Definition of Confidential Information Management
Confidential information management refers to the protocols and practices employed to ensure personal and sensitive data is handled securely and discreetly. Organizations, such as DocHub, prioritize confidentiality by implementing robust systems that enhance client trust and comply with legal and ethical standards. Properly managing confidential information involves understanding what constitutes sensitive data, including personal identifiers, financial records, and proprietary business details.
- Types of Confidential Information:
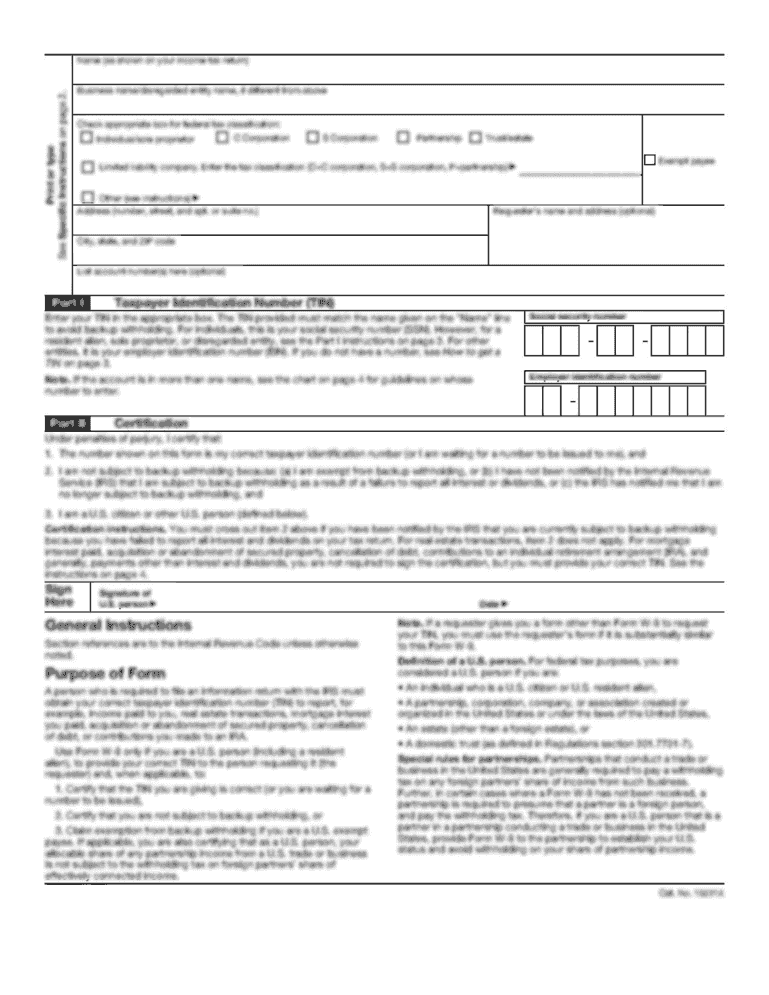
- Personal Identification Information (PII): Names, addresses, Social Security numbers
- Financial Data: Bank details, credit card numbers, income statements
- Corporate Secrets: Proprietary formulas, business strategies, client lists
Confidentiality emphasizes safeguarding this information from unauthorized access and potential breaches.
Security Protocols to Safeguard User Data
DocHub implements a range of security measures that are essential in maintaining the confidentiality of user information. Key protocols include:
- Encryption: All documents utilize 256-bit SSL encryption during transmission and storage. This high level of security ensures that any information exchanged is encrypted and cannot be accessed by unauthorized parties.
- Authentication: The use of OAuth 2.0 authentication provides secure access to user accounts, ensuring that only authorized individuals can view or alter confidential documents.
- Password Protection: Users can add password protection to sensitive documents. This feature mandates that recipients enter a password before accessing the document, adding an extra layer of security.
These measures demonstrate a commitment to protecting user-generated content and maintaining privacy.
Best Practices for Ensuring Confidentiality
To maximize the confidentiality of the information shared through DocHub, users can adhere to several best practices:
- Use Strong Passwords: Ensure that passwords are complex and changed regularly. Avoid commonly used passwords.
- Limit Document Sharing: Share documents only with intended recipients and utilize features such as setting permissions to control access levels.
- Regularly Monitor Access Logs: Review who has accessed documents and their changes to ensure no unauthorized alterations have been made.
These practices aim to cultivate a culture of security and responsibility among users.
Compliance with Legal Standards
Various legal frameworks dictate the handling of confidential information, particularly in the United States. DocHub complies with the ESIGN Act, ensuring that electronic signatures are legally binding. This legal backing is crucial for maintaining confidentiality and validity in transactions. Users should also be aware of:
- HIPAA (Health Insurance Portability and Accountability Act): Governs the protection of health information, ensuring confidentiality for healthcare providers and related organizations.
- FERPA (Family Educational Rights and Privacy Act): Ensures the confidentiality of student education records.
Understanding these regulations helps users ensure their practices align with national standards for confidentiality.
Document Flow and Information Security
Maintaining an effective document workflow is vital for ensuring the confidentiality of sensitive information. Through DocHub, users can manage documents securely in a streamlined fashion by:
- Importing from Secure Sources: Users can import documents directly from secure cloud storage services, ensuring documents remain confidential during transfers.
- Using Audit Trails: DocHub provides audit trails that log access to documents, allowing users to track who viewed or modified files. This transparency is critical for accountability and upholding confidentiality.
Such features enhance operational efficiency while prioritizing the security of confidential data.
Frequently Asked Questions on Confidential Information
Addressing common inquiries about confidentiality is important to alleviate concerns users may have regarding the security of their information. Questions such as "I assure you that the information you provided will be kept confidential" reflect user needs for clarity around confidentiality practices:
- How secure is my personal information?: DocHub ensures that all data is encrypted and protected against unauthorized access, with numerous security layers in place.
- What happens if my information is breached?: In the rare event of a security breach, DocHub is committed to notifying affected users and taking necessary corrective actions.
- Are electronic signatures really binding?: Yes, DocHub complies with legal standards set forth by the ESIGN Act, affirming the validity of electronic signatures.
Providing clear answers enhances user trust and fosters an environment of open communication regarding confidentiality.
Developing a Culture of Confidentiality
Fostering a culture of confidentiality within any organization or individual practice is crucial. This culture ensures that all users are aware of their responsibilities regarding data security:
- Training and Awareness: Educating users on best practices for managing confidential information sets the standard for an organization’s approach to security.
- Regular Policy Reviews: Frequent updates to privacy policies and training sessions help keep confidentiality at the forefront of organizational priorities.
By developing this culture, organizations ensure that the confidentiality of information remains a core value.
Continuous Improvement of Security Measures
To safeguard confidentiality in a rapidly changing digital landscape, continuous improvement of security measures is essential. DocHub stays updated on the latest security developments and compliance requirements, such as:
- Adopting New Technologies: Regularly updating encryption technologies to address emerging threats.
- User Feedback: Listening to user feedback to enhance features and security measures that prioritize confidentiality.
This commitment helps ensure that the information users provide will always be kept confidential, maintaining a secure and trustworthy document management environment.