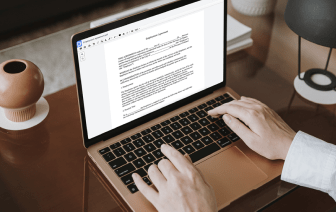
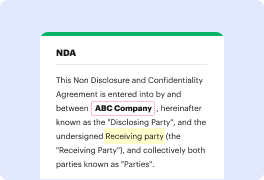
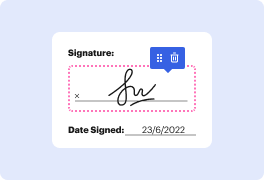
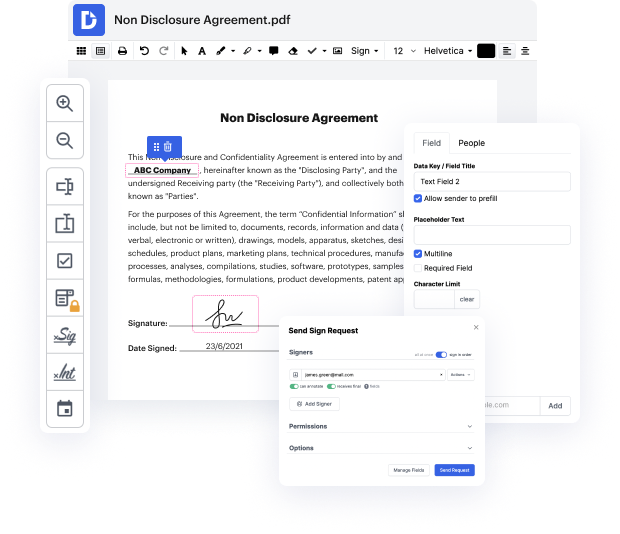
DocHub is an all-in-one PDF editor that allows you to strike authentication in ANS, and much more. You can highlight, blackout, or erase document fragments, add text and pictures where you need them, and collect information and signatures. And since it runs on any web browser, you won’t need to update your software to access its robust tools, saving you money. When you have DocHub, a web browser is all it takes to handle your ANS.
Log in to our service and follow these instructions:
It couldn't be simpler! Streamline your document management now with DocHub!
so all right continuing on our case study track um this is really going to be a really interesting one here so weamp;#39;ve got Dean perin from Fox Corporation I know your name oh here they come um and matot with serby here to talk to you about how fox has leveraged phot2 and the talk is called F2 Strikes Back so please letamp;#39;s welcome them to the stage awesome awesome awesome awesome thank you for coming today 74% of bdocHubes Target humans as the attack Vector 74% this means that only 26% of bdocHubes donamp;#39;t Target humans so if you want to reduce your risk of bdocHub secure the human letamp;#39;s look at two examples of recent attacks where humans are part of the attack lapsis and Scattered spider all right how many of you have heard of lapsis or scattered spider couple yeah how many of you had the pleasure of dealing with them nobody say nobody wants to raise their hand all right all right very cool I saw one hand I saw one um so yeah I mean lapsis wellknown for bdocHubes