Definition and Purpose of the Bomb Threat Checklist
A bomb threat checklist is a crucial document used to guide individuals through the appropriate response during a bomb threat situation, particularly when the threat is received via phone call. This form includes specific questions designed to capture detailed information from the caller such as the location, time, and nature of the threat. It also prompts the user to note background sounds and the characteristics of the caller’s voice. Beyond its primary function, the checklist emphasizes the prompt need to contact authorities to ensure safety and timely intervention.
How to Use the Bomb Threat Checklist Word Document
To effectively use a bomb threat checklist, it is important first to understand the layout and components of the document. Users should familiarize themselves with the sections that pertain to obtaining details from the caller. When a threat is received, individuals should remain calm and listen carefully. As you fill out the checklist, ask the caller direct questions listed in the document, ensuring to write down exact words used. Additionally, make observations about background noises and voice characteristics. Once the information is gathered, immediately contact local law enforcement and provide them with the completed checklist for further investigation.
Detailed Steps for Completing the Checklist
- Stay calm and document the exact time of the call.
- Use the checklist to ask the provided questions about the location, type, and timing of the bomb.
- Note the caller's voice characteristics and any background noises.
- Document your observations thoroughly and accurately.
- Contact local authorities immediately with the completed checklist.
Key Elements of the Bomb Threat Checklist
The bomb threat checklist contains several essential elements designed for thorough information gathering:
- Exact wording of the threat: Capture the precise language used by the caller.
- Voice characteristics: Note if the voice is calm, angry, accented, or any other distinguishable features.
- Background noises: Identify and document sounds like traffic, machines, or people during the call.
- Caller ID and phone number: Record if visible or obtained.
- Questions asked: Follow the guide for specific questions about the bomb, such as its location, appearance, and timing.
Who Typically Uses the Bomb Threat Checklist
Typically, bomb threat checklists are used by organizations such as schools, businesses, and government agencies. Security personnel, receptionists, or anyone who may potentially receive a threatening call are the primary users of this document. Training on recognizing and responding to threats can be enhanced by familiarizing personnel with the checklist, ensuring they are prepared to act swiftly and accurately in stressful situations.

Legal Use of the Bomb Threat Checklist
The bomb threat checklist serves a critical role in ensuring that responses to threats are systematic and legal. Gathering detailed information is crucial for law enforcement to investigate, and the checklist helps organizations to maintain a record of all incidents. By following the checklist, organizations exhibit due diligence, a critical aspect often required in legal proceedings or insurance claims relating to threat management.
Examples of Using the Bomb Threat Checklist
Real-world cases demonstrate the utility of the bomb threat checklist in effectively managing and mitigating potential threats. For instance, in a corporate context where a bomb threat is called in, employees trained with the checklist captured vital information that assisted law enforcement, preventing potential harm. Schools also frequently use such checklists during bomb drills to practice preparedness and ensure everyone knows their roles during an actual event.
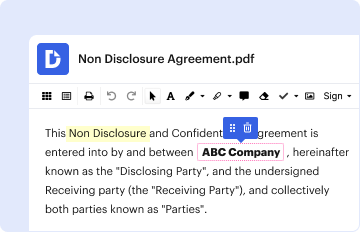
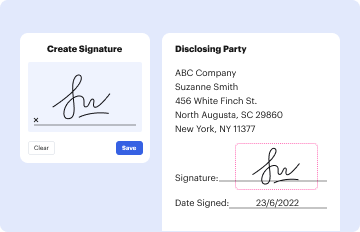
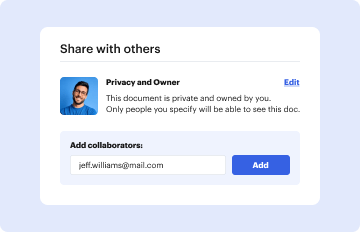
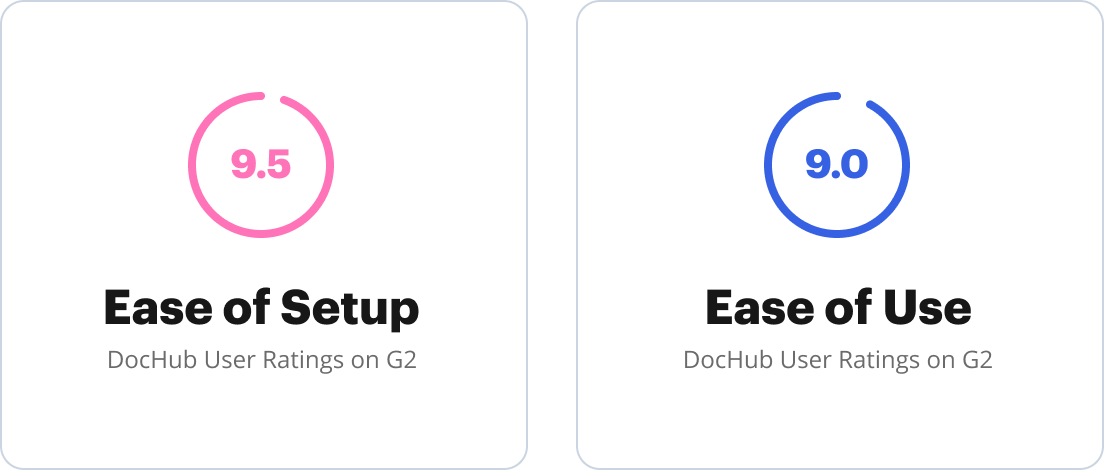
Software Compatibility and Integration
Bomb threat checklists in word document format are compatible with various document editing software. Platforms like DocHub allow for easy integration and modification of these documents, enabling users to customize the checklist to fit specific needs. This allows organizations to update and distribute the document swiftly across their networks. Due to the document's Word format, it's also readily editable on common software like Microsoft Word or Google Docs, facilitating widespread accessibility and versatility.
Versions and Alternatives to the Bomb Threat Checklist
There are multiple versions of bomb threat checklists available, varying in complexity and detail based on industry needs. Some organizations may choose to adopt security agency-approved checklists or develop customized versions that align with their specific protocols. Alternatives may include digital checklists integrated into security systems or apps designed to allow quicker sharing with authorities. Organizations can also complement the checklist with training sessions and digital simulations to prepare employees effectively.