Definition & Meaning
The "Revised: August 19, 2008 - Technology Services - The College of" form refers to a document updated on August 19, 2008, focusing on the technology services provided by a particular college. This form is likely used to detail the technological infrastructure, services, and policies present at the institution. It might include guidelines for using college networks, accessing electronic resources, and complying with IT policies.
Key Elements of the Form
The form typically includes several important components designed to provide comprehensive coverage of IT services. Key elements often encompass:
- Network Usage Policies: Guidelines on how institutional networks should be accessed and used.
- Resource Access: Instructions for accessing digital libraries, databases, and other technology resources essential for academic or professional purposes.
- User Responsibilities: A section detailing the obligations of students, faculty, and staff in maintaining the integrity and security of college IT systems.
- Support Services: Information about available IT support, help desks, and troubleshooting resources.
How to Use the Form
To effectively use the "Revised: August 19, 2008 - Technology Services - The College of" form, follow these steps:
- Familiarize Yourself with the Content: Review each section to understand all policies and instructions clearly.
- Adhere to Network Policies: Ensure you follow the network usage guidelines to maintain compliance.
- Access Resources as Needed: Use the instructions to access institutional resources effectively.
- Seek Support for Issues: Contact the IT support services if you encounter any technical difficulties while using college technology systems.
Steps to Complete the Form
Completing this form requires careful attention to detail and adherence to its instructions:
- Read All Instructions Thoroughly: Begin by reading all guidelines to fully understand requirements.
- Provide Accurate Information: Fill in any required fields accurately (e.g., personal details, student/faculty ID).
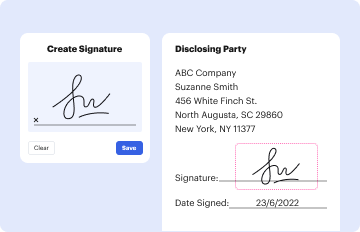
- Acknowledge Understanding: Where applicable, sign sections to confirm understanding of and compliance with technology policies.
- Submit as Instructed: Follow any final steps regarding submission, whether it needs to be handed in, logged online, or kept for personal reference.
Who Typically Uses the Form
This form is usually utilized by a wide array of college stakeholders, including:
- Students: Primarily responsible for adhering to IT usage guidelines to ensure smooth access to educational resources.
- Faculty and Staff: Utilize the form to understand and comply with technology usage policies while engaging in their work or academic duties.
- IT Department: Uses the form to standardize technology service delivery and ensure all users comply with institutional policies.

Legal Use of the Form
The form serves as a legal document that both outlines the permissible use of college IT resources and highlights the consequences of misuse. Users may be required to sign the form as a testament to their understanding and agreement to abide by these regulations, acting as a legal contract between the user and the institution.
Software Compatibility
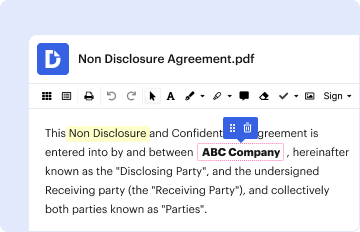
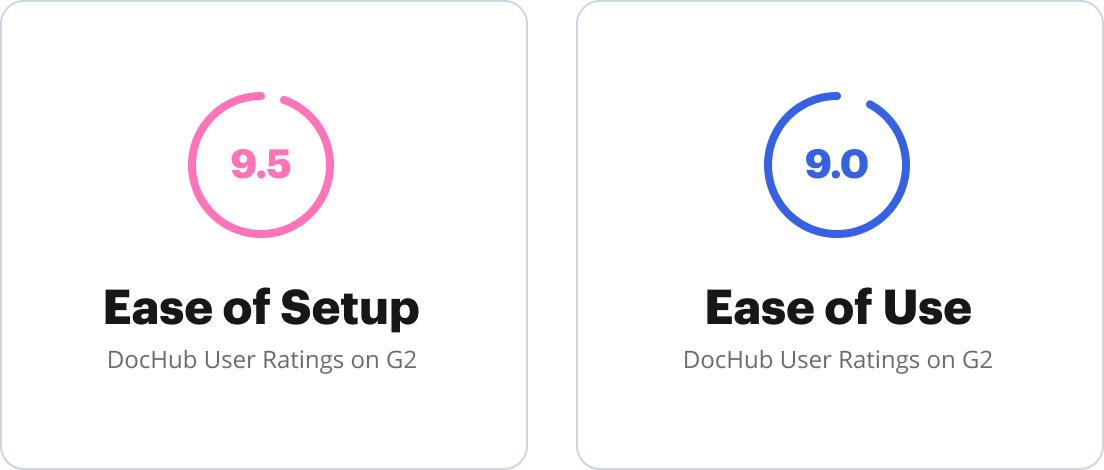
For those who need to complete or manage the form digitally, compatibility with software systems is crucial:
- Common Software: Many users can access and fill out this form using PDF readers, online form-filling platforms, or institutional tools provided by the college's IT department.
- Integration with EdTech Tools: Integration with educational technology tools might be possible, linking the form with platforms such as learning management systems (LMS) for easier access and submission.
Examples of Using the Form
Real-world scenarios where this form is essential include:
- New Student Orientation: Students are often required to complete the form to get network access.
- IT Incident Accountability: If there is an IT-related incident, this form is referenced to ascertain whether policies were followed.
- Resource Access Authorization: Faculty members needing specific software access for courses may need to submit this form to gain the necessary permissions.
Form Submission Methods
Multiple submission avenues are typically available:
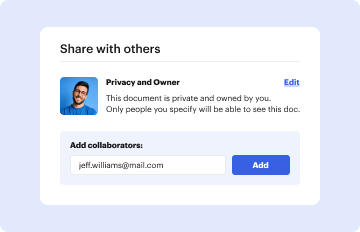
- Online Platforms: Users can often submit forms through online college portals.
- Physical Submission: In certain instances, a printed and signed version might be required to be handed in at the IT department.
- Email Submission: Some institutions allow electronic submission via email, attaching the completed form.
Penalties for Non-Compliance
Failure to adhere to the directives outlined in the form can lead to various penalties:
- Access Revocation: Immediate suspension or revocation of network access and IT services.
- Disciplinary Action: Possible disciplinary measures in line with college regulations, impacting academic standing or employment.
- Legal Repercussions: In severe cases, legal action might be pursued for significant breaches of policy or network misuse.
State-Specific Rules for the Form
Depending on the college's location, there may be variations in the form due to state-specific educational regulations:
- Data Protection Laws: Varying state laws regarding data protection may influence the form's content on privacy and user data.
- Acceptable Use Policies: State laws may dictate additional acceptable use guidelines, reflected in the form to ensure local legal compliance.