Definition & Meaning of the HIPAA Breach Decision Tool and Risk Assessment Documentation
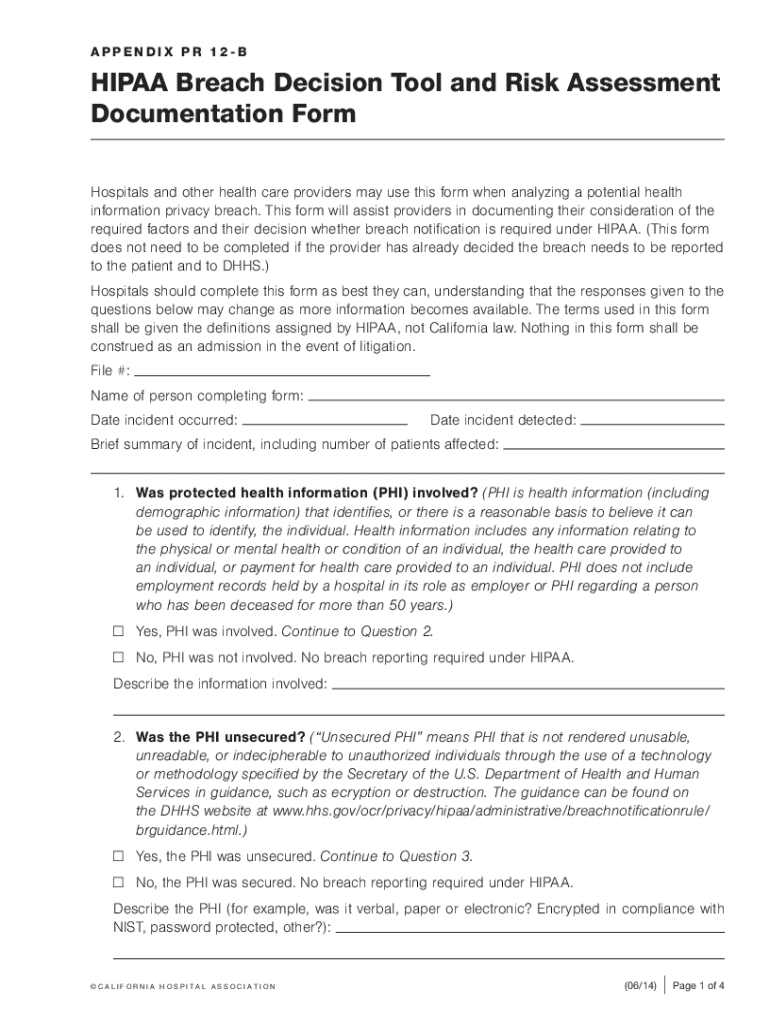
The HIPAA Breach Decision Tool and Risk Assessment Documentation serve as an essential resource for healthcare providers and organizations managing protected health information (PHI). It is designed to help users evaluate potential breaches of health information privacy according to HIPAA regulations, guiding them through critical decision points. The primary objective of the tool is to assess whether a breach notification is required and to determine the level of risk associated with the exposure of PHI.
The tool focuses on the security status of PHI, the context in which the information was exposed, and any applicable legal exceptions. By using this documentation, healthcare organizations can ensure compliance with HIPAA guidelines while maintaining the integrity and confidentiality of patient information.
Steps to Complete the HIPAA Breach Decision Tool and Risk Assessment Documentation
-
Identify the Type of Incident:
- Start by categorizing the nature of the incident. This includes understanding whether there was unauthorized access to PHI, unintentional disclosure, or loss of data.
- Determine if the information was encrypted or otherwise safeguarded at the time of the incident.
-
Evaluate the Extent of the Breach:
- Assess which PHI elements were involved, such as full names, Social Security Numbers, or medical records.
- Analyze how this information was accessed and who may have potentially seen or acquired it.
-
Assess the Risk of Harm:
- Evaluate any risk that the breach might cause to the individual whose information was exposed. Consider potential identity theft, financial fraud, or reputational damage.
- Take into account any past incidences or similar breaches to determine ongoing risks.
-
Determine Notifications:
- Based on the assessment, decide if notification to the affected parties, healthcare partners, or authorities such as the Department of Health and Human Services is necessary.
- Prepare communication strategies and documentation for those affected by the breach.
-
Document All Findings:
- Thoroughly record all findings, conclusions, and steps taken to mitigate the risk of the breach.
- Include a detailed account of how the breach was investigated, the risk analysis results, and the decision-making process regarding notifications.
Key Elements of the HIPAA Breach Decision Tool and Risk Assessment Documentation
-
Incident Description:
- A comprehensive narrative of the incident, including dates, how the breach was discovered, and preliminary actions taken.
-
PHI Impact Analysis:
- Detailed examination of the type and amount of PHI involved and an assessment of who might have access to it.
-
Risk Mitigation Measures:
- Strategies implemented to reduce the impact of the breach and prevent future occurrences, like strengthening security protocols.
-
Notifications & Communications:
- Lists of entities and individuals informed about the breach, along with copies of any communication sent.
-
Legal and Regulatory Compliance Check:
- Verification that all HIPAA regulatory requirements are met in the investigation and response efforts.
Who Typically Uses the HIPAA Breach Decision Tool and Risk Assessment Documentation
Healthcare organizations, including hospitals, clinics, and private practices, commonly utilize this tool. It is essential for compliance officers, data protection officers, and legal teams involved in safeguarding PHI. These stakeholders ensure that any potential breaches are identified promptly and managed according to federal regulations.


Legal Use of the HIPAA Breach Decision Tool and Risk Assessment Documentation
Using this documentation aligns healthcare entities with federal HIPAA requirements, helping them identify whether a breach requires regulatory notification. By ensuring that all necessary steps are taken and documented, organizations can defend against potential legal actions or penalties resulting from non-compliance. This serves as a legal record that due diligence was conducted in response to a PHI breach.
Important Terms Related to HIPAA Breach Decision Tool and Risk Assessment Documentation
-
Breach Notification Rule:
- A HIPAA regulation requiring covered entities to notify affected individuals and others in the event of a PHI breach.
-
Protected Health Information (PHI):
- Any information in a medical record that can be used to identify an individual and that was created, used, or disclosed in the course of providing healthcare services.
-
Encryption:
- Process of converting data into a coded form to prevent unauthorized access, often used as a mitigation measure in breach scenarios.
State-Specific Rules for the HIPAA Breach Decision Tool and Risk Assessment Documentation
Each U.S. state may have unique regulations that affect how breaches should be handled. Some states require additional notifications or impose stricter timelines for reporting breaches. Healthcare organizations must familiarize themselves with both federal HIPAA guidelines and any specific state laws to ensure full compliance when a breach occurs.
Examples of Using the HIPAA Breach Decision Tool and Risk Assessment Documentation
In a case where a hospital discovers unauthorized access to patient data, the Breach Decision Tool guides the compliance officer in making informed decisions about notifying patients and authorities. Another example might involve a healthcare provider inadvertently mailing patient records to the wrong recipient; the tool helps evaluate if the error constitutes a notifiable breach based on the exposure's risk level and the involved PHI.