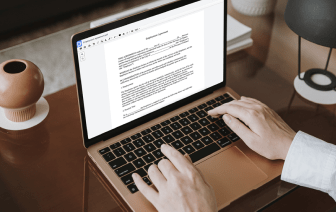
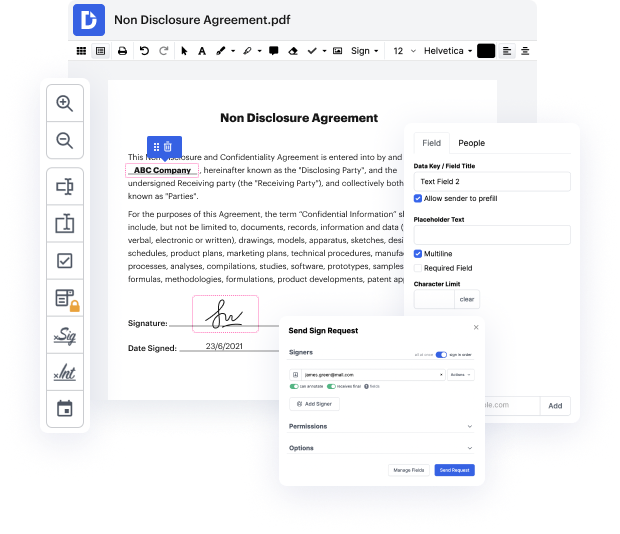
Browsing for a specialized tool that deals with particular formats can be time-consuming. Despite the huge number of online editors available, not all of them support OMM format, and definitely not all enable you to make adjustments to your files. To make matters worse, not all of them give you the security you need to protect your devices and documentation. DocHub is a perfect solution to these challenges.
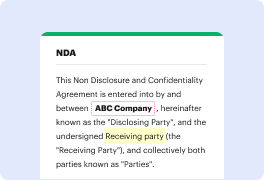
DocHub is a well-known online solution that covers all of your document editing needs and safeguards your work with bank-level data protection. It works with different formats, including OMM, and helps you edit such documents easily and quickly with a rich and intuitive interface. Our tool complies with essential security standards, like GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to guarantee the best user experience. With everything it provides, DocHub is the most trustworthy way to Cut ssn in OMM file and manage all of your individual and business documentation, irrespective of how sensitive it is.
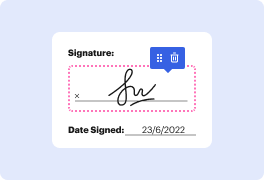
Once you complete all of your alterations, you can set a password on your edited OMM to ensure that only authorized recipients can open it. You can also save your document containing a detailed Audit Trail to see who applied what edits and at what time. Choose DocHub for any documentation that you need to edit safely. Sign up now!
hi were going to look at one of the most powerful hacking tools on the Internet today its the Google web search now you make me a promise when you watch this video that if you find anything that is sensitive information that you do not use it in an illegal manner so youll see what I mean as we go along so the website that we have in front of us here is called the Google hacking database its an open source project that you can get in many different websites but Im looking here at exploit dashdb.com now these are all different Google searches that will lead you to places that you did not know existed on the Internet people share data that they did not intend to and hackers use that data to find exploits and backdoors into systems where theyre not invited so let me show you where the secret lies for this type of hacking so Im going to google.com and doing a forward slash advanced underscore search so an advanced search allows you to find specific file names specific directories and