Definition and Meaning
Publication 5433 (SP) (7-2020) - Internal Revenue Service is a resource designed for tax professionals, focusing on safeguarding taxpayer information. This publication details the protocols necessary for protecting sensitive data, especially from phishing scams that exploit situations like COVID-19. The document provides insight into recognizing fraudulent communications and implementing 'trusted client' policies to ensure secure interaction with clients.
Importance of Data Protection
- Phishing Scams: The document stresses the need to identify phishing emails that often mimic legitimate sources and carry a sense of urgency to deceive recipients.
- Trusted Client Policies: Tax professionals are advised to develop policies that ascertain the authenticity of client communications and protect against data breaches.
How to Use Publication 5433 (SP) (7-2020) - Internal Revenue Service
The publication serves as a guideline for implementing secure data handling practices. Users should follow these protocols:
- Review Security Guidelines: Understand and apply the recommended strategies for data protection mentioned within the publication.
- Identify Phishing Indicators: Educate yourself and your team on identifying signs of fraudulent emails and communications.
- Report Suspicious Activity: Utilize the guidelines to report any identified phishing attempts directly to the IRS.
Steps to Complete Processes Within Publication 5433 (SP) (7-2020) - IRS
The document outlines steps necessary to secure taxpayer data effectively:
- Establish Protocols: Set up clear guidelines within your practice or organization to deal with potential phishing scams.
- Training for Staff: Conduct training sessions for staff to familiarize them with the signs of phishing and the necessary actions to take.
- Implementation of Technology Solutions: Use secure software and platforms that comply with the guidelines stipulated in the publication.
Key Elements of Publication 5433 (SP) (7-2020)
Critical components include:
- Identification and Reporting: Procedures for recognizing and reporting phishing scams.
- Data Security Protocols: Practical steps for maintaining secure networks and communication channels.
- Compliance with IRS Recommendations: Conformance to IRS-endorsed security measures for taxpayer data protection.
Legal Use of the Document
Tax professionals must adhere to the legal guidelines outlined in the publication to avoid penalties and ensure compliance with federal regulations. The publication emphasizes the importance of these procedures in preventing unauthorized access to confidential taxpayer information.
Who Typically Uses the Publication 5433 (SP) (7-2020)
The primary users include:
- Tax Professionals: Accountants and tax preparers seeking to secure their practice and protect client information.
- Tax Firms: Organizations aiming to implement a robust security framework.
- Compliance Officers: Individuals responsible for aligning business practices with IRS requirements.
Examples of Using Publication 5433 (SP) (7-2020)
Real-world scenarios include:
- Implementing Secure Email Systems: A tax firm enhances its email security following publication guidelines.
- Training Modules for Staff: An organization conducts workshops to improve staff awareness of potential security threats.
- Auditing Security Measures: Regular audits are implemented to ensure ongoing compliance with IRS standards.
IRS Guidelines and State-Specific Rules
While Publication 5433 (SP) provides federal guidelines, tax professionals should also be aware of state-specific rules that may influence their practices. Each state may have additional compliance requirements that organizations need to meet to ensure they do not encounter legal issues.
Compliance with IRS Guidelines
- Confidentiality: Ensure strict confidentiality in all communications and data handling.
- Integrity: Maintain accurate and unalterable records as required by federal law.
- Availability: Ensure that authorized parties have access to necessary data while preventing unauthorized access.
Required Documents for Compliance
Professionals must maintain proper documentation to demonstrate compliance with the publication’s guidelines. Essential documents include:
- Security Audit Records: Documentation of security audits conducted within the organization.
- Training Logs: Records of training sessions provided to staff regarding data protection and phishing identification.
- Compliance Certifications: Any certificates or documentation that demonstrate adherence to IRS recommendations.
Form Submission Methods and Software Compatibility
Publication 5433 (SP) does not require direct submission; however, it influences how other related forms are handled, typically through the following methods:
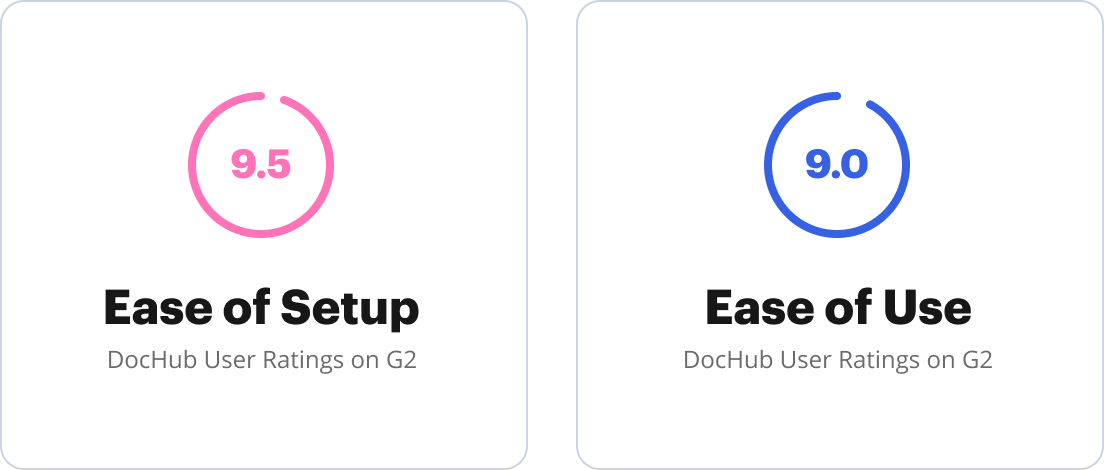
- Online Platforms: Use of secure software such as TurboTax or QuickBooks for digital submissions.
- Compatible Software: Ensure compatibility of security protocols with existing accounting software systems for seamless integration.
Penalties for Non-Compliance
Failure to follow the guidelines outlined in Publication 5433 (SP) can result in:
- Legal Repercussions: Potential lawsuits due to mishandling confidential information.
- Financial Penalties: Fines imposed by the IRS for failing to protect taxpayer data adequately.
- Reputational Damage: Loss of client trust resulting from data breaches or unauthorized disclosures.
Conclusion
Through comprehensive coverage of data protection strategies, Publication 5433 (SP) serves as a crucial resource for tax professionals. The guidelines ensure that organizations stay compliant with IRS requirements and protect sensitive taxpayer information from cyber threats.








