Definition and Meaning of a Digital Forensic Report
A digital forensic report is a detailed document that outlines the findings from a digital forensic investigation. This form is primarily used to record, analyze, and present digital evidence from various electronic devices. It plays a crucial role in investigating cyber crimes by providing a structured analysis of data recovery, including deleted or encrypted files, email correspondence, and other digital footprints. Each section of the report provides comprehensive insights into the methodologies and tools used to ensure data integrity and validity, which can be pivotal during legal proceedings.
Examples of Content in a Digital Forensic Report
- Case Background: Overview of the cyber crime being investigated.
- Evidence Collection Methods: Detailed description of how digital evidence was gathered.
- Analysis Techniques: Explanation of forensic tools and methods used to analyze data.
- Findings and Results: Summarized results of the investigation, such as retrieved files or detected anomalies.
- Conclusion and Implications: The final summary that relates findings to the case objectives.
How to Use a Digital Forensic Report
A digital forensic report serves several purposes depending on the user. For legal teams, it provides critical evidence to support a case in court. Investigators use it to outline procedural steps and methodologies that reaffirm the integrity and validity of their findings. Organizations may use these reports internally to understand security breaches and develop strategies to strengthen their IT infrastructure. Additionally, digital forensics professionals utilize these reports to enhance their understanding of forensic tools and techniques applicable to various case types.
Practical Scenarios for Report Usage
- Court Proceedings: To corroborate evidence presented in legal cases.
- Internal Audits: Organizations may review the report to identify weaknesses in data security protocols.
- Educational Purposes: The report can be studied by forensic students to understand case handling and evidence documentation.
Steps to Complete a Digital Forensic Report
Completing a digital forensic report involves a series of structured stages, each crucial for the accuracy and reliability of the final document.
- Initial Assessment: Define the scope of investigation, including the devices and data to be examined.
- Evidence Acquisition: Collect digital evidence while maintaining a documented chain of custody.
- Forensic Analysis: Utilize specialized software tools to analyze collected data.
- Result Documentation: Record findings in a detailed manner, ensuring clarity and comprehensiveness.
- Report Compilation: Organize data, analysis, and conclusions into a coherent format for presentation.
- Review and Verification: Cross-verify findings with case objectives and external sources, if necessary.
Key Considerations
- Accuracy: Ensure data presented is factual and supported by evidence.
- Clarity: Use clear language to avoid ambiguity, making it understandable to non-technical stakeholders.
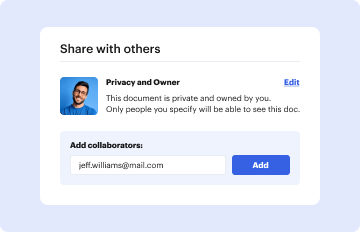
- Confidentiality: Sensitive information must be handled in compliance with legal and organizational guidelines.
Key Elements of a Digital Forensic Report
Digital forensic reports are often complex, containing numerous elements essential for thorough documentation. Understanding these elements is critical for any professional involved in the creation or interpretation of digital forensic reports.
Common Components
- Executive Summary: A brief overview of the investigation and key findings.
- Technical Details: In-depth information on the tools and procedures used.
- Appendixes: Supplementary materials, such as logs or code samples.
- Recommendations: Suggested actions based on the findings, often used for mitigating future risks.
Significance of Each Element
- Executive Summary: Helps decision-makers quickly assess the report's relevance and urgency.
- Technical Details: Provides transparency and facilitates accuracy verification.
- Recommendations: Serves as a guideline for addressing identified issues and preventing reoccurrences.
Legal Use of Digital Forensic Reports
In the context of the United States, digital forensic reports are often subject to legal standards that ensure their admissibility in courts. This includes following proper protocols during data collection and analysis to maintain the evidence's integrity and prevent tampering claims.
Legal Considerations
- Admissibility: Reports must be prepared according to established legal frameworks to be considered valid in court.
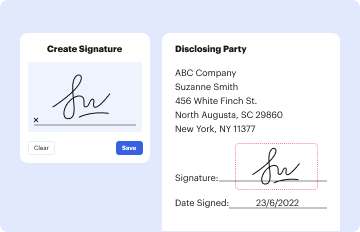
- Compliance: Adherence to laws such as the ESIGN Act ensures that electronically signed reports are legally binding.
- Confidentiality Laws: Experts must be aware of laws concerning the handling and disclosure of digital evidence.
Who Typically Uses Digital Forensic Reports
Digital forensic reports are used by a wide range of professionals who require detailed digital evidence documentation for various purposes.
Typical Users
- Law Enforcement Agencies: For criminal investigation and prosecution purposes.
- Legal Professionals: To present evidence in court and support litigation cases.
- Corporate Security Teams: To investigate and respond to internal breaches and cybersecurity threats.
Obtaining a Digital Forensic Report
To obtain a digital forensic report, it is often necessary to engage with a qualified digital forensics expert or organization possessing the necessary tools and expertise to perform the investigation. These reports can be commissioned by:
- Legal Entities: To support ongoing investigations or cases.
- Private Individuals: When faced with personal cybersecurity issues.
- Organizations: For internal audits or to investigate data breaches.
Steps to Request a Report
- Identify the Need: Clarify why the report is required and what specific questions it needs to answer.
- Engage with Experts: Contact certified professionals or forensic companies to discuss terms and scope.
- Provide Relevant Data: Supply necessary documents or devices for the investigation.
- Review Drafts: Collaborate with practitioners to finalize the report, ensuring all necessary data is included and correctly interpreted.