Definition and Purpose of DD Form 2875
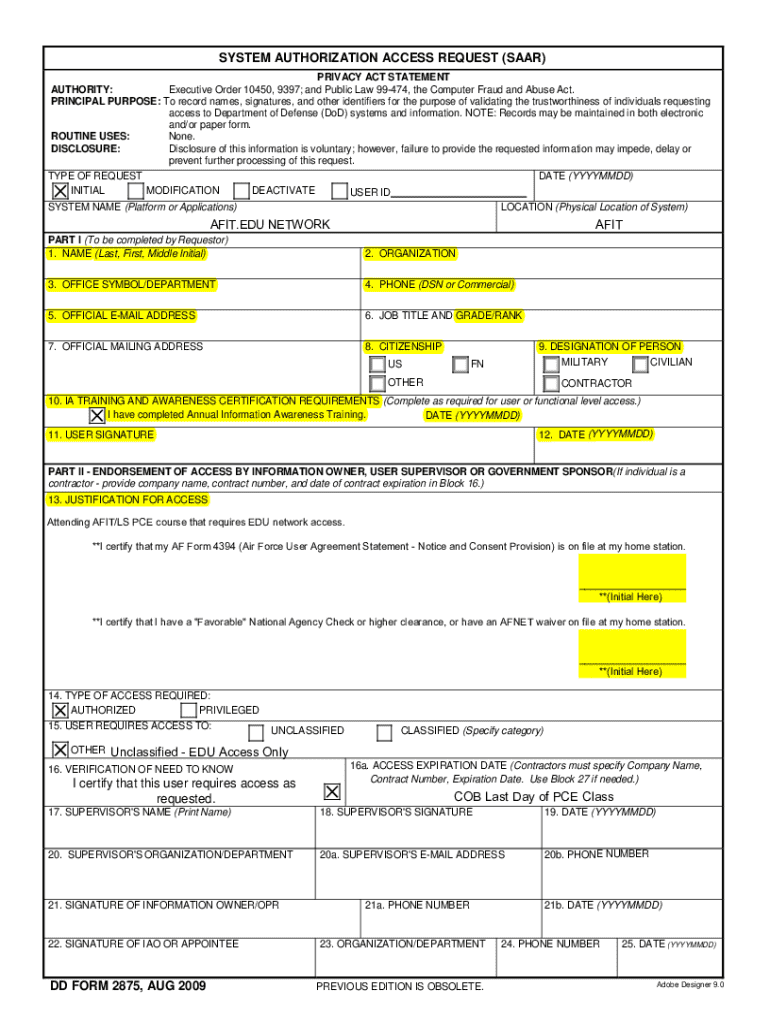
DD Form 2875, also known as the System Authorization Access Request (SAAR) form, is a standard document used by the United States Department of Defense (DoD) to request access to information systems. This form is essential for managing computer accounts, especially for individuals enrolled in specific military courses like AFIT/LS. It provides a secure procedure for granting and managing system access, ensuring that only authorized personnel can access sensitive information.
The form is crucial in maintaining cyber security within the DoD, facilitating controlled access to digital infrastructure. By using the DD Form 2875, the department can monitor and record access permissions, making it an integral part of the broader system of data protection and operational security.
How to Use DD Form 2875
To utilize DD Form 2875 correctly, applicants must first secure the form, typically available through their organization's designated channels or online through official DoD resources. The process involves several key steps, which require precise and secure handling to ensure that all information is correctly recorded and submitted.
Applicants need to accurately complete the form with personal and professional details, information about the systems they require access to, and any specific access privileges they need. It's vital to adhere to guidelines provided by supervisors or IT officers, as these instructions ensure the form is properly completed and accepted.
How to Obtain DD Form 2875
Obtaining DD Form 2875 is generally straightforward. The form can be downloaded from official DoD repositories or provided directly by an organization's IT department. It is critical to ensure that the latest version is used, as updates to the form may occur, reflecting changes in access protocols or security measures.
In most cases, the form is distributed to personnel who are new to a system or whose access privileges need updating. Individuals should follow their department's protocol for obtaining and submitting the form to ensure that it is processed in a timely and proper manner.
Steps to Complete DD Form 2875
Completing DD Form 2875 involves a structured process:
- Provide Personal Information: Fill in your name, rank, and contact details.
- Identify System Requirements: Specify the information systems you need access to, detailing the level of access required.
- Justify Access: Include a rationale for why access is necessary and any specific duties that require system use.
- Complete Security Modules: Ensure you have completed all required security training as outlined by DoD guidelines.
- Obtain Authorizations: Get necessary approvals and signatures from designated authorities, such as a supervisor or IT officer.
- Submit Form: Send the completed form to your department's IT office, following any additional submission requirements.
These steps are critical in ensuring the proper use of the form and securing system access within DoD regulations.
Who Typically Uses DD Form 2875
DD Form 2875 is primarily used by military personnel, including active-duty members and civilians working within DoD environments. It is also essential for contractors and vendors who require access to specific information systems to perform their duties. Additionally, those working in cybersecurity and system administration roles frequently encounter this form as part of standard access management protocols.
The form ensures that individuals who need to access information systems are adequately vetted and authorized, maintaining the integrity and confidentiality of DoD operations.
Key Elements of DD Form 2875
Understanding the critical components of DD Form 2875 is essential for its correct completion:
- Part I: User information and system requirements, detailing personal data and the systems for which access is requested.
- Part II: Security clearance and access requirements, ensuring alignment with security protocols.
- Part III: Authorizations, approvals, and signatures from commanding authorities, confirming the validity of the request.
Each element plays a significant role in the authorization process and is vital for maintaining secure access to information systems.
Security and Legal Considerations
The legal use of DD Form 2875 involves stringent adherence to data protection laws and security regulations set forth by the DoD. Applicants must ensure that all personal and professional information submitted aligns with legal requirements, and any violations or inaccuracies could result in denied access or disciplinary action.
The form serves as a legal document, tracking and authorizing access to secure systems, and must be handled with confidentiality and accuracy to prevent unauthorized access and maintain compliance with security standards.
Digital vs. Paper Version
DD Form 2875 is often available in both digital and paper formats, with the choice of submission often depending on departmental preferences and infrastructure capabilities. While the paper version is traditional, digital submissions are increasingly common, offering benefits such as ease of access, quick transmission, and better record management.
When opting for a digital version, ensure compatibility with your department's software and submission portals to avoid delays or processing errors. Both versions require careful completion to ensure security and system access permissions are properly managed.