Definition & Meaning
In the context of secure file handling and verification, "if you confirm that the file is coming from a trusted source, you can send the following SHA-256 hash" refers to the process used to ensure a file's integrity and authenticity. A SHA-256 hash is a cryptographic function that produces a fixed-size string representation of a file's contents. When a file is confirmed as originating from a trusted source, sending the corresponding SHA-256 hash allows recipients to verify the file's integrity. By comparing the received hash with the computed hash on their end, recipients can confirm if the file has been altered in transit.
SHA-256 Hash Characteristics
- Fixed Output: The SHA-256 algorithm generates a 64-character string, regardless of file size.
- Collision Resistance: It is unlikely for two different files to produce the same hash.
- Immutability: An alteration in the file will result in a completely different hash.
How to Use the SHA-256 Hash Confirmation
Using the SHA-256 hash to confirm a file's origin involves verifying that the file has not been tampered with. When you confirm that the file is from a trusted source, you can provide the hash to the recipient. The recipient then generates the hash for the received file and compares it to the one provided. If both hashes match, the file is confirmed as unaltered.
Step-by-Step Verification Process
- Generate Hash: Use a hashing tool to generate the SHA-256 hash of the file.
- Share Hash: Send the generated hash to the recipient using a secure channel.
- Recipient Verification: The recipient calculates the SHA-256 hash of the received file.
- Comparison: Compare the hashes. If they match, the file is confirmed as unchanged.
How to Obtain the SHA-256 Hash
To obtain a SHA-256 hash for a file, you need to use specific software or tools designed for this purpose. Many operating systems come with built-in command-line utilities, and there are various third-party applications available.
Tools and Software
- Command Line:
- Windows:
certutil -hashfile [file_path] SHA256 - macOS:
shasum -a 256 [file_path] - Linux:
sha256sum [file_path]
- Windows:
- Third-Party Applications: Applications like HashCalc or Online Hash Crack.
Steps to Complete the SHA-256 Hash Process
Completing the hash verification process involves a few crucial steps, from file selection to final confirmation.
- Select File: Choose the file from a trusted source.
- Generate Hash: Use command-line tools or applications to derive the SHA-256 hash.
- Secure Transfer: Share the hash with the recipient securely.
- Recipient Verification: The recipient computes the file's hash and compares it.
- Confirmation: Ensure the recipient communicates the match or discrepancy.
Why Confirm File Integrity with SHA-256
Confirming file integrity using SHA-256 is essential in safeguarding against corruption and tampering. It is commonly used in digital contracts, software distribution, and financial documents.
Benefits
- Security: Ensures file content has not been altered.
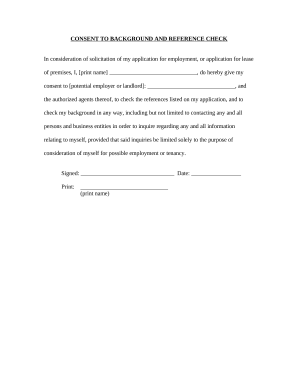
- Trust: Establishes reliability between communicating parties.
- Compliance: Meets legal requirements for integrity verification processes.
Legal Use of SHA-256 Hashes
The use of SHA-256 hashes is legal and often required for compliance in various sectors. This includes industries such as finance, healthcare, and government agencies where data integrity is paramount.
Compliance and Regulation
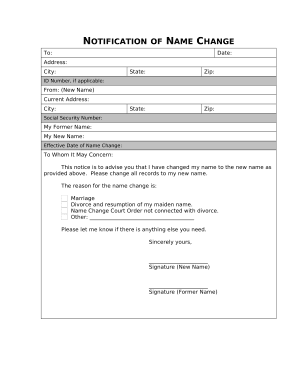
- Financial Services: Required for secure transaction verification.
- Healthcare: Used to protect sensitive patient data under HIPAA.
- Government: Ensures document integrity in regulatory submissions.
Key Elements of SHA-256 Verification
Several key elements underpin the effective use of SHA-256 hash verification in secure communications.
Elements
- Hash Generation: Proper generation of a correct hash string.
- Secure Communication: Safe sharing of the hash value.
- Integrity Verification: Accurate matching of source and received hash.
Examples of Using SHA-256 Hash Verification
Real-world examples illustrate the practical use of SHA-256 hash verification in daily operations.
Use Cases
- Software Distribution: Verifying download integrity of software packages.
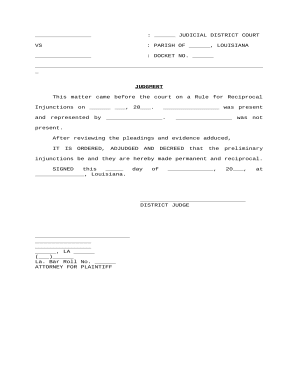
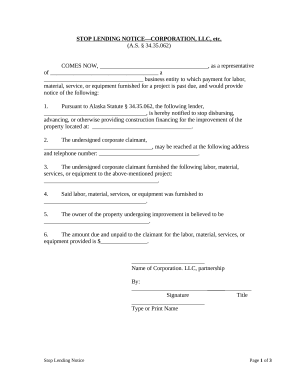
- Legal Documents: Ensuring the integrity of contracts or agreements.
- Email Attachments: Confirming that digital attachments remain untouched.
Important Terms Related to SHA-256
Understanding related terminology is crucial for grasping the full scope of SHA-256 utilities.
Key Terms
- Cryptography: The practice of secure communication using codes.
- Hash Function: Algorithm that converts an input into a fixed-length string.
- Nonce: A random number used once when generating a unique hash.
This comprehensive coverage ensures a thorough understanding of how to use and verify files using SHA-256 hashes, enhancing document security and preventing unauthorized alterations.