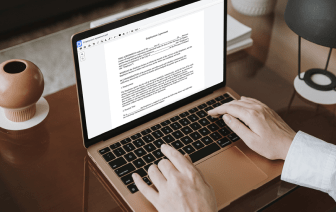
Whether you are already used to working with xht or managing this format for the first time, editing it should not feel like a challenge. Different formats might require specific software to open and modify them effectively. Yet, if you need to quickly strike result in xht as a part of your usual process, it is advisable to get a document multitool that allows for all types of such operations without the need of extra effort.
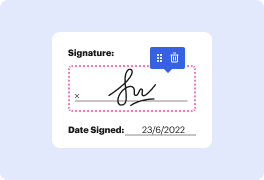
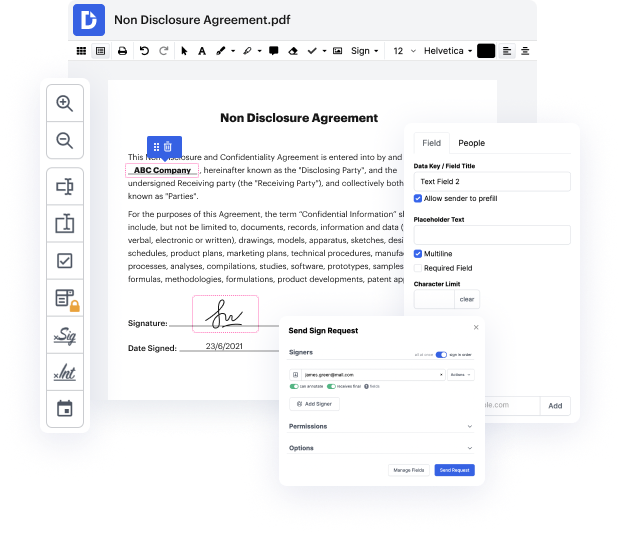
Try DocHub for sleek editing of xht and also other document formats. Our platform offers easy document processing regardless of how much or little prior experience you have. With tools you need to work in any format, you will not have to jump between editing windows when working with every one of your files. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You will just need to register a new DocHub account, and you can begin your work immediately.
See an improvement in document management efficiency with DocHub’s simple feature set. Edit any document easily and quickly, irrespective of its format. Enjoy all the advantages that come from our platform’s efficiency and convenience.
[Music] today were going to talk about cobalt strike why youre hearing so much about it in the news and what kind of detection opportunities it presents for you hi my name is dan brent im the cso of countercraft and im here talking with david barroso our ceo hi david hi how are you really good thanks okay so cobalt strike um why was it originally built by the security community david well i think ostek was created back in 2012 more or less uh by a security researcher in in the u.s but was more likely trying to replace metasploit metal protector starting with a visual wii so thats the initial origin of kobold sites so they wanted to have a visual or application for using metasploit but then of course they they detected that there was a good opportunity of improving many things that metapod was doing at the time okay so im a security researcher using cobalt strike and what is it im doing you know so called stack mainly is a post exploitation tool so usually use that after exploit