Definition & Meaning
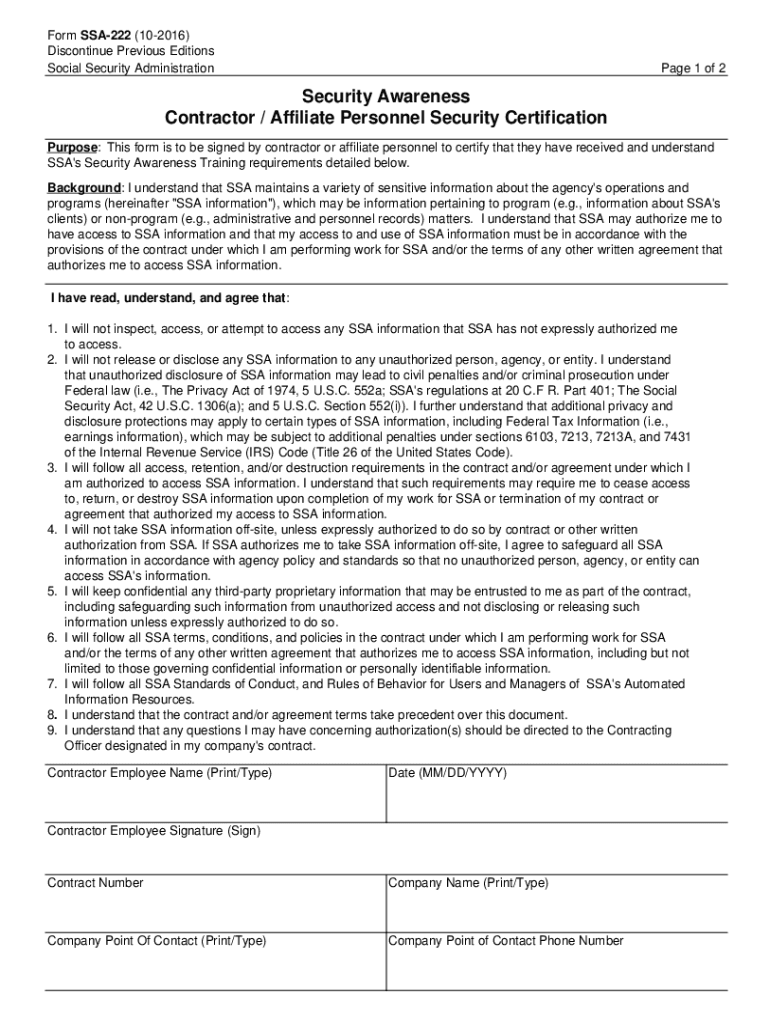
The "Security Awareness Contractor Personnel Security Certification" is a formal document that confirms an individual’s understanding and compliance with security awareness requirements for handling sensitive information, particularly within a governmental or corporate setting. It emphasizes the responsibilities of contractor personnel in maintaining confidentiality and protecting data integrity. This certification serves as a commitment to adhering to established security protocols and regulatory standards to mitigate risks associated with data breaches or unauthorized access.
How to Use the Security Awareness Contractor Personnel Security Certification
Contractor and affiliate personnel must complete and maintain this certification to affirm their understanding of security protocols. The form is typically used as part of an onboarding process or periodic re-certification exercise to ensure that all staff engaged in handling sensitive information are aware of their obligations. The certification involves reviewing guidelines, acknowledging comprehension, and agreeing to comply with security measures. Personnel may be required to provide this certification before accessing specific information systems or databases.
Steps to Complete the Security Awareness Contractor Personnel Security Certification
-
Read the Guidelines: Carefully review the security awareness training materials provided by your organization, focusing on confidentiality, information handling, and compliance issues.
-
Acknowledge Understanding: Ensure you fully understand the implications of the guidelines, including potential penalties for non-compliance and unauthorized disclosures.
-
Fill Out Personal Information: Enter your name, job title, and contact details accurately in the designated sections of the form.
-
Sign the Certification: Provide your signature to confirm your agreement to adhere to the security policies and procedures outlined in the training.
-
Submit the Form: Return the completed form to your organization’s security officer or designated personnel. This can often be submitted electronically through secure email platforms or document management systems.
-
Retain a Copy: Keep a personal copy for your records, which may be required for future reference or audit purposes.
Key Elements of the Security Awareness Contractor Personnel Security Certification
-
Personal Information: Includes fields for entering the participant’s name, role, and department within the organization.
-
Acknowledgment Statement: A section where individuals affirm their understanding and commitment to the security guidelines.
-
Legal Compliance: Details the legal framework and organizational policies that dictate security protocols.
-
Signature Block: Requires a dated signature from the personnel to finalize the certification process.
-
Instructional Guidance: Supplementary instructions on how to complete the certification correctly and any next steps post-submission.
Important Terms Related to the Certification
-
Confidentiality: The obligation to protect sensitive information from unauthorized access.
-
Data Breach: Unauthorized access or exposure of protected information, indicating a failure in security measures.
-
Compliance: Adherence to specified regulatory and security guidelines, often enforced through policy.
-
Security Protocols: Procedures and measures put in place to protect data integrity and prevent unauthorized access.
-
Training Requirements: Specific training that individuals must complete to be eligible for certification.
Legal Use of the Security Awareness Contractor Personnel Security Certification
This form is legally binding and integral to contracts or agreements with organizations that handle sensitive data. It serves to demonstrate that personnel have been adequately trained and acknowledge their responsibilities. Legal repercussions for failing to maintain certification can include termination of contracts, fines, or other disciplinary actions, depending on the severity of the breach.
Who Typically Uses the Security Awareness Contractor Personnel Security Certification
Primarily, this certification is used by contractors and third-party personnel working with organizations such as government agencies, healthcare providers, and corporations managing proprietary or sensitive information. It may also be applicable to consultants, temporary workers, and affiliates who have access to critical data systems.


Penalties for Non-Compliance
Failing to complete or comply with the certification requirements can lead to several penalties, including but not limited to the loss of data access privileges, suspension, or termination of contracts. Organizations might also face legal consequences, reputational damage, and potential financial liabilities if breaches occur due to non-compliant personnel.