Definition and Meaning
The concept of "2 A'4 2) 21,( 5')(+2,4 5+(7 ,8 '9( ')+6' (2 )2+8' 2) 77 ( - aikencountysc" does not appear to correspond directly to any commonly recognized form or document. It seems to be a sequence of fragmented letters, numbers, and symbols, lacking the coherent structure usually associated with official forms. This string could be mistaken for a scrambled or encoded message that doesn't offer direct insight but might contain meaningful data or instructions related to a specific context or system.
How to Interpret the Sequence
Understanding the sequence "2 A'4 2) 21,( 5')(+2,4 5+(7 ,8 '9( ')+6' (2 )2+8' 2) 77 ( - aikencountysc" requires analysis and contextual clues which are not immediately evident. If this sequence is part of a specific system or organization, cross-referencing with internal documentation may be necessary. It might involve:
- Translating any encoded data using an appropriate encryption or decoding method.
- Checking if it fits a pattern typical of a coding scheme in technical domains.
- Consulting with entities who regularly handle such sequences for guidance.
Legal Use and Considerations
The legal implications of using or referencing the sequence depend heavily on its context and intended purpose. Without clear identification, it is difficult to ascertain whether it holds any legal significance. Carefully examine if this sequence might relate to a legally bound document or system, and ensure compliance with national and local regulations:
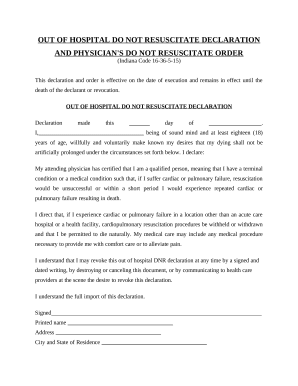
- Data Privacy: If related to personal data, ensure compliance with data protection laws.
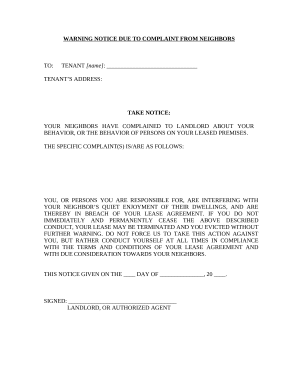
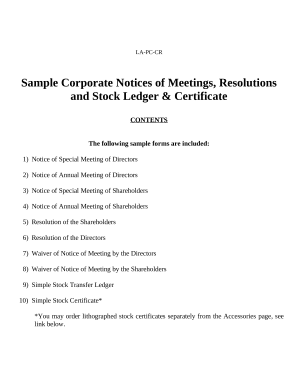
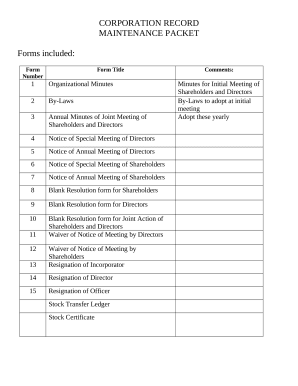
- Legal Documentation: Verify whether it pertains to or is a part of any legal formality.
- Authorized Use: Confirm that accessing or utilizing this sequence does not breach any agreements or proprietary systems.
Key Elements to Identify
Identifying the key components in "2 A'4 2) 21,( 5')(+2,4 5+(7 ,8 '9( ')+6' (2 )2+8' 2) 77 ( - aikencountysc" might help decode its intended use:
- Numerical Patterns: Look for sequences that might represent coded information.
- Symbol Functions: Consider any roles that symbols might play in specific coding languages or protocols.
- Contextual Clues: Use surrounding documentation or metadata where this sequence is found to provide further information.
Examples of Potential Uses
Since the exact use of the sequence is unclear, theoretical examples can only be hypothesized based on potential contexts such as:
- Tracking Codes: As seen in shipping or logistics industries.
- System References: In IT environments where sequences may align with system identifiers.
- Security Tokens: When related to encoded or encrypted security measures.
Required Documentation for Decoding
Effective analysis often involves compiling relevant documentation, such as:
- Decoding Manuals: Guides that may apply if this aligns with a known encoding system.
- Technical Specifications: Particularly if associated with software or IT systems.
- Legal Documentation: Relevant legal guidelines if this sequence is to be applied within a legal framework.
Software Compatibility Considerations
If it pertains to digital processing, understanding what software mechanisms might interpret this sequence is crucial:
- Encryption Software: To encrypt or decrypt if relevant.
- Data Management Systems: In case of integration with databases.
- Specialized Applications: Designed to manage or interpret specific sequence formats.
Eligibility for Use
Only authorized individuals or entities should use this sequence contextually where required. Without proper context:
- Verification: User eligibility must be cross-referenced with system requirements.
- Restrictions: Ensure no breach of access protocols.
- Security Checks: Implement standard security measures verifying person/entity access to sequence usage.
This structure integrates practical avenues of exploration for interpreting and utilizing the sequence provided.