Definition & Meaning
The "Protection of Confidential Electronic Information Policy" is a crucial framework designed to safeguard sensitive electronic information. This policy defines the protocols and responsibilities involved in ensuring the protection of confidential data, especially within educational and organizational contexts, such as those practiced by California State University, Northridge (CSUN). It serves as a guideline for compliance with key regulations, maintaining data integrity and confidentiality, and preventing unauthorized access. By doing so, it plays a central role in data security management, which is pertinent for institutions managing vast amounts of sensitive data.
Key Elements of the Protection of Confidential Electronic Information Policy
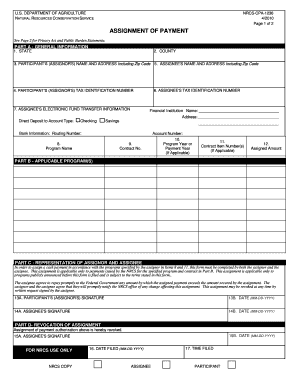
This policy incorporates several essential components to ensure the comprehensive protection of electronic information. It includes:
- Compliance: Adhering to regulations such as FERPA and local information security policies.
- Secure Data Handling and Storage: Implementing secure methods for storing and accessing sensitive data.
- Encryption: Requiring encryption for data transmission over networks to prevent data interception.
- Assigned Responsibilities: Designating roles within university personnel and IT departments to enforce security and manage data.
These critical elements collectively fortify the institution's capability to protect confidential information against potential security breaches.
Legal Use of the Protection of Confidential Electronic Information Policy
The enactment of this policy is pivotal in creating a legally compliant framework for safeguarding confidential information. It aligns with specific federal and state laws, ensuring that electronic information protection is consistent with legal requirements. Key legal aspects include:
- FERPA Compliance: Ensures that student educational records are kept confidential and secure.
- Data Privacy Laws: Adhering to laws such as the California Consumer Privacy Act (CCPA) and others applicable to data protection.
By aligning with these legal standards, institutions can minimize the risk of legal liabilities associated with data breaches or unauthorized disclosures.
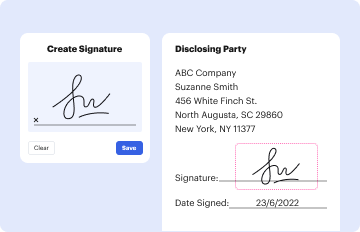
Steps to Complete the Protection of Confidential Electronic Information Policy
Implementing this policy involves a systematic approach, including:
- Assessment: Identify the types of data that require confidential handling.
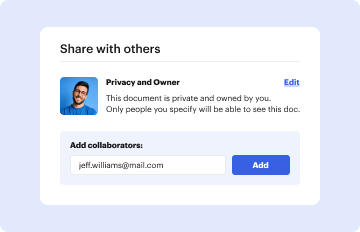
- Policy Dissemination: Distribute the policy to relevant stakeholders and ensure understanding.
- Training: Conduct training for personnel involved in data handling.
- Implementation: Enforce the policy through technological measures and procedural adjustments.
- Review and Audit: Regularly review the effectiveness of policy implementation and conduct audits to ensure compliance.
By following these steps, institutions can effectively align their practices with the policy's objectives.
Who Typically Uses the Protection of Confidential Electronic Information Policy
This policy is primarily used by educational institutions, particularly universities, and colleges managing substantial amounts of confidential student and faculty data. It is also applicable to:
- University Personnel: Ensures that faculty and staff handle sensitive information appropriately.
- IT Departments: Enforce security measures and safeguard data systems against unauthorized access.
- Administrative Departments: Manage information that requires confidentiality during inter-departmental processes.
Each of these groups plays a critical role in the successful implementation of the policy.

State-Specific Rules for the Protection of Confidential Electronic Information Policy
Different states may have specific regulations and requirements concerning the protection of electronic information. In California, for example, compliance with the California Consumer Privacy Act (CCPA) is imperative. It mandates additional protections for consumer data, which must be integrated into the institution's broader policy framework. Understanding and implementing these state-specific requirements ensures broader compliance and protection of confidential information.
Encryption and Secure Data Transfer
Encryption acts as the frontline defense in protecting confidential information from being intercepted during electronic transfers. The policy mandates the use of strong encryption protocols to secure sensitive data during:
- Network Transfers: Data sent over public networks must be encrypted to prevent unauthorized interception.
- Email Communication: Sensitive data shared via email should be encrypted to maintain confidentiality.
Employing robust encryption safeguards against potential breaches and conforms to legal data protection requirements.
Practical Scenarios and Examples of Using the Policy
The application of this policy can be observed in diverse scenarios:
- University Admissions: Ensuring that applicant data is securely handled and stored.
- Research Data Management: Protecting sensitive research data from unauthorized access or leaks.
- Student Records Management: Safeguarding student grades, history, and other personal information.
These examples illustrate the policy's role in preventing data breaches and maintaining the confidentiality of electronic information in various institutional processes.
Software Compatibility Considerations
Institutions implementing this policy must ensure that their systems are compatible with necessary security and compliance software, such as:
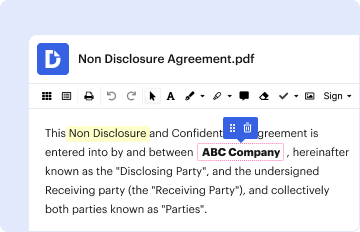
- Encryption Tools: Software that supports robust encryption methods.
- Compliance Management Systems: Tools that facilitate compliance with the policy’s requirements.
Compatibility with these software suites ensures a streamlined implementation of security protocols, aiding in the comprehensive protection of confidential information.