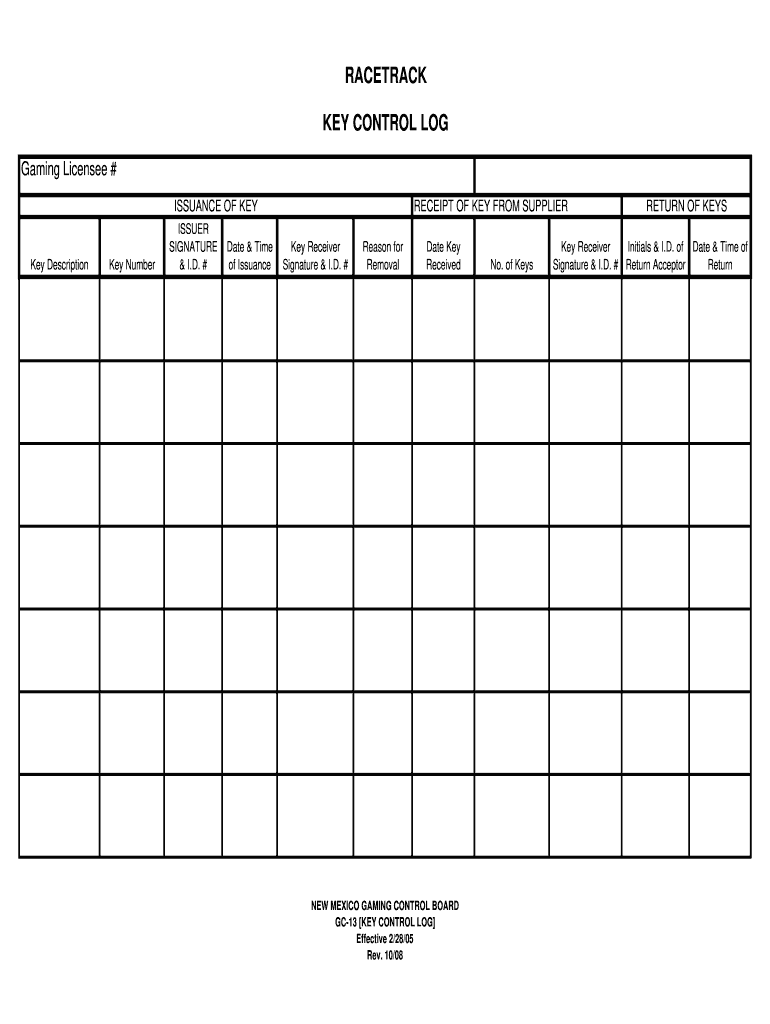
Definition and Importance of a Key Log Sheet
A key log sheet is a crucial document used for tracking the issuance, receipt, and return of keys within an organization. This log helps maintain an accurate inventory of keys, ensuring accountability and safeguarding against unauthorized access. A well-structured key log sheet typically includes various essential components such as key descriptions, issuer details, recipient information, and reasons for the removal of keys.
- Definition: The key log sheet serves as a formal record that documents who has been issued which key, when it was issued, and when it must be returned.
- Purpose: It plays a significant role in enhancing security protocols by monitoring key access and usage, thus preventing loss or theft.
Understanding the purpose and mechanisms of a key log sheet is fundamental for businesses that rely on physical access control.
Key Elements of a Key Log Sheet
Understanding the format and elements of a key log sheet is essential for effective management of keys in any organization. The following elements are commonly found in a comprehensive key log sheet:
- Key Description: This includes a unique identifier or name for each key, helping distinguish between different keys within the organization.
- Issuer Information: Details about the individual or entity responsible for issuing the key, including their name and position.
- Recipient Information: Information on the person receiving the key, often requiring them to sign or acknowledge receipt.
- Date Issued: The exact date when the key was handed over to the recipient.
- Return Date: A specified date by which the key should be returned, if applicable.
- Reason for Removal: Documentation of why the key is being issued or if a key is being replaced, such as loss or damage.
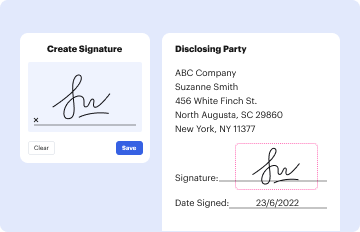
- Signatures: Areas for both the issuer and recipient to sign, ensuring both parties acknowledge the transaction.
Using these elements helps maintain accountability and a clear record of key distribution within an organization.
How to Use the Key Log Sheet Effectively
Using a key log sheet effectively involves following a clear procedure to ensure all keys are tracked properly. Here are the essential steps to utilize a key log sheet:
- Initiate the Log: Start by creating a master key log sheet, ensuring all necessary fields are included for proper documentation.
- Issuance of Keys: When issuing keys, fill out the required information in the sheet meticulously, making sure the recipient provides their signature.
- Regular Updates: Consistently update the log to reflect real-time changes; if a key is returned, mark it as such, including the date.
- Review Procedures: Implement routine checks to reconcile keys against the log, ensuring all issued keys are accounted for and there are no discrepancies.
- Retention of Logs: Keep records of key logs for a defined duration, as per organizational policies, which may help in audits or investigations.
Establishing clear protocols for using the key log sheet is fundamental to preserving security and monitoring access.
Examples of Using Key Log Sheets in Various Settings
Key log sheets can be employed across multiple scenarios, reflecting various settings where access control is vital. Here are some practical examples:
- Educational Institutions: Schools may use key log sheets to track keys to classrooms, administrative offices, and storage closets, ensuring that staff members are accountable for access to secured areas.
- Corporate Offices: In a corporate environment, key log sheets can manage access to IT rooms, file cabinets, or sensitive areas, documenting who has access and preventing unauthorized entry.
- Residential Complexes: Property management companies often utilize key log sheets to monitor which maintenance personnel have keys to units, ensuring that access is limited to authorized individuals only.
- Event Venues: For venues hosting multiple events, key log sheets facilitate the tracking of keys for storage areas, stages, or equipment rooms used by different teams.
These examples highlight the functional versatility of key log sheets across various organizations, underscoring the importance of careful key management.
Important Terms Related to Key Log Sheets
Understanding specific terminology related to key log sheets enhances clarity and communication. Here are several key terms that are frequently associated with key management:
- Key Control: A method of governing the distribution, access, and inventory of keys to ensure they are utilized responsibly.
- Access Control: The process of restricting access to certain areas or items within a facility, often linked with physical keys or electronic access systems.
- Accountability: Establishing responsibility for key issuance and return; critical in preventing unauthorized access.
- Audit Trail: A documented history of actions regarding key management, providing a reference for both security and compliance purposes.
Familiarity with these terms helps individuals and organizations effectively communicate about key management and security protocols.
Who Typically Uses the Key Log Sheet
Key log sheets are utilized by a wide array of professionals across different industries. Here’s an overview of typical users:
- Facility Managers: Responsible for overseeing access to buildings and sensitive areas, they use key log sheets to maintain security protocols.
- Administrative Staff: Often in charge of issuing keys to employees or contractors, ensuring that records are accurately kept.
- Security Personnel: Monitoring key access helps security teams safeguard sensitive areas by tracking who has access at any given time.
- Maintenance Teams: Require keys for regular access to various areas; thus, keeping track of their key usage is essential for operational efficiency.
- Property Managers: Responsible for managing residential or commercial properties, they utilize key log sheets to ensure that all access points are secure.
These professionals rely on key log sheets to maintain security standards and enhance operational workflows in their respective environments.