Definition & Meaning
A Sample Written Information Security Plan is a comprehensive document designed to outline how an organization protects its customers' non-public personal information. This plan encompasses various safeguards—administrative, technical, and physical—that ensure the confidentiality and security of sensitive data. The document serves as a blueprint for identifying potential threats, protecting against them, and implementing robust security measures. This plan is pivotal for businesses dealing with confidential customer data, as it provides a structured approach to information security management.
Key Elements of the Sample Written Information Security Plan
The Sample Written Information Security Plan contains several key components that are critical for effective data protection. Among these are:
- Objectives and Purposes: Clearly state the goals of the security plan, emphasizing the importance of protecting personal information.
- Administrative Safeguards: Outline the policies and procedures that govern data security, including roles and responsibilities.
- Technical Safeguards: Detail the technologies and tools used for data protection, such as encryption and network monitoring.
- Physical Safeguards: Describe measures to protect physical facilities and equipment from unauthorized access.
- Risk Assessment: Specify the process for identifying and evaluating potential security threats.
Each of these elements plays a crucial role in creating a robust framework for safeguarding personal data and ensuring compliance with applicable regulations.
Steps to Complete the Sample Written Information Security Plan
To effectively complete the Sample Written Information Security Plan, organizations should follow a structured approach:
- Identify Sensitive Information: Begin by cataloging all types of non-public personal information handled by the organization.
- Assess Risks: Conduct a thorough risk assessment to identify vulnerabilities in current data handling practices.
- Develop Policies: Create detailed security policies that address identified risks and outline procedures for data protection.
- Implement Safeguards: Apply necessary administrative, technical, and physical safeguards as described in the plan.
- Train Employees: Provide comprehensive training for staff to ensure they understand their role in maintaining data security.
- Monitor and Review: Establish regular monitoring and review procedures to assess the effectiveness of security measures and update them as needed.
By following these steps, organizations can ensure their information security plan is both comprehensive and effective.
Why Use a Sample Written Information Security Plan
A Sample Written Information Security Plan is essential for organizations that handle sensitive customer data. The plan:
- Enhances Data Protection: By standardizing security practices, organizations can better protect sensitive information from breaches.
- Ensures Regulatory Compliance: Helps businesses comply with data protection laws and regulations, reducing the risk of legal penalties.
- Builds Customer Trust: Demonstrating a commitment to data security can enhance an organization's reputation and build trust with customers.
- Facilitates Risk Management: Provides a structured approach to identifying and mitigating security risks.
Implementing such a plan demonstrates an organization's dedication to safeguarding its customers' personal information, which is increasingly important in today's digital age.
Legal Use of the Sample Written Information Security Plan
The legal implications of using a Sample Written Information Security Plan are significant. It helps ensure compliance with a range of laws and regulations designed to protect personal information, such as:
- Gramm-Leach-Bliley Act (GLBA): Requires financial institutions to explain their information-sharing practices and safeguard sensitive data.
- Federal Trade Commission (FTC) Regulations: Enforces measures to protect consumer privacy and prevent data breaches.
- State-Specific Data Protection Laws: Various states have their laws requiring businesses to protect residents' personal information.
Adhering to these legal requirements is crucial for avoiding penalties and maintaining operational legitimacy.
Who Typically Uses the Sample Written Information Security Plan
The Sample Written Information Security Plan is utilized by a wide range of businesses and organizations, particularly those in sectors that manage large volumes of personal data. Typical users include:
- Financial Institutions: Banks and credit unions need to safeguard their customers' financial information.
- Healthcare Providers: Medical organizations protect patient information under HIPAA regulations.
- Educational Institutions: Schools and universities protect student records and personal data.
- E-Commerce Businesses: Online retailers handle sensitive customer payment data and must ensure its security.
These organizations use such plans as a cornerstone of their data protection strategies.

Important Terms Related to Sample Written Information Security Plan
Understanding key terms related to the Sample Written Information Security Plan is crucial for effective implementation:
- Non-Public Personal Information (NPI): Information that is not publicly available and pertains to an individual's privacy.
- Data Breach: An incident where confidential information is accessed without authorization.
- Encryption: The process of converting data into a code to prevent unauthorized access.
- Authentication: Verifying the identity of a user who requests access to information.
- Access Control: Mechanisms that limit who can view or use resources in a computing environment.
Familiarity with these terms aids in comprehending and executing the security plan's provisions.
Examples of Using the Sample Written Information Security Plan
Practical applications of a Sample Written Information Security Plan can be seen across various sectors:
- Banking Industry: A bank implements encryption protocols and continuous monitoring systems as outlined in their security plan to protect customer transactions.
- Healthcare Sector: A hospital trains staff on data privacy policies and uses secure access controls to prevent unauthorized viewing of patient records.
- Retail Business: An online store utilizes multi-factor authentication for customer accounts, reducing the risk of data breaches.
These examples illustrate how organizations transform these plans into actionable strategies for data protection.
Software Compatibility
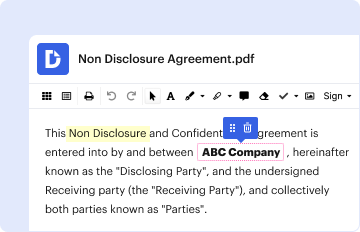
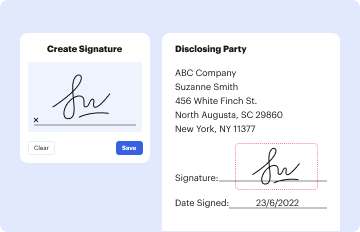
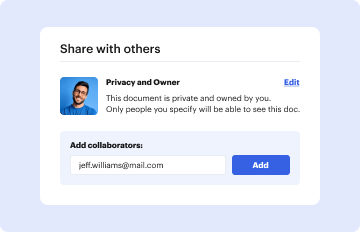
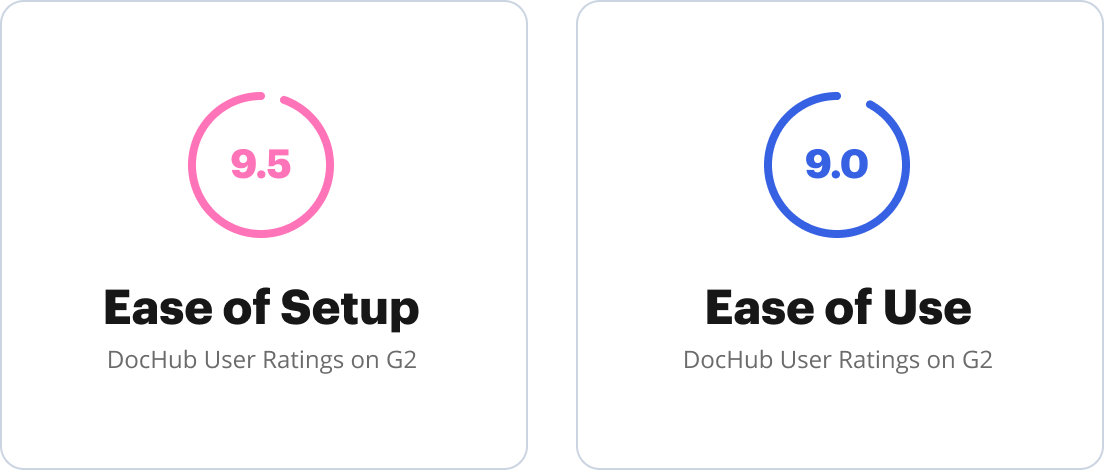
The form may be utilized alongside various software systems and platforms, such as:
- DocHub: Offers functionality for editing, signing, and sharing security plan documents.
- Google Workspace Integration: Allows for seamless document handling through Google Drive.
- Data Protection Tools: Incorporate additional software solutions like antivirus programs and firewall protection.
Software compatibility enhances the usability and effectiveness of the security plan, streamlining its implementation within organizational processes.