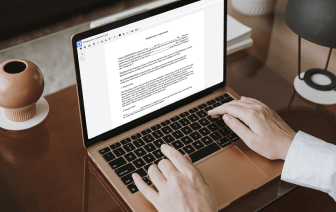
Choosing the perfect document administration solution for the organization might be time-consuming. You have to analyze all nuances of the platform you are thinking about, evaluate price plans, and stay aware with protection standards. Arguably, the ability to work with all formats, including QUOX, is crucial in considering a solution. DocHub provides an vast list of features and tools to ensure that you manage tasks of any complexity and handle QUOX format. Register a DocHub profile, set up your workspace, and begin dealing with your files.
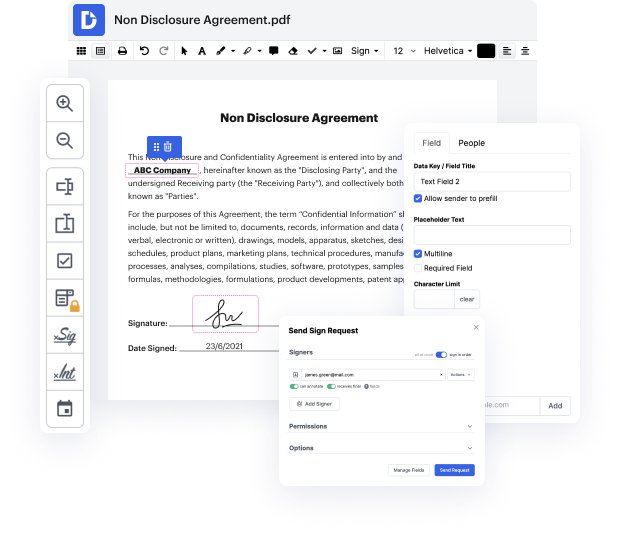
DocHub is a extensive all-in-one app that permits you to change your files, eSign them, and create reusable Templates for the most commonly used forms. It provides an intuitive interface and the ability to deal with your contracts and agreements in QUOX format in the simplified way. You don’t have to bother about studying numerous guides and feeling anxious because the software is way too sophisticated. inject header in QUOX, delegate fillable fields to specified recipients and collect signatures easily. DocHub is about potent features for specialists of all backgrounds and needs.
Improve your document generation and approval operations with DocHub today. Benefit from all this by using a free trial version and upgrade your profile when you are all set. Modify your files, make forms, and learn everything that you can do with DocHub.
hello in this lecture we are going to experiment with the HTTP header injection attack in cross-site scripting we inject the data into the contents of the HTTP response now we are going to do more or less the same but instead of injecting in the content we are going to inject in the HTTP response headers so lets go to the application which is called the test page so if you go to the target machine console you can see the URL there its VIP is the same as the others just it runs on port 8000 so lets load that part 8000 and make sure that perp is also running yes its running its intercepting as well so you could see that its a pretty simple test page if we call to perp we can go to history and and here is the request nothing interesting here is response also pretty simple just a few headers and and then a little HTML so this is a pretty simple page it doesnt really do anything it mostly just proves that the server is running but if you look closer in the response you could see tha