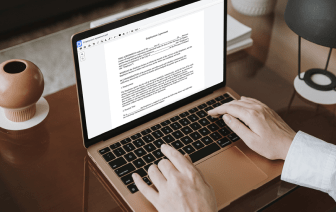
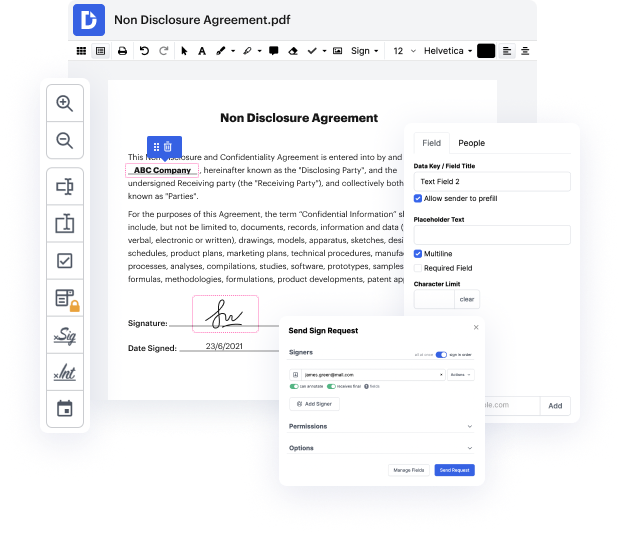
ACL may not always be the best with which to work. Even though many editing capabilities are available on the market, not all offer a straightforward tool. We developed DocHub to make editing straightforward, no matter the form format. With DocHub, you can quickly and effortlessly conceal authentication in ACL. On top of that, DocHub offers an array of other features including document generation, automation and management, field-compliant eSignature solutions, and integrations.
DocHub also lets you save effort by producing document templates from paperwork that you utilize frequently. On top of that, you can take advantage of our a wide range of integrations that enable you to connect our editor to your most used applications easily. Such a tool makes it quick and easy to deal with your documents without any delays.
DocHub is a handy feature for individual and corporate use. Not only does it offer a all-encompassing set of tools for document generation and editing, and eSignature integration, but it also has an array of capabilities that prove useful for developing complex and straightforward workflows. Anything imported to our editor is saved risk-free according to major industry standards that safeguard users' information.
Make DocHub your go-to choice and streamline your document-based workflows easily!
hello this is Edie from practical martinet welcome to a new video series where Iamp;#39;m going to teach you about access control lists this series is meant to be the last set of videos youamp;#39;ll ever have to watch to understand this concept this is the first video in the series where we will be answering the fundamental question what are access lists at its core an access control list is simply a tool you use to identify traffic how you apply the access list then determines what the access list is actually doing for example if you apply an axle issed to an interface then any traffic that is identified by your access list is being permitted through that interface this is the most common application of an ax list but there are many other use cases for a nexus for example if you apply an access list to a network address translation configuration then whatever traffic is identified by the X list is processed through a net if you apply an X list to a VPN configuration then whatever t