Definition & Meaning
Understanding the "request for proposal security guard services standard contract" involves recognizing it as a formal document used by organizations to solicit bids from potential vendors or service providers. This contract standardizes the process for government agencies or private entities to outline the expectations, requirements, and scope of security guard services, ensuring a structured approach to evaluating and selecting qualified vendors. The main goal is to obtain competitive bids while maintaining transparency and compliance with regulatory standards.
How to Use the "Request for Proposal Security Guard Services Standard Contract"
Organizations intending to procure security guard services should use this contract as a framework to communicate their requirements clearly. They begin by detailing the scope of services needed, including specific security roles, expected shift schedules, and service areas. This document serves to invite qualified vendors to submit proposals that meet these stipulations. It is crucial for organizations to articulate evaluation criteria and outline how proposals will be judged, such as cost-effectiveness, vendor experience, or service quality.
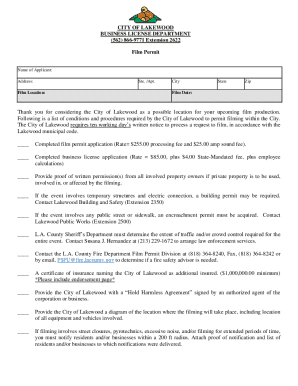
How to Obtain the "Request for Proposal Security Guard Services Standard Contract"
To access this contract, interested parties typically visit the official state procurement website or consult with authorized procurement offices. Many state agencies provide downloadable versions that can be customized to fit specific needs. For businesses unfamiliar with navigating government websites, collaborating with legal consultants or procurement specialists can be helpful. These professionals often have the expertise to locate the appropriate document and assist in initial deployment.
Steps to Complete the "Request for Proposal Security Guard Services Standard Contract"
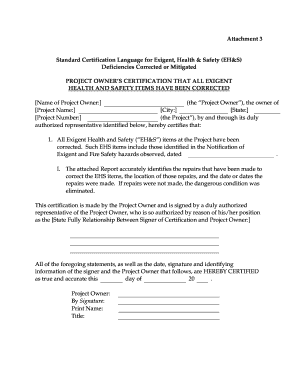
- Review the Contract Template: Before completion, thoroughly study the existing template to understand its structure and required fields.
- Customize Service Details: Input specific information about the services required, including the types of security roles and hours needed.
- Specify Evaluation Criteria: Clearly define how proposals will be assessed. This could include price, past performance, and specific qualifications.
- Set Response Deadlines: Provide clear timelines for proposal submission and indicate deadlines for vendor queries and final proposals.
- Finalize and Approve: Ensure the contract is reviewed and approved by appropriate organizational authorities before distribution to vendors.
Key Elements of the "Request for Proposal Security Guard Services Standard Contract"
- Scope of Services: Outlines the specific duties and responsibilities of security personnel, including patrol, surveillance, and emergency response.
- Pricing Structure: Specifies how pricing will be evaluated, whether on a fixed-price basis or using cost-plus arrangements.
- Terms and Conditions: Includes clauses on confidentiality, performance standards, and liability insurance requirements.
- Selection Criteria: Details the metrics that will be used to evaluate vendor proposals, such as compliance with security regulations and overall cost.
- Contract Duration: Defines the length of service and any options for renewal or termination.
Important Terms Related to the "Request for Proposal Security Guard Services Standard Contract"
Understanding certain terms can enhance clarity when dealing with this contract:
- Vendor: The service provider or contractor submitting a proposal for consideration.
- Bid: The proposal submitted by a vendor in response to the RFP.
- Scope of Work: The detailed description of services to be executed by the contractor.
- Evaluation Committee: A group within the procuring organization responsible for reviewing and scoring vendor submissions.
- Award Notification: Formal communication indicating the selection of a vendor after the evaluation process.
State-Specific Rules for the "Request for Proposal Security Guard Services Standard Contract"
Different states may have unique regulations and requirements:
- California: Requires specific compliance with state privacy laws and mandates background checks for security personnel.
- New York: Enforces rigid adherence to state labor laws including prevailing wage considerations.
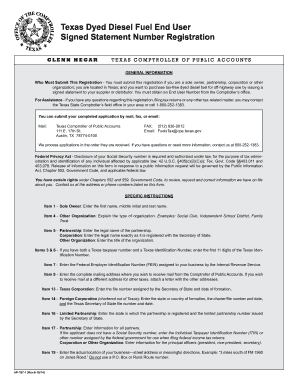
- Texas: Often requires vendors to be registered with the state’s procurement division and can necessitate additional certifications based on service scope.
- Florida: May include additional public safety requirements due to tourism considerations.
Examples of Using the "Request for Proposal Security Guard Services Standard Contract"
Several scenarios exemplify the practical applications of this contract:
- Municipal Use: A city government seeking to outsource security at public parks utilizes this contract to solicit bids from local security companies.
- Corporate Needs: A national retailer issues an RFP to enhance its security presence at multiple locations across a specific region, ensuring a standardized security protocol is applied companywide.
- Educational Institutions: Universities looking to enhance campus safety might deploy the contract to engage security services that align with federal education safety mandates.