Definition & Meaning of Littlest Hostages' - E-Research
The term "Littlest Hostages' - E-Research" pertains to an investigative or analytical process that studies the experiences and issues concerning vulnerable populations often metaphorically referred to as the "little hostages," possibly children or individuals in situations beyond their control. This form functions as a tool or guide within the realm of electronic research, allowing for the collection and analysis of relevant data. The scope of e-research extends across multiple disciplines and involves digital methodologies to explore complex topics systematically.
How to Use the Littlest Hostages' - E-Research
To effectively utilize the Littlest Hostages' - E-Research form, users should follow a structured approach that includes preparation, data collection, analysis, and reporting. This guide helps standardize methodology, ensuring consistency and reliability in findings.
-
Preparation:
- Identify clear research objectives.
- Gather necessary background information.
-
Data Collection:
- Use ethically approved methods.
- Employ digital tools to gather relevant data.
-
Analysis:
- Employ statistical or qualitative analysis tools.
- Interpret findings with consideration of context and bias.
-
Reporting:
- Compile data into comprehensive reports.
- Use visual aids to summarize key findings.
Steps to Complete the Littlest Hostages' - E-Research
Completing the Littlest Hostages' - E-Research involves a series of methodical steps that ensure comprehensive coverage and accurate data capture. Follow these steps for effective completion:
-
Understand the Purpose:
- Define what you aim to discover or verify.
-
Gather Materials:
- Collect all necessary software and questionnaires.
-
Employ Research Techniques:
- Choose appropriate digital tools for data acquisition.
-
Conduct Surveys and Interviews:
- Use electronic forms to capture participant responses effectively.
-
Evaluate Data for Accuracy:
- Check for completeness and consistency in responses.
-
Draw Conclusions:
- Synthesize results to produce actionable insights.
Who Typically Uses the Littlest Hostages' - E-Research
The Littlest Hostages' - E-Research is typically utilized by professionals in social sciences, human rights agencies, and educational institutions. These users analyze data to inform policy decisions, enhance program effectiveness, or contribute to scholarly research. The flexibility and digital nature of the form make it particularly beneficial for:
-
Researchers:
- Conduct comprehensive studies on societal issues.
-
Policy Makers:
- Formulate data-driven policies that address human rights and welfare.
-
Non-Governmental Organizations (NGOs):
- Tailor interventions for vulnerable groups based on empirical evidence.

Legal Use of the Littlest Hostages' - E-Research
The legal use of Littlest Hostages' - E-Research involves complying with ethical guidelines and privacy laws to protect the data used. Users must ensure they are:
-
Adhering to Data Privacy Laws:
- Follow regulations such as GDPR for handling personal data.
-
Obtaining Informed Consent:
- Secure permissions from participants before data collection.
-
Ensuring Data Security:
- Utilize encryption and secure storage to protect sensitive information.
-
Following Institutional Review Board (IRB) Protocols:
- Obtain approval for research involving human subjects when necessary.
Key Elements of the Littlest Hostages' - E-Research
Critical elements that form the foundational components of the Littlest Hostages' - E-Research include:
-
Objective Definition:
- Clear articulation of research intents and goals.
-
Ethical Frameworks:
- Guidelines ensuring ethical research practices.
-
Data Collection Tools:
- Software and methodologies tailored for accurate information gathering.
-
Analytical Methods:
- Statistical or content analysis techniques for data interpretation.
-
Report Generation:
- Frameworks for compiling and reviewing research findings.
State-Specific Rules for the Littlest Hostages' - E-Research
State-specific rules may dictate variations in the implementation of the Littlest Hostages' - E-Research. Researchers must be aware of regional regulations, which can include:
-
Differing Privacy Legislation:
- Variations such as California's rigorous privacy standards affect data handling.
-
Institutional Requirements:
- State institutions may have additional compliance protocols.
-
Ethical Review Boards:
- Some states necessitate local IRB oversight for all research activities.
Recognizing these nuances ensures compliance and enhances the research's credibility.
Software Compatibility with Digital E-Research
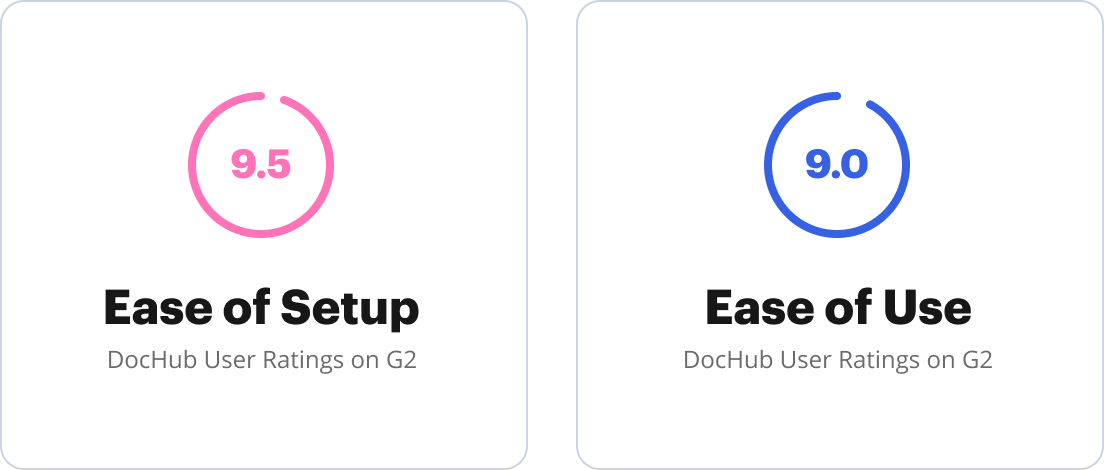
Using the right software is crucial for the seamless execution of Littlest Hostages' - E-Research. Compatibility with platforms like DocHub ensures:
-
Integration with Existing Systems:
- Platforms such as Google Workspace enhance efficiency.
-
User-Friendly Interfaces:
- Simplifies data entry and management processes.
-
Compatibility with Analytical Tools:
- Integration with software like SPSS or R for advanced data analysis.
Researchers should confirm compatibility before selecting their digital tools to streamline the research process.









