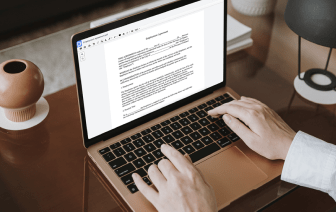
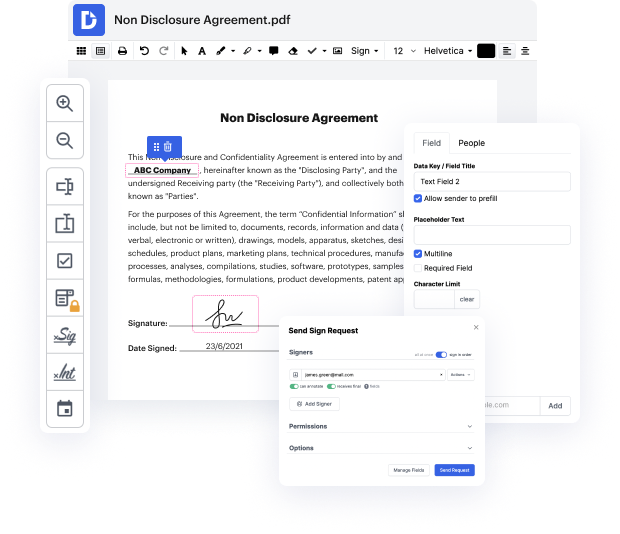
Picking out the perfect file administration solution for the business can be time-consuming. You must analyze all nuances of the platform you are thinking about, compare price plans, and stay aware with safety standards. Arguably, the opportunity to deal with all formats, including CWK, is vital in considering a platform. DocHub offers an extensive set of functions and tools to successfully deal with tasks of any complexity and take care of CWK format. Get a DocHub profile, set up your workspace, and begin working on your documents.
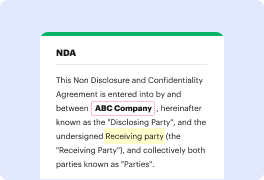
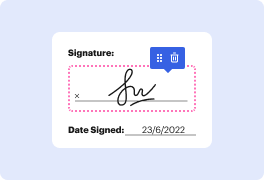
DocHub is a thorough all-in-one program that permits you to change your documents, eSign them, and make reusable Templates for the most frequently used forms. It provides an intuitive user interface and the opportunity to handle your contracts and agreements in CWK format in the simplified way. You don’t need to bother about reading countless tutorials and feeling stressed because the software is way too complex. link dent in CWK, assign fillable fields to designated recipients and collect signatures easily. DocHub is all about potent functions for experts of all backgrounds and needs.
Boost your file generation and approval operations with DocHub today. Enjoy all of this with a free trial version and upgrade your profile when you are all set. Modify your documents, create forms, and learn everything that you can do with DocHub.
[Music] [Applause] [Music] thank you [Music] okay so thank you I think that in the beginning Ill explain what WS link is oh okay can you hear me fine okay so WS link is uh interesting piece of malware that we like discovered and all of its samples were protected with an interesting virtual machine and our motivation to the obfuscate is for to see what is under the hood of this sample so in the beginning there werent any clear artifacts about we just suggest what the virtual machine was but after the publication of our paper several researchers docHubed out to us and told us that this is something which really looks like old virtualizer which is basically like the virtual machine used in temida and we afterwards like verified and confirm it so well talk like about code virtualizer and it should be fine because it was unpublicly described before as far as I know so I think that now Ill tell something about me so my name iska and Ive been working as a malware researcher at ESET since