Definition and Meaning of the Threat Assessment Template
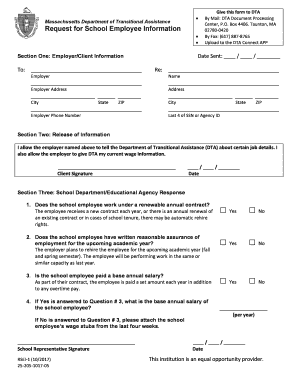
A threat assessment template is a structured document used by organizations, especially in educational settings, to evaluate and respond to potential threats. It provides a standardized approach to assess situations where a person may pose a threat to themselves or others. The template helps in documenting observations, evaluating the severity of the threat, and determining appropriate interventions. The aim is to prevent harmful incidents by adopting a methodical and informed response strategy. A comprehensive understanding of this template is crucial in ensuring safety and compliance with institutional protocols.
Key Elements of the Threat Assessment Template
The threat assessment template is comprised of several critical elements that enable thorough evaluation and documentation:
- Identification of Threat: Includes details about the individual posing the threat, the nature of the threat, and circumstances under which it was identified.
- Assessment of Severity: Categorizes the level of threat as transient, serious substantive, or very serious substantive, based on the specific criteria established by the template.
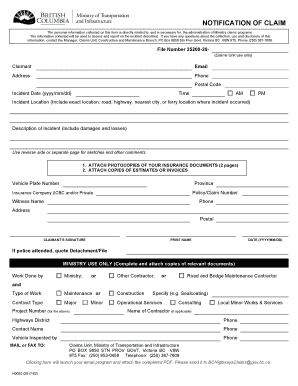
- Documentation of Incident: Provides a section for recording the details of the incident, including time, date, and location.
- Intervention Plan: Outlines the immediate and long-term actions to be taken by the institution or organization.
- Follow-up and Monitoring: Ensures there is a procedure in place for ongoing review of the situation and effectiveness of interventions implemented.
Steps to Complete the Threat Assessment Template
- Gather Information: Begin by collecting all relevant information about the incident and individual involved. This includes observations, witness statements, and any pertinent background data.
- Identify the Nature of the Threat: Clearly document what the threat entails—whether it is verbal, behavioral, or implied.
- Evaluate the Severity: Use the pre-defined criteria within the template to determine the threat level.
- Initiate an Immediate Response: Develop an initial intervention plan based on the severity identified. This might involve notifying law enforcement, school security, or initiating mental health support.
- Prepare a Long-Term Plan: Beyond immediate responses, plan for long-term management and support.
- Conduct Follow-ups: Schedule regular follow-ups to assess the situation and adjust interventions as needed.
Who Typically Uses the Threat Assessment Template
The primary users of a threat assessment template are educational administrators, security personnel, and mental health professionals. Schools often have dedicated teams comprising counselors, teachers, and law enforcement officers who utilize these templates to ensure student safety. Additionally, businesses with high-risk environments or significant public interaction may employ such templates to safeguard their premises and personnel. Understanding the roles and responsibilities of these professionals is key to properly implementing the threat assessment process.

Important Terms Related to Threat Assessment Template
- Transient Threat: A threat that is not intended to be carried out, often the result of an outburst or statement made in anger.
- Substantive Threat: A credible threat that requires active intervention due to its seriousness.
- Intervention Plan: A set of actions designed to neutralize a threat, provide support to the involved parties, and ensure the ongoing safety of the community.
- Confidentiality: Ensures that all personal information and assessment results are protected and shared only with authorized personnel.
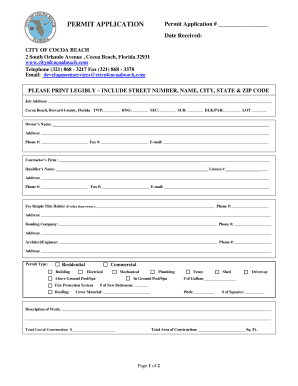
Legal Use of the Threat Assessment Template
The legal framework surrounding the use of threat assessment templates often involves privacy laws and duty of care obligations. Users must ensure all procedures are compliant with regional laws, such as FERPA in the educational sector in the United States. Moreover, users must balance legal requirements for confidentiality with their duty to prevent harm. Underpinning these requirements is the necessity for thorough documentation and responsible information sharing among key stakeholders when assessing threats.
Examples of Using the Threat Assessment Template
Consider a situation in a school where a student makes a threatening statement during class. School officials would utilize the threat assessment template to:
- Record the incident details and initial teacher testimonies.
- Assess the student's behavior history and any contextual factors.
- Plan interventions including parental notification and counseling sessions.
- Review and update their approach based on subsequent information and developments over time.
Another example could involve a corporate environment where an employee exhibits potentially harmful behavior, prompting HR and security to use the template for evaluating the risk and determining next steps for everyone’s safety.
State-Specific Rules for the Threat Assessment Template
While the threat assessment template provides a general framework, state laws may dictate specific procedures and reporting obligations. Differences can include:
- Mandatory Reporting Requirements: Some states require certain threats to be reported to law enforcement or other authorities regardless of their perceived severity.
- Documentation and Retention Protocols: States may have varying rules on how long threat assessment documentation must be retained and who can access these records.
- Training and Education Standards: Variations exist in terms of required training for staff completing the assessments.
Familiarity with state-specific rules ensures that threat assessments are conducted legally and effectively, supporting the ultimate goal of preserving safety and preventing harm.