Definition & Meaning
The "Breach Notification - CIO - cio wisc" is essential for informing affected parties about breaches involving protected data. Under the Health Information Technology for Economic and Clinical Health Act (HITECH Act), this form details the requirements for notifying individuals, the Department of Health and Human Services (HHS), and, when necessary, the media, whenever a breach of unsecured protected health information occurs. Designed for compliance, it outlines how entities should address the handling and notification process to ensure adherence to legal obligations.
Key Elements of the Breach Notification - CIO - cio wisc
At its core, the breach notification form encompasses several critical elements, including the:
- Identification of Breach: Clearly outlines what constitutes a data breach under the regulatory framework.
- Notification Requirements: Establishes who needs to be notified and the timeline for doing so.
- Understanding of Exceptions: Covers situations that may not be classified as breaches, providing clarity on what falls outside the scope.
- Burden of Proof: Specifies the necessity for entities to demonstrate compliance with notification requirements, including maintaining records of notifications issued.
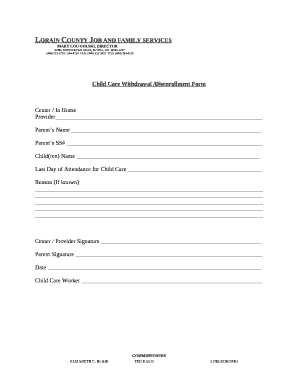
Steps to Complete the Breach Notification - CIO - cio wisc
- Identify the Breach: Confirm that a breach involving unsecured protected data has occurred.
- Determine Scope: Assess the extent and impact of the breach, including the information affected and the potential risks to individuals.
- Prepare Notifications: Draft notifications for affected individuals, including details about the breach, potential consequences, and steps individuals can take to protect themselves.
- Notify Authorities: Inform the Secretary of HHS according to the established timelines. In some cases, notify media outlets if a significant number of individuals are affected.
- Document Procedures: Maintain detailed records of all actions taken in response to the breach to demonstrate compliance with the HITECH mandates.
How to Obtain the Breach Notification - CIO - cio wisc
The form can typically be obtained from the responsible regulatory body, such as the Department of Health Services or through the internal security or compliance department within your organization. Additionally, organizations may have internal versions of the form tailored to align with specific operational processes and institutional legal advice.
Legal Use of the Breach Notification - CIO - cio wisc
Legally, the notification form is used to ensure compliance with the HITECH Act's requirements. It serves as a formal document representing an organization's commitment to transparency and regulatory adherence concerning data breaches. Failure to use and submit this notification properly can result in significant legal penalties and reputational damage.
Important Terms Related to Breach Notification - CIO - cio wisc
- Unsecured Protected Information: Data that is not protected through methods like encryption or destruction.
- Notice of Breach: A formal communication issued when a data breach occurs.
- Covered Entities: Organizations covered under the Health Insurance Portability and Accountability Act (HIPAA), which may include healthcare providers, health plans, and healthcare clearinghouses.
- Business Associates: Third-party organizations that perform activities involving protected health information on behalf of a covered entity.
Who Typically Uses the Breach Notification - CIO - cio wisc
Primarily, this form is used by organizations that handle sensitive health information, including healthcare providers, insurance companies, and their business associates. Responsible parties, such as Chief Information Officers (CIOs) or compliance officers, are usually tasked with overseeing the completion and submission of this notification to meet regulatory standards.


Penalties for Non-Compliance
Non-compliance with breach notification requirements can result in severe penalties. These may include monetary fines, legal action, and damage to the organization's reputation. Fines are tiered based on the level of negligence, with penalties increasing for willful neglect and failure to correct the breach in a timely manner. These consequences underline the importance of adhering strictly to legislative mandates regarding breach notifications.
Examples of Using the Breach Notification - CIO - cio wisc
Consider a scenario where an unauthorized person gains access to a patient's medical records. The organization must issue a breach notification to the individual affected, and potentially to HHS and the media, depending on the size of the breach. The notification should include what happened, what information was breached, potential consequences, and actions being taken to prevent future occurrences. Through real-world examples, organizations can recognize potential areas of vulnerability and improve their data protection strategies.
Versions or Alternatives to the Breach Notification - CIO - cio wisc
Though the primary focus is on the standardized form, organizations might have tailored versions that fit their specific operational framework or comply with additional state laws. Some entities might integrate this form within broader compliance documentation practices, ensuring alignment with other regulatory requirements at both federal and state levels to mitigate risks effectively.
The comprehensive approach to highlighting each aspect of the "Breach Notification - CIO - cio wisc" ensures that organizations are prepared to handle data breaches, safeguarding both their interests and the privacy of individuals affected.