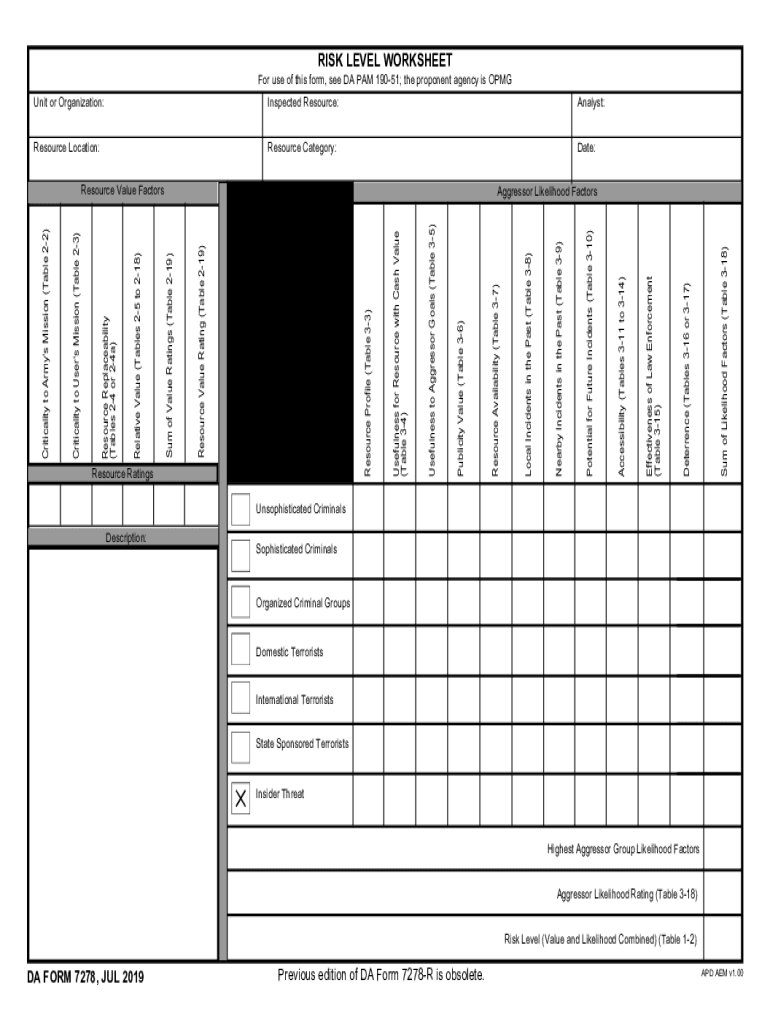
Understanding the DA Form 7278
The DA Form 7278 is a crucial risk assessment document utilized primarily within the military to analyze potential threats and evaluate the effectiveness of law enforcement resources. This form is integral to assessing various aspects of security risk, including deterrence levels, accessibility, and previous incidents. It plays a vital role in both individual unit assessments and broader Army mission planning.
Comprehensive Use of the DA Form 7278
The DA Form 7278 serves multiple purposes, including the identification and measurement of potential risks associated with military resources. By filling out this form, one can systematically evaluate threat levels and resource vulnerabilities. This process aids military personnel in making informed decisions regarding resource allocation and protective measures.
Practical Application Scenarios
- Threat Analysis: Assess potential external threats based on past incidents and current security intelligence.
- Resource Evaluation: Determine the effectiveness of existing law enforcement resources and identify areas for improvement.
- Strategic Planning: Utilize the form for creating comprehensive security plans that align with both unit-specific and larger Army goals.
Steps to Complete the DA Form 7278
Filling out the DA Form 7278 involves a structured approach to ensure accuracy and thoroughness. Below is a step-by-step guide on how to complete this essential form.
- Gather Required Information: Collect data on existing threats, past incidents, and resource effectiveness before starting.
- Complete the Identification Section: Fill in details about the unit or facility being assessed.
- Analyze Deterrence Factors: Evaluate current deterrence measures and their effectiveness.
- Assess Accessibility Risks: Identify and document how easily resources can be accessed by potential aggressors.
- Document Past Incidents: Record any relevant historical data on security breaches or threats.
- Analyze Likelihoods: Use gathered data to assess the likelihood of potential threat scenarios.
Key Elements of the DA Form 7278
The DA Form 7278 includes various critical sections, each designed for thorough analysis of security threats. Understanding these elements is crucial for accurate completion.
- Threat Analysis Tables: Detailed tables that guide through the risk evaluation process.
- Resource Rating Metrics: Metrics used to determine the value and vulnerability of resources.
- Deterrence Assessment: Sections evaluating the effectiveness of current deterrent measures.
Who Commonly Uses the DA Form 7278
While the primary users of the DA Form 7278 are military personnel involved in security and law enforcement, it is also relevant to various government agencies responsible for national security tasks.
- Military Units: Employed by individual units for localized risk assessments.
- Security Analysts: Used by analysts for broader threat evaluations.
- Resource Managers: Vital for decision-makers overseeing resource protection strategies.
Legal Considerations in Using the DA Form 7278
The DA Form 7278 must be used in compliance with military guidelines and standards. It holds significant legal importance as it informs strategic decisions impacting national security.
Important Legal Aspects
- Confidentiality: Ensure all data recorded on the form is handled with strict confidentiality.
- Accuracy and Honesty: Information provided must be accurate and truthful to maintain its legal integrity.
- Regulatory Compliance: Adhere to all relevant military regulations when completing and submitting the form.
Obtaining the DA Form 7278
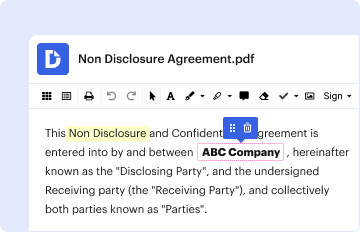
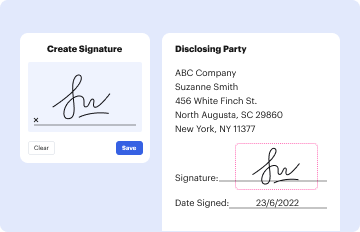
The DA Form 7278 can be accessed through official military channels and platforms that provide editable and printable versions. The form can also be filled out and signed digitally using tools like DocHub, which offers secure and efficient means to manage such documents.
Accessing the Form
- Military Websites: Available for download from secure military or government portals.
- DocHub Platform: Utilize DocHub to complete and sign the form securely online.
Security and Encryption with Digital Forms
When using digital versions of the DA Form 7278, security is paramount. Tools like DocHub provide 256-bit SSL encryption, ensuring data protection during transfer and storage, making it a secure option for handling sensitive information related to the form.
Security Features
- Encryption: 256-bit SSL encryption for maximum data protection.
- Authentication Protocols: OAuth 2.0 for secure user access.
- Password Protection: Additional layer of security when sharing documents.