Definition & Meaning
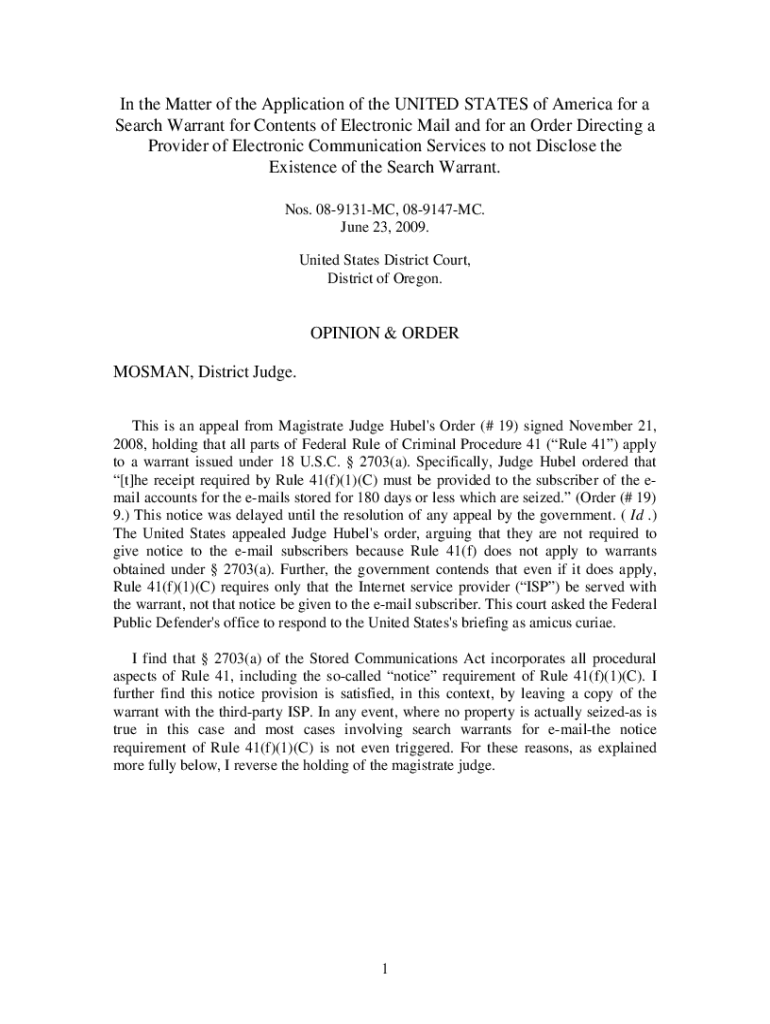
The phrase "In the Matter of the Application of the UNITED STATES of America" typically refers to a legal proceeding where the United States government is seeking a particular judicial action. Such applications are often seen in contexts involving warrants, subpoenas, or other requests requiring judicial approval. The primary objective is to obtain authorization from a court to perform certain actions, such as accessing electronic communications or conducting searches.
Key Elements of the Application
Several core elements are essential for understanding these types of applications:
- Legal Basis: Each application must cite the specific legal statutes or regulations under which the United States is seeking judicial approval.
- Purpose: Clearly defines the intent behind the application, such as gathering evidence or enforcing compliance with federal laws.
- Scope: Outlines the particular actions or access being requested by the government.
- Supporting Evidence: Provides documentation or affidavits that justify the need for the judicial action.
- Specificity: Describes the details of what the government aims to achieve, including the extent of the data sought or the area to be searched.
How to Obtain the Form
Typically, forms or applications related to this legal context are not directly obtained by the public but are submitted by government agencies or legal representatives. The process involves:
- Preparation by Legal Counsel: Government attorneys or representatives prepare the application, ensuring all legal criteria are met.
- Submission to Court: The completed application is filed with the appropriate federal court.
- Judicial Review: A judge reviews the application to ensure it complies with legal standards and protects constitutional rights.
Steps to Complete the Application
Completing an application in this context involves several methodical steps:
- Identify Legal Grounds: Specify the legal provisions that justify the application.
- Compile Supporting Information: Gather evidence and documents that support the request.
- Draft the Application: Prepare a detailed written application, ensuring clarity and legal compliance.
- Review for Accuracy: Check the application for any errors or omissions.
- File with Court: Submit the application to the relevant federal court for consideration.
Legal Use of the Application
The application is used within a stringent legal framework:
- Compliance with Statutes: The application must align with federal laws and procedural rules.
- Judicial Oversight: Judges evaluate applications to balance law enforcement needs with individual privacy rights.
- Confidentiality: Details of the application, particularly those involving sensitive information, are often sealed to protect ongoing investigations.
Who Typically Uses This Application
The primary users of such applications include:
- Government Agencies: Federal entities such as the Department of Justice or the FBI.
- Legal Representatives: Attorneys working on behalf of the United States government.
- Judicial Authorities: Judges who assess and approve or deny the applications based on the merits presented.
Important Terms Related to the Application
Understanding this application requires familiarity with several key terms:
- Warrant: A formal authorization issued by a judge allowing government action.
- Affidavit: A sworn written statement used as evidence supporting the application.
- Subpoena: A legal order requiring testimony or the production of documents.
- Sealed Application: A filing kept confidential to protect sensitive information.
State-Specific Rules for the Application
While the federal government primarily manages these applications, state-specific nuances may arise:
- Jurisdictional Variances: Different courts might have distinct procedural requirements.
- State Legislation: Some applications may need to consider state laws concerning privacy and data protection.
- Cooperative Agreements: State and federal agencies may collaborate, necessitating adherence to both federal and state protocols.
Examples of Using the Application
Real-world instances help illustrate how these applications function:
- Electronic Data Access: The government seeks access to data stored by Internet service providers under the Stored Communications Act.
- Counterterrorism Efforts: Applications that involve obtaining information for national security purposes.
- Fraud Investigations: Cases where financial records are subpoenaed to investigate potential fraud.
Each example underscores the significant role these applications play in upholding federal law while balancing civil liberties.