It is usually difficult to find a platform that will deal with all your business demands or offers you correct tools to handle document creation and approval. Opting for an application or platform that includes crucial document creation tools that simplify any process you have in mind is essential. Even though the most widely used file format to work with is PDF, you need a comprehensive solution to manage any available file format, including xhtml.
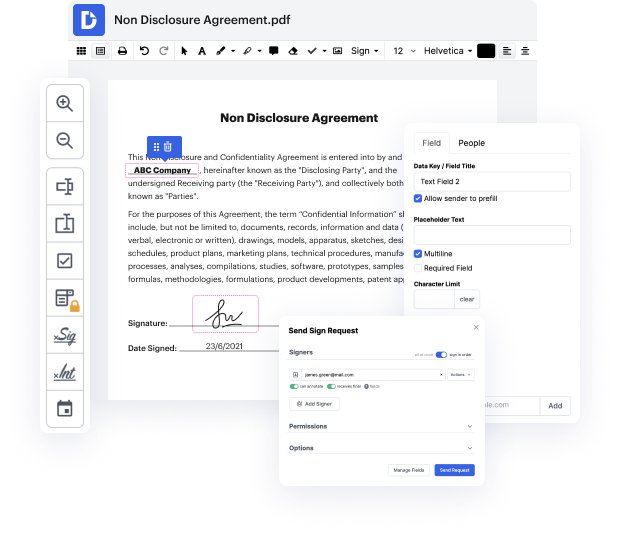
DocHub ensures that all your document creation demands are taken care of. Edit, eSign, turn and merge your pages based on your requirements with a mouse click. Deal with all formats, including xhtml, efficiently and quickly. Regardless of what file format you start working with, it is simple to convert it into a needed file format. Preserve tons of time requesting or looking for the proper file format.
With DocHub, you do not need extra time to get comfortable with our interface and modifying process. DocHub is an easy-to-use and user-friendly platform for any individual, even those without a tech education. Onboard your team and departments and change document managing for your company forever. inject header in xhtml, create fillable forms, eSign your documents, and have things done with DocHub.
Take advantage of DocHub’s comprehensive feature list and rapidly work with any document in every file format, which includes xhtml. Save time cobbling together third-party software and stick to an all-in-one platform to improve your day-to-day operations. Begin your cost-free DocHub trial right now.
hello in this lecture we are going to experiment with the HTTP header injection attack in cross-site scripting we inject the data into the contents of the HTTP response now we are going to do more or less the same but instead of injecting in the content we are going to inject in the HTTP response headers so lets go to the application which is called the test page so if you go to the target machine console you can see the URL there its VIP is the same as the others just it runs on port 8000 so lets load that part 8000 and make sure that perp is also running yes its running its intercepting as well so you could see that its a pretty simple test page if we call to perp we can go to history and and here is the request nothing interesting here is response also pretty simple just a few headers and and then a little HTML so this is a pretty simple page it doesnt really do anything it mostly just proves that the server is running but if you look closer in the response you could see tha