Definition & Meaning
Understanding issues in cloud forensics involves examining the challenges and obstacles faced when conducting forensic investigations in cloud computing environments. This exploration addresses how traditional forensic methodologies must evolve to accommodate the unique characteristics of cloud services. Key areas include acquiring digital evidence, preserving its integrity, and maintaining the chain of custody. The cloud introduces complexities such as multi-tenancy, data dispersion across geographies, and dynamic scalability, all of which impact how forensic practitioners collect and analyze data. This context prompts improvements in both legal and technical frameworks to keep pace with technological advancements.
Key Elements of Cloud Forensics
Cloud forensics encompasses several key elements that differentiate it from traditional digital forensics.
- Evidence Collection: Involves identifying and gathering data from virtual machines, storage blobs, and network logs collectively held in cloud environments.
- Preservation: Focuses on ensuring that the evidence remains unchanged from the time it is collected until it is presented in court.
- Chain of Custody: Documenting each person who handled the evidence, the date and time it was collected, transferred, or modified, and its location.
These elements must adapt to the distributed nature of cloud infrastructure, where data could be stored in multiple physical locations managed by third-party service providers.
Steps to Complete Tasks in Cloud Forensics
Forensic investigations in the cloud require a structured approach to ensure effectiveness and compliance with legal standards.
- Initial Assessment: Determine the scope of the investigation and identify relevant data sources within the cloud.
- Data Acquisition: Select appropriate tools and methods to collect credible evidence without altering it.
- Analysis: Use forensic tools to examine the collected evidence, focusing on patterns that may indicate malicious activity.
- Reporting: Document findings in a comprehensive report that details the timeline, actions taken, and conclusions drawn from the investigation.
In each step, investigators face unique challenges owing to the cloud’s dynamic nature, which necessitates specialized skills and tools.
Legal Use and Compliance in Cloud Forensics
Legal considerations are fundamental in cloud forensics, as they govern how evidence is collected, stored, and processed.
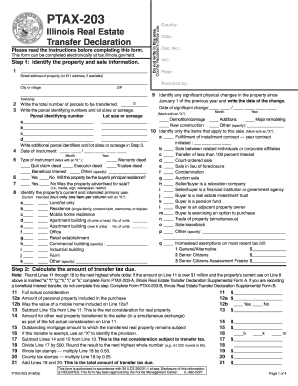
- Authorization: Secure legal access to cloud data, usually involving a warrant or legal agreement with the cloud service provider.
- Jurisdictional Challenges: Navigate laws from multiple regions due to the global distribution of data centers.
- Privacy Laws: Ensure compliance with regulations such as the General Data Protection Regulation (GDPR) or the California Consumer Privacy Act (CCPA) when handling personal data.
Understanding and navigating these legal landscapes is crucial to maintaining the admissibility of evidence in legal proceedings.
Who Typically Uses Cloud Forensics
Cloud forensics is utilized by various stakeholders in the cybersecurity and legal landscapes.
- Law Enforcement Agencies: Investigate cybercrimes that utilize cloud services.
- Corporate Security Teams: Protect organizational data from unauthorized access or breaches.
- Legal Professionals: Provide evidence in litigation concerning data breaches or intellectual property theft.
Each user group has distinct priorities but shares a need for rigorous forensic processes to effectively address incidents involving cloud environments.
Important Terms Related to Cloud Forensics
Several terms are central to understanding cloud forensics.
- Multi-Tenancy: Describes the sharing of resources among multiple customers within the same cloud environment.
- Virtualization: Refers to creating virtual instances of hardware or software resources in a cloud infrastructure.
- Elasticity: The ability of a cloud environment to automatically adjust resource allocation in response to current demands.
These concepts highlight the need for specialized forensic strategies capable of navigating the intricacies introduced by cloud architectures.
Examples of Using Cloud Forensics
Practitioners frequently encounter diverse scenarios requiring cloud forensic capabilities.
- Compromised Cloud Servers: Investigating unauthorized access or malware on servers hosted in the cloud.
- Data Theft: Tracing the exfiltration of sensitive data from a cloud-based storage system.
- Digital Fraud: Analyzing logs and transactions to uncover fraud perpetrated through cloud services.
These instances demonstrate the application of cloud forensic principles to real-world threats, underscoring their importance in contemporary cybersecurity efforts.
Software Compatibility for Cloud Forensics
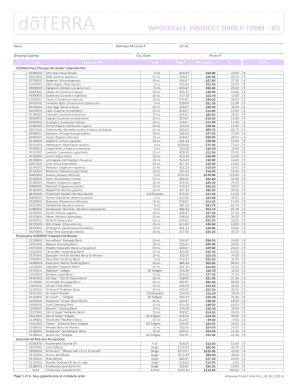
Cloud forensics requires tools compatible with cloud-based systems and services.
- EnCase and FTK: Widely used in traditional forensics but also have modules that handle cloud data.
- X1 Social Discovery: Investigates activities across social media platforms that may interface with cloud environments.
- AWS CloudTrail Logs: Specific to Amazon Web Services, provides forensic data on user activity across AWS resources.
The selection of tools depends on the specific requirements of the incident and the cloud platforms involved, emphasizing the need for versatility and breadth of expertise in forensic software.