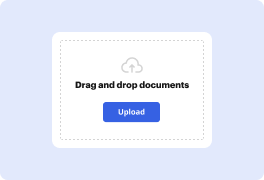
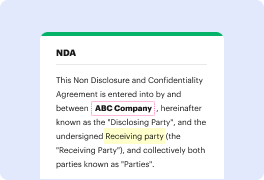
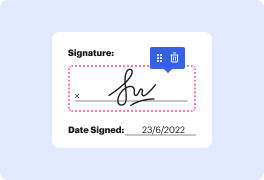
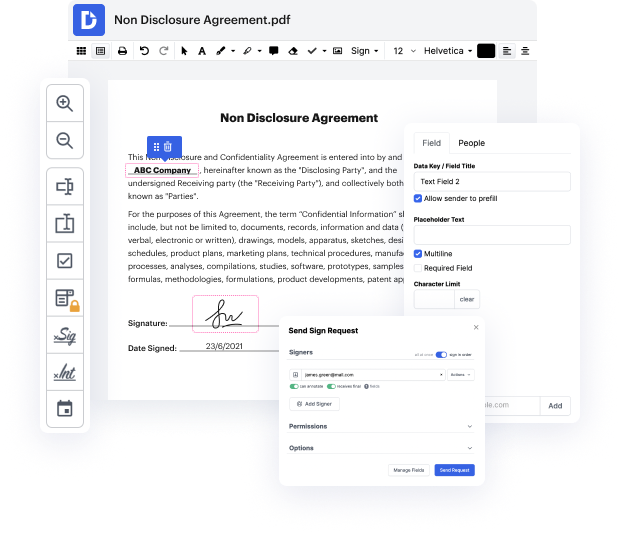
Are you having a hard time choosing a trustworthy solution to Exploit Application For Free? DocHub is set up to make this or any other process built around documents much easier. It's easy to navigate, use, and make changes to the document whenever you need it. You can access the essential tools for handling document-based workflows, like signing, importing text, etc., even with a free plan. Moreover, DocHub integrates with multiple Google Workspace apps as well as solutions, making file exporting and importing a breeze.
DocHub makes it easier to edit paperwork from wherever you’re. In addition, you no longer need to have to print and scan documents back and forth in order to sign them or send them for signature. All the vital tools are at your fingertips! Save time and hassle by completing paperwork in just a few clicks. Don’t wait another minute today!
This tutorial series by Ryan from Elevated Security will focus on using ExploitDB to download vulnerable software for security testing. The series will cover conducting security attacks and testing, particularly focusing on exploiting a Windows buffer overflow. Additionally, the tutorial will demonstrate various methods for leveraging the Windows OS for file transfers, providing value-packed content for viewers.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



