Definition and Meaning of COMSEC Briefing
A COMSEC briefing, or Communications Security Briefing, is a crucial document provided to individuals who are granted access to sensitive communications security information. It explains the types and components of COMSEC information, emphasizing the importance of protecting this data. The briefing outlines specific responsibilities and regulations that must be adhered to in order to maintain the confidentiality and integrity of communication systems. This includes preventing the unauthorized disclosure of COMSEC material and ensuring compliance with legal and security protocols.
How to Use the COMSEC Briefing
The utility of a COMSEC briefing lies in its role as a guide for managing sensitive communication information. When using this briefing, individuals should carefully read and understand the outlined responsibilities and procedures. The briefing serves as an instructional tool, providing steps for handling COMSEC information safely. Users are encouraged to note the procedures for reporting security issues or vulnerabilities and to adhere to these protocols diligently. Practical examples within the document illustrate scenarios where these procedures may apply, helping users internalize and implement them effectively.
Steps to Complete the COMSEC Briefing
- Review the Document Thoroughly: Begin by reading the entire briefing to understand the scope and details of the security measures.
- Identify Key Responsibilities: Note the specific responsibilities assigned to you regarding the handling of COMSEC information.
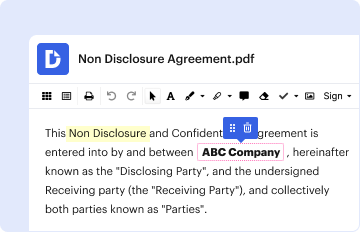
- Acknowledge Understanding: Often, there will be a section where individuals must acknowledge their understanding of the briefing.
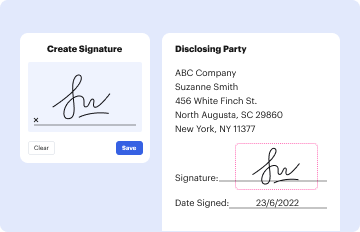
- Sign the Document: Provide a signature where requested, affirming your commitment to comply with the outlined responsibilities.
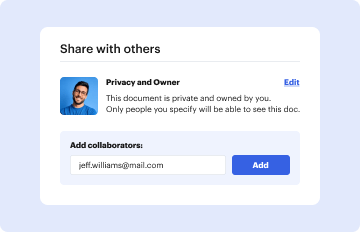
- Submit the Completed Briefing: Depending on the organization, the completed briefing may need to be submitted to a security officer or similar authority.
- Retain a Copy: Keep a personal copy for future reference to ensure ongoing compliance.
Key Elements of the COMSEC Briefing
- Types of COMSEC Information: The briefing details various categories of information to which the user may have access.
- Safeguarding Measures: Descriptions of measures necessary to protect sensitive information from unauthorized access or disclosure.
- Legal Consequences: It outlines potential legal implications for non-compliance with security measures.
- Handling and Reporting Protocols: Specifies the procedures for appropriately managing and reporting security threats or issues.
- Compliance Requirements: Highlights the necessity for adherence to all security practices and guidelines outlined in the briefing.
Who Typically Uses the COMSEC Briefing
This briefing is typically used by military personnel, government employees, contractors, and anyone else who is given access to sensitive communication security information. These individuals are often in roles involving the handling of protected communications technology or systems and are required to understand the implications of improper handling.
Legal Use of the COMSEC Briefing
The COMSEC briefing has legal weight, as it underscores federal and organizational regulations surrounding the use of sensitive communications information. Individuals who engage with COMSEC material must comply with all applicable laws, such as the protection of classified information under the Espionage Act. The briefing also highlights the legal repercussions of breaches, which can include penalties such as fines, imprisonment, or employment termination.
Penalties for Non-Compliance
Non-compliance with the guidelines in a COMSEC briefing can lead to various penalties, depending on the severity of the violation. Misuse or mishandling of sensitive COMSEC information could result in administrative actions, criminal charges, and even incarceration. It's critical for individuals with access to COMSEC information to comprehend these penalties to avoid inadvertent breaches of protocol.
Examples of Using the COMSEC Briefing
Real-world scenarios provide further clarity on how a COMSEC briefing is applied. For instance, in military operations, personnel are required to maintain confidentiality of radio communications and encryption keys. Another example is in government agencies where employees are trained to handle secure email transmissions and licensed software. These examples illustrate the daily applicability of COMSEC briefings and emphasize the critical nature of compliance for national security.