacy laws and regulations. It serves as an official document:
- Compliance Verification: Demonstrates that the VistA VAEC-AWS system adheres to federal and organizational privacy standards.
- Audit and Accountability: Acts as evidence during audits to prove that proper data protection measures are in place.
- Risk Management: Supports legal teams in managing and mitigating privacy risks on a regular basis.
Important Terms Related to Privacy Impact Assessment for VistA VAEC-AWS
Understanding specific terminology related to the PIA is vital:
- Protected Health Information (PHI): Any information about health status, provision of health care, or payment for health care that can be linked to an individual.
- Personally Identifiable Information (PII): Any data that could potentially identify a specific individual or user.
- Encryption: The process of converting information or data into a code to prevent unauthorized access.
- Authentication: The process of verifying the identity of a user or process.
Examples of Using the Privacy Impact Assessment for VistA VAEC-AWS
Real-world scenarios where the PIA is used include:
- System Upgrades: Prior to upgrading the VistA VAEC-AWS system, organizations refer to the PIA to understand how changes may impact data privacy.
- Compliance Audits: During privacy compliance audits, the PIA serves as a reference document to assess current practices against legal requirements.
- Security Assessments: The PIA is employed in periodic assessments to evaluate security measures and ensure ongoing protection of sensitive information.
Who Typically Uses the Privacy Impact Assessment for VistA VAEC-AWS
The PIA is typically utilized by:
- Privacy Officers: To ensure data processing activities comply with privacy laws and regulations.
- IT Security Professionals: To implement effective security measures and monitor their efficacy.
- Data Governors: To oversee data collection, storage, and sharing practices within the Veterans Health Administration.
- Legal Teams: To provide legal advice and support compliance initiatives within federal regulatory frameworks.