Definition and Meaning of Call Key
The term "Call Key" refers to a critical element within specific documentation procedures, often used in contexts requiring thorough identification or verification processes. It represents a unique identifier or access point integral to executing particular transactions or facilitating communication within a system. In scenarios where documentation requires security and authenticity, the Call Key functions as a gatekeeper, ensuring only authorized users can interact with certain data or perform specific actions.
Usage Contexts
- Security Protocols: In digital systems, the Call Key acts as an essential access credential.
- Document Verification: It plays a pivotal role in verifying document authenticity, preventing unauthorized access.
Obtaining the Call Key
Acquiring a Call Key generally involves a series of formal steps depending on the governing body's requirements or the specifics of the application process. The following outlines typical methodologies.
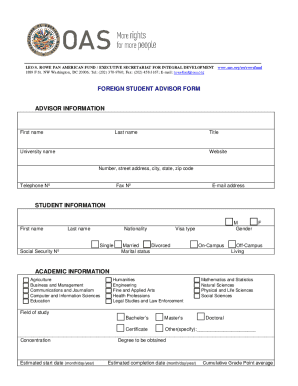
General Process
- Application Submission: Submit a formal application to the relevant authority requesting a Call Key.
- Verification of Identity: Provide documentation to verify identity and eligibility.
- Approval: Await approval from the governing body, which may include background checks.
- Issuance: Receive the Call Key through a secure, predefined channel.
Documentation Requirements
- Valid identification proof
- Supporting documents corroborating the necessity of a Call Key
- Organizational credentials if applicable
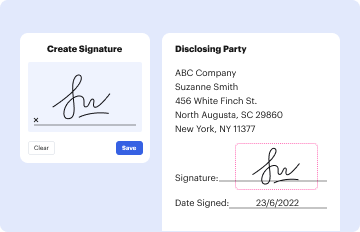
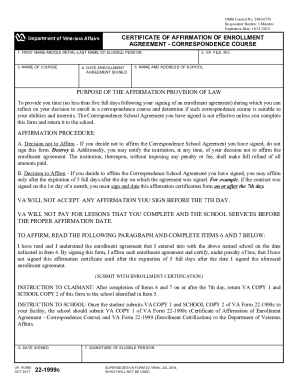
Steps to Complete the Call Key
Completing the Call Key involves fulfilling specific procedural requirements to enable its function within a designated system.
Detailed Procedure
- Initiate Request: Contact the issuing authority to express the intention to complete a Call Key.
- Fulfill Prerequisites: Ensure all necessary conditions and documentation are prepared and verified.
- System Integration: Follow the outlined integration processes, which may involve software or digital platform involvement.
- Final Confirmation: Conduct a thorough review with the issuing authority to confirm successful completion.
Considerations
- Ensure timely submission of all required elements.
- Maintain transparency and communication with the issuing body throughout the process.
Important Terms Related to Call Key
Understanding the relevant terminology is crucial for navigating the complexities involved with Call Keys.
Key Terms
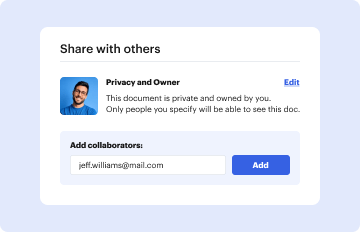
- Authentication: The process of verifying an individual's identity before access is granted.
- Access Control: Mechanisms that manage who can view or use resources in a computing environment.
- Verification Code: A secondary layer of security providing further authentication.
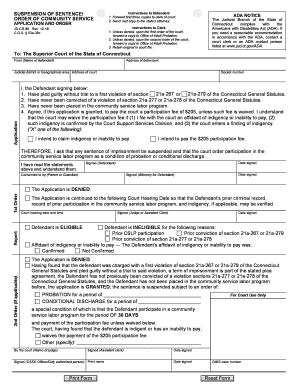
Legal Use of the Call Key
The legal utilization of a Call Key is pivotal as it delineates permissible actions within compliance frameworks established by the issuing authority or relevant legislation.
Compliance Guidelines
- Adherence to Regulation: Ensure all Call Key activities comply with federal and state regulations.
- Documentation: Maintain accurate records of all actions taken using the Call Key for accountability.
- Usage Boundaries: Clearly understand and respect the Call Key's operational limits to avoid legal repercussions.
Examples of Using the Call Key
Real-world applications of the Call Key can illustrate its versatility and functionality within various environments.
Scenarios
- Corporate Sector: Used to facilitate secure transactions within financial institutions.
- Healthcare Systems: Allows for secure access to patient records by authorized medical personnel.
- Educational Institutions: Provides access control to digital platforms containing sensitive student data.
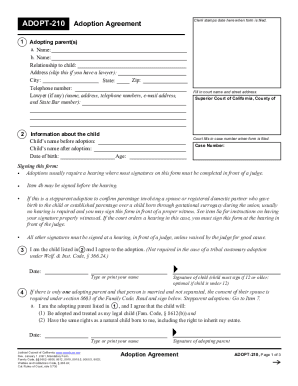
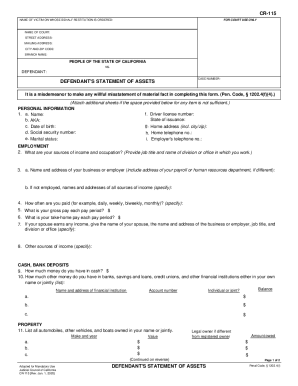
Required Documents for Call Key
Certain documents must be prepared and submitted to ensure successful Call Key application and usage.
Essential Documentation
- Identification Documents: Such as a driver's license or passport.
- Proof of Address: Verified through utility bills or lease agreements.
- Organizational Authorization: For business-specific Call Keys, providing proof of organizational legitimacy.
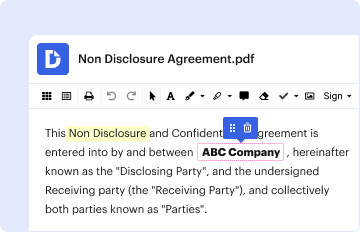
Software Compatibility
Ensuring that the Call Key is compatible with necessary software systems is critical for seamless functionality.
Compatible Platforms
- Document Management Systems: Platforms like TurboTax and QuickBooks often support Call Key integration.
- Security Suites: Software designed to protect digital transactions might require Call Keys for enhanced security.
- Cloud Integration: Works with cloud services, facilitating secure data access and processing.
State-Specific Rules for Call Key
Regulations concerning the Call Key may vary by state, highlighting the importance of awareness regarding local legislation.
State Variabilities
- Differing Approval Processes: Some states may require additional steps or specific documentation for Call Key acquisition.
- Regulatory Compliance: Be mindful of state-specific regulations that can affect the issuance or use of a Call Key.
Penalties for Non-Compliance
Non-compliance with Call Key regulations can lead to significant penalties reflecting both legal and financial repercussions.
Potential Consequences
- Fines: Monetary penalties imposed for unauthorized or inappropriate use.
- Revocation: Loss of Call Key privileges due to non-compliance.
- Legal Action: Potential for lawsuits or other legal actions if compliance violations are severe.
Ensuring you are fully informed and prepared in regard to the Call Key can significantly enhance your capacity to use it effectively within your designated context. Comprehensive understanding of the processes, legalities, and implications allows for better management and application of this essential tool.